Install Roundcube Webmail on CentOS 8/RHEL 8 with Apache/Nginx
Roundcube is a free open source, full-featured webmail client written in PHP. A webmail is a mail client in your browser, which means instead of reading and sending emails from a desktop mail client like Mozilla Thunderbird, you can access your email from a web browser. This tutorial is going to show you how to install Roundcube webmail on CentOS 8/RHEL 8 with Apache or Nginx web server.
Roundcube Features
Roundcube functionality includes:
- Address book
- Folder management
- Message searching
- Message filter
- Spell checking
- MIME support
- PGP encryption and signing
- Mailvelope integration
- Users are able to change their passwords in Roundcube.
- Import MIME or Mbox formatted emails.
- Email Resent (Bounce)
- Support for Redis and Memcached cache
- Support for SMTPUTF8 and GSSAPI
- A responsive skin called Elastic with full mobile device support
- OAuth2/XOauth support (with plugin hooks)
- Collected recipients and trusted senders
- Full Unicode support with MySQL database
- Support of IMAP LITERAL- extension
Prerequisites
To follow this tutorial, it’s assumed that
- Postfix SMTP server and Dovecot IMAP server have been installed on your CentOS 8/RHEL 8 server
- You have already installed a LAMP stack or LEMP stack on CentOS 8/RHEL 8 server.
If not, please click the above links and follow the instructions to complete prerequisites. Now let’s proceed to install Roundcube.
Step 1: Download Roundcube Webmail on CentOS 8/RHEL 8
Log in to your CentOS/RHEL server via SSH, then run the following command to download the latest 1.4.9 stable version from Roundcube Github repository.
wget https://github.com/roundcube/roundcubemail/releases/download/1.4.9/roundcubemail-1.4.9-complete.tar.gz
Note: You can always use the above URL format to download Roundcube from command line. If a new version comes out, simply replace 1.4.9 with the new version number. You can check if there’s new release at Roundcube download page.
Extract the tarball, move the newly created folder to web root (/var/www/) and rename it as roundcube at the same time.
tar xvf roundcubemail-1.4.9-complete.tar.gz sudo mkdir /var/www/ sudo mv roundcubemail-1.4.9 /var/www/roundcube
Step 2: Install Dependencies
Roundcube requires the php-imap module to create subfolders in mailboxes, but php-imap isn’t included in the default CentOS 8/RHEL 8 repository, so we need to use the Remi repo to install this PHP module.
Install the Remi Repo.
sudo dnf install -y https://rpms.remirepo.net/enterprise/remi-release-8.rpm
Then reset PHP module streams.
sudo dnf module reset php
Enable the php:remi-7.4 module stream.
sudo dnf module enable php:remi-7.4 -y
Then you can run the following command to install PHP modules required or recommended by Roundcube.
sudo dnf install php-ldap php-imagick php-common php-gd php-imap php-json php-curl php-zip php-xml php-mbstring php-bz2 php-intl php-gmp
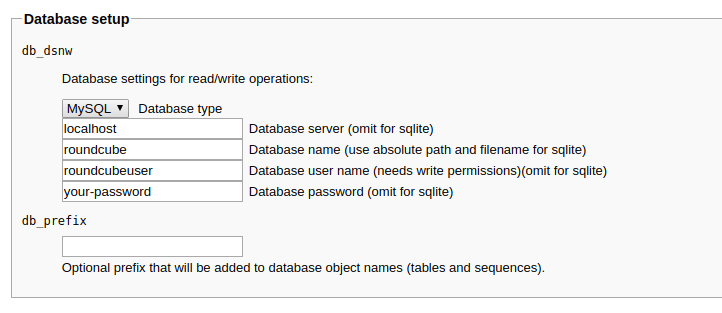
Step 3: Create a MariaDB Database and User for Roundcube
Log into MariaDB shell as root.
mysql -u root -p
Then create a new database for Roundcube using the following command. This tutorial name it roundcube, you can use whatever name you like for the database.
CREATE DATABASE roundcube DEFAULT CHARACTER SET utf8 COLLATE utf8_general_ci;
Next, create a new database user on localhost using the following command. Again, this tutorial name it roundcubeuser, you can use whatever name you like. Replace password with your preferred password.
CREATE USER roundcubeuser@localhost IDENTIFIED BY 'password';
Then grant all permission of the new database to the new user so later on Roundcube webmail can write to the database.
GRANT ALL PRIVILEGES ON roundcube.* TO roundcubeuser@localhost;
Flush the privileges table for the changes to take effect.
flush privileges;
Exit MariaDB Shell:
exit;
Run the following command to import the initial tables to roundcube database. You need to enter the MariaDB root password.
mysql -u root -p roundcube < /var/www/roundcube/SQL/mysql.initial.sql
Step 4: Create Apache Virtual Host or Nginx Config File for Roundcube
Apache
If you use Apache web server, create a virtual host for Roundcube.
sudo nano /etc/httpd/conf.d/roundcube.conf
Note: If you followed my Postfix/Dovecot tutorial, a virtual host already exists. You should edit the following file. (Remove the texts in this file that was added in part 2 and add the new texts below.)
sudo nano /etc/httpd/conf.d/mail.your-domain.com.conf
Put the following text into the file. Replace mail.your-domain.com with your real domain name and don’t forget to set DNS A record for it.
<VirtualHost *:80>
ServerName mail.your-domain.com
DocumentRoot /var/www/roundcube/
ErrorLog /var/log/httpd/roundcube_error.log
CustomLog /var/log/httpd/roundcube_access.log combined
<Directory />
Options FollowSymLinks
AllowOverride All
</Directory>
<Directory /var/www/roundcube/>
Options FollowSymLinks MultiViews
AllowOverride All
Order allow,deny
allow from all
</Directory>
</VirtualHost>
Save and close the file. Reload Apache for the changes to take effect.
sudo systemctl reload httpd
Now you should be able to see the Roundcube web-based install wizard at http://mail.your-domain.com/installer.
Nginx
If you use Nginx web server, create a virtual host for Roundcube.
sudo nano /etc/nginx/conf.d/roundcube.conf
Note: If you followed my Postfix/Dovecot tutorial, a virtual host already exists. you should edit the following file. (Remove the texts in this file that was added in part 2 and add the new texts below.)
sudo nano /etc/nginx/conf.d/mail.your-domain.com.conf
Put the following text into the file. Replace the domain name and don’t forget to set DNS A record for it.
server {
listen 80;
listen [::]:80;
server_name mail.your-domain.com;
root /var/www/roundcube/;
index index.php index.html index.htm;
error_log /var/log/nginx/roundcube.error;
access_log /var/log/nginx/roundcube.access;
location / {
try_files $uri $uri/ /index.php;
}
location ~ \.php$ {
try_files $uri =404;
fastcgi_pass unix:/run/php-fpm/www.sock;
fastcgi_index index.php;
fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name;
include fastcgi_params;
}
location ~ /.well-known/acme-challenge {
allow all;
}
location ~ ^/(README|INSTALL|LICENSE|CHANGELOG|UPGRADING)$ {
deny all;
}
location ~ ^/(bin|SQL)/ {
deny all;
}
# A long browser cache lifetime can speed up repeat visits to your page
location ~* \.(jpg|jpeg|gif|png|webp|svg|woff|woff2|ttf|css|js|ico|xml)$ {
access_log off;
log_not_found off;
expires 360d;
}
}
Save and close the file. Then test Nginx configurations.
sudo nginx -t
If the test is successful, reload Nginx for the changes to take effect.
sudo systemctl reload nginx
Now you should be able to see the Roundcube web-based install wizard at http://mail.your-domain.com/installer.
Step 5: Enabling HTTPS
It’s highly recommended that you use TLS to encrypt your webmail. We can enable HTTPS by installing a free TLS certificate issued from Let’s Encrypt.
If you use Apache, run this command to obtain and install TLS certificate.
sudo certbot --apache --agree-tos --redirect --hsts --staple-ocsp --email [email protected] -d mail.your-domain.com
If you use Nginx, run the following command to obtain and install TLS certificate.
sudo certbot --nginx --agree-tos --redirect --hsts --staple-ocsp --email [email protected] -d mail.your-domain.com
Where
--nginx: Use the nginx plugin.--apache: Use the Apache plugin.--agree-tos: Agree to terms of service.--redirect: Force HTTPS by 301 redirect.--hsts: Add the Strict-Transport-Security header to every HTTP response. Forcing browser to always use TLS for the domain. Defends against SSL/TLS Stripping.--staple-ocsp: Enables OCSP Stapling. A valid OCSP response is stapled to the certificate that the server offers during TLS.
The certificate should now be obtained and automatically installed.
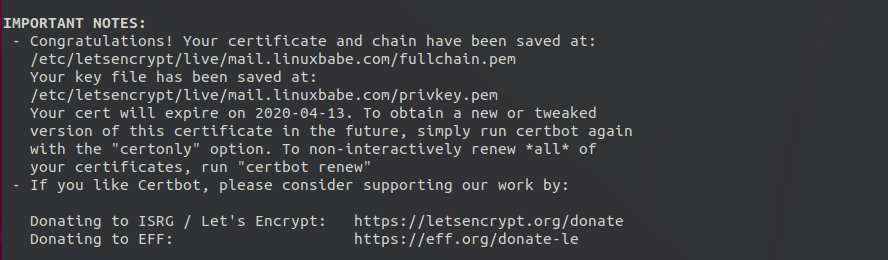
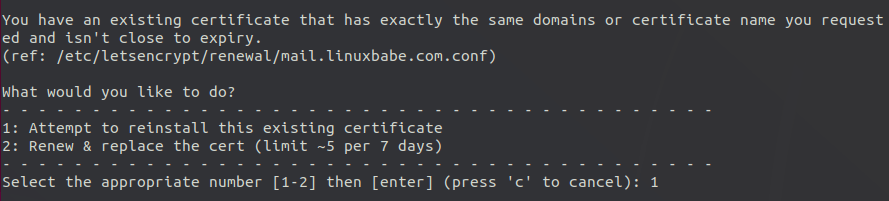
Note: If you followed my Postfix/Dovecot tutorial, and now you install Roundcube on the same server, then certbot will probably tell you that a certificate for mail.your-domain.com already exists as shown below, so you can choose to install the existing TLS certificate to your web server configuration file.
Step 6: Setting Up Permissions
First, we need to change the SELinux context of the web directory, so it can be used to serve web content.
sudo chcon -t httpd_sys_content_t /var/www/roundcube/ -R
The web server needs to write to the temp and logs directory. Change the SELinux context to make it writable.
sudo chcon -t httpd_sys_rw_content_t /var/www/roundcube/temp/ /var/www/roundcube/logs/ -R
Then grant write permission to the web server.
Apache:
sudo setfacl -R -m u:apache:rwx /var/www/roundcube/temp/ /var/www/roundcube/logs/
Nginx:
sudo setfacl -R -m u:nginx:rwx /var/www/roundcube/temp/ /var/www/roundcube/logs/
By default, SELinux forbids Apache/Nginx to make network requests to other servers, but later Apache/Nginx needs to request TLS certificate status from Let’s Encrypt CA server for OCSP stapling, so we need to tell SELinux to allow Apache/Nginx with the following command.
sudo setsebool -P httpd_can_network_connect 1
If you use Nginx, then you also need to run the following command to give the nginx user read and write permissions to 3 directories.
sudo setfacl -R -m u:nginx:rwx /var/lib/php/opcache/ /var/lib/php/session/ /var/lib/php/wsdlcache/
Restart Apache/Nginx.
sudo systemctl restart httpd sudo systemctl restart nginx
Step 7: Adding Local DNS Entry
It’s recommended to edit the /etc/hosts file on the mail server and add the following entry so that Roundcube won’t have to query the public DNS, which will speed up web page loading a little bit.
127.0.0.1 localhost mail.your-domain.com
Step 8: Finish the Installation in Web Browser
In your web browser, go to the Roundcube installer page.
https://mail.your-domain.com/installer
The web installer will first check if PHP extensions, database and 3rd party libraries are installed. If you follow this tutorial, then all requirements should be met.
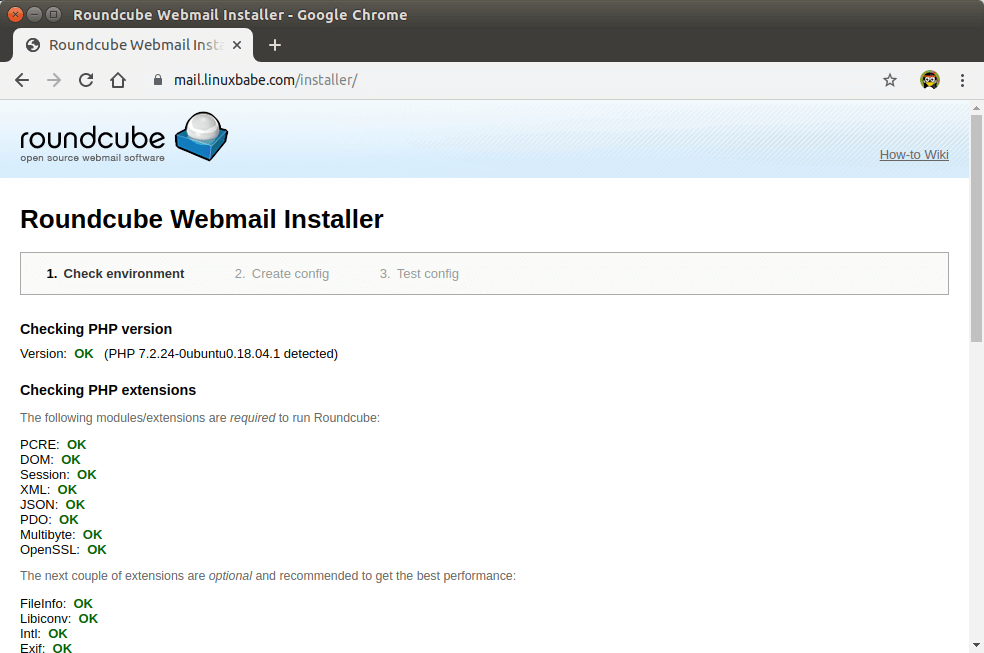
Click Next button. In the 2nd page, you need to fill in MariaDB database details that you created in step 3.
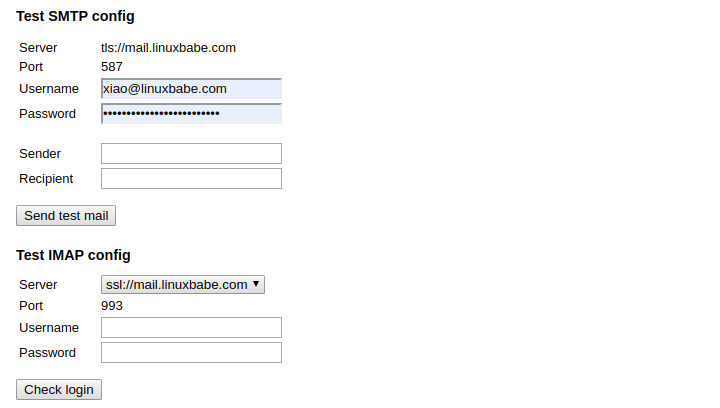
The IMAP and SMTP section allows you to configure how to receive and submit email. Enter the following values for IMAP.
- IMAP host:
ssl://mail.your-domain.comport:993
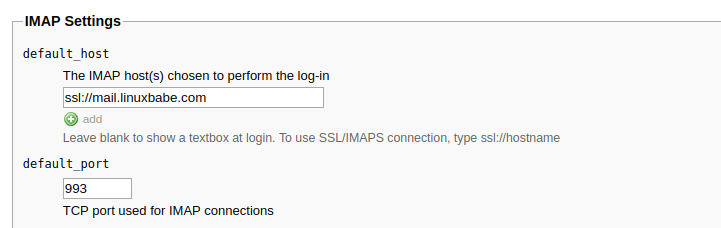
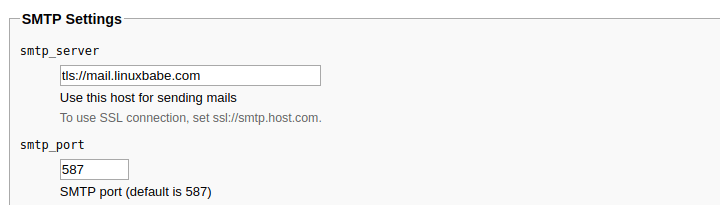
Enter the following values for SMTP settings.
- SMTP port:
tls://mail.your-domain.comport:587. Note that you must usetls://as the prefix for port 587. Thessl://prefix should be used for port 465.
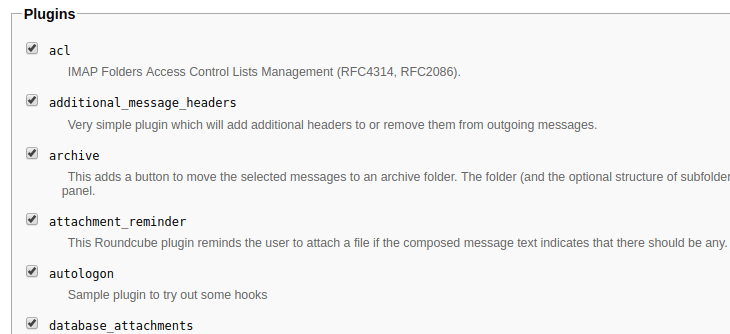
Next, you can scroll down to the Plugins section to enable some plugins. For example: the password plugin, mark as junk plugin and so on. I enabled all of them.
Once that’s done, click create config button which will create configuration based on the information you entered. You need to copy the configuration and save it as config.inc.php under the /var/www/roundcube/config/ directory.
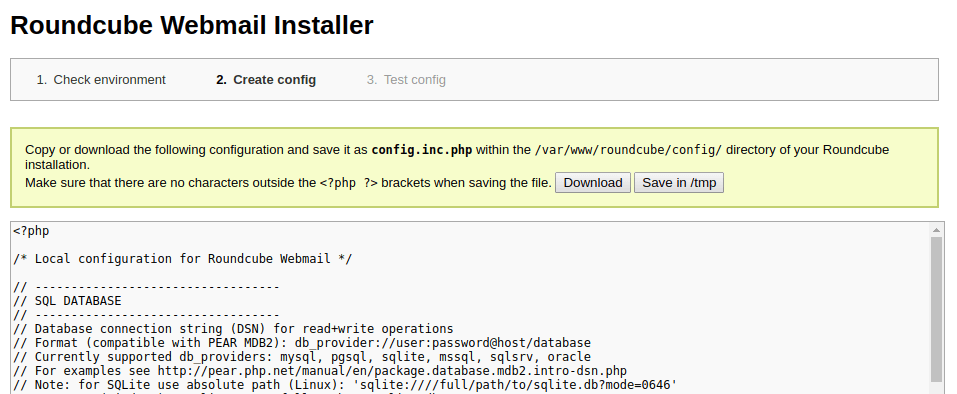
Once the config.inc.php file is created, click continue button. In the final step, test your SMTP and IMAP settings by sending a test email and checking IMAP login. Note that you need to enter your full email address in the Sender field when testing SMTP config.
If the test fails, then you can click the 2. Create config link on the top of page to go back to step 2 and recreate the config.inc.php file.
If test is successful, go to your Webmail domain without /installer and login.
Roundcube Webmail interface
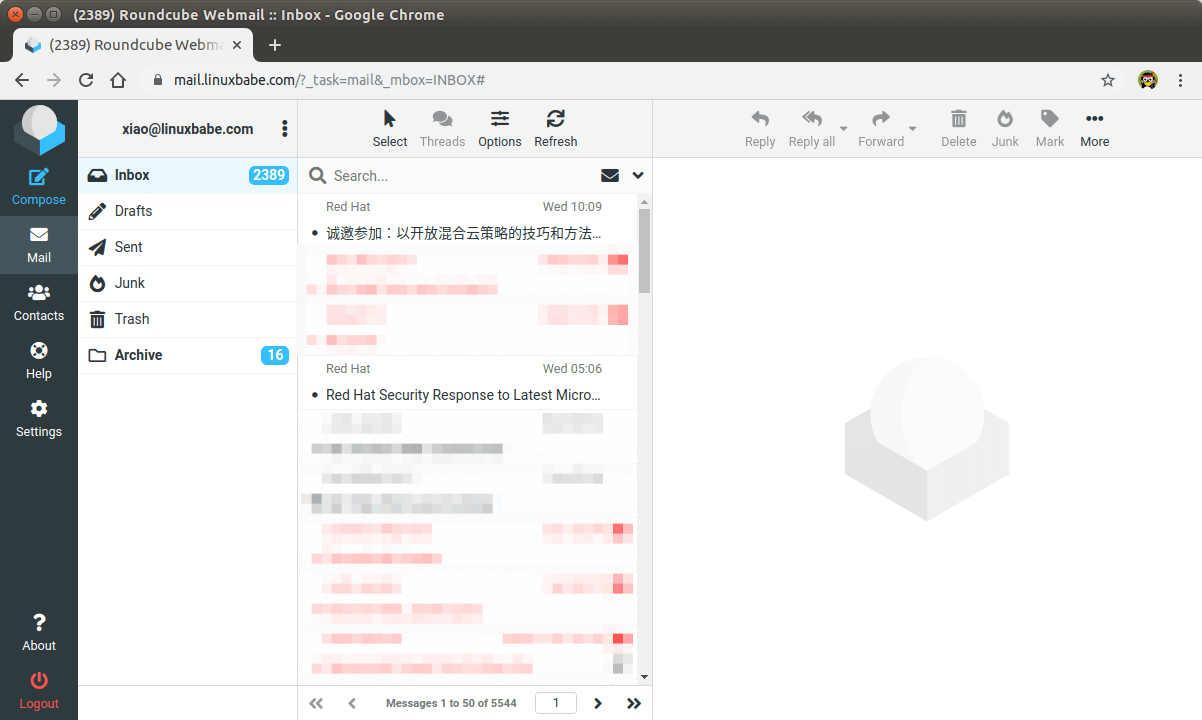
Now you should remove the whole installer folder from the document root or make sure that enable_installer option in config.inc.php file is disabled.
sudo rm /var/www/roundcube/installer/ -r
These files may expose sensitive configuration data like server passwords and encryption keys to the public. Make sure you cannot access the installer page from your browser.
Step 9: Configure the Sieve Message Filter
You can create folders in Roundcube webmail and then create rules to filter email messages into different folders. In order to do this, you need to install the dovecot-pigeonhole package with the following command.
sudo dnf install dovecot-pigeonhole
Open the /etc/dovecot/conf.d/15-lda.conf file.
sudo nano /etc/dovecot/conf.d/15-lda.conf
Scroll to the end of the file, uncomment the mail_plugins line and add the sieve plugin to local delivery agent (LDA).
protocol lda {
# Space separated list of plugins to load (default is global mail_plugins).
mail_plugins = $mail_plugins sieve
}
Save and close the file. If you can find the 20-lmtp.conf file under /etc/dovecot/conf.d/ directory, then you should also enable the sieve plugin in that file like below.
protocol lmtp {
mail_plugins = quota sieve
}
Edit the /etc/dovecot/conf.d/10-mail.conf file.
sudo nano /etc/dovecot/conf.d/10-mail.conf
Sieve scripts are stored under each user’s home directory. If you followed my PostfixAdmin tutorial and are using virtual mailbox domains, then you need to enable mail_home for the virtual users by adding the following line in the file, because virtual users don’t have home directories by default.
mail_home = /var/vmail/%d/%n
Save and close the file.
By default, Postfix uses its built-in local delivery agent (LDA) to move inbound emails to the message store (inbox, sent, trash, Junk, etc). We can configure it to use Dovecot to deliver emails, via the LMTP protocol, which is a simplified version of SMTP. LMTP allows for a highly scalable and reliable mail system and it is required if you want to use the sieve plugin to filter inbound messages to different folders.
Edit the Dovecot main configuration file.
sudo nano /etc/dovecot/dovecot.conf
Add lmtp and sieve to the supported protocols.
protocols = imap lmtp sieve
Save and close the file. Then edit the Dovecot 10-master.conf file.
sudo nano /etc/dovecot/conf.d/10-master.conf
Change the lmtp service definition to the following.
service lmtp {
unix_listener /var/spool/postfix/private/dovecot-lmtp {
group = postfix
mode = 0600
user = postfix
}
}
Next, edit the Postfix main configuration file.
sudo nano /etc/postfix/main.cf
Add the following lines at the end of the file. The first line tells Postfix to deliver emails to local message store via the dovecot LMTP server. The second line disables SMTPUTF8 in Postfix, because Dovecot-LMTP doesn’t support this email extension.
mailbox_transport = lmtp:unix:private/dovecot-lmtp smtputf8_enable = no
Save and close the file. Finally, restart Postfix and Dovecot.
sudo systemctl restart postfix dovecot
Now you can go to Roundcube webmail, open an email message and click the more button and select create filters to create message filters. For example, I create a filter that moves every email sent from redhat.com to the Red Hat folder.
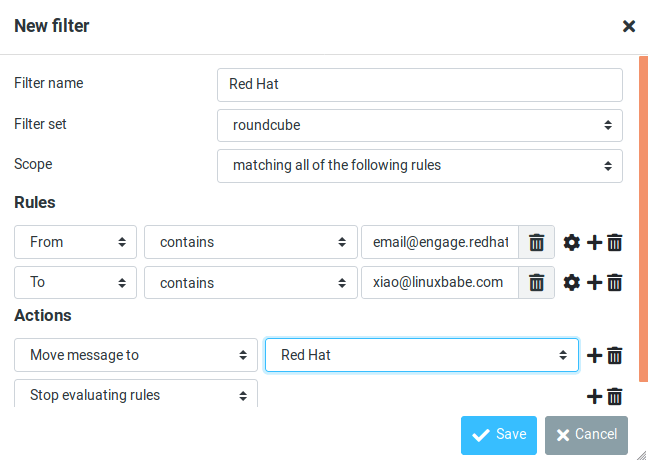
If you don’t have the create filter option, it’s probably because you didn’t enable the managesieve plugin. Edit the config.inc.php file.
sudo nano /var/www/roundcube/config/config.inc.php
Add the managesieve plugin in the array at the end of this file. The plugin order doesn’t matter.
$config['plugins'] = array('acl', 'additional_message_headers', 'managesieve', .....);
Save and close the file.
Note that if you move a sieve filter set from an old mail server to your new mail server, you need to go to Settings -> Filters, then click Actions and enable the filter set, or Dovecot LMTP server won’t execute the sieve filter.
Step 10: Removing Sensitive Information from Email Headers
By default, Roundcube will add a User-Agent email header, indicating that you are using Roundcube webmail and the version number. You can tell Postfix to ignore it so recipient can not see it. Run the following command to create a header check file.
sudo nano /etc/postfix/smtp_header_checks
Put the following lines into the file.
/^User-Agent.*Roundcube Webmail/ IGNORE
Save and close the file. Then edit the Postfix main configuration file.
sudo nano /etc/postfix/main.cf
Add the following line at the end of the file.
smtp_header_checks = regexp:/etc/postfix/smtp_header_checks
Save and close the file. Then run the following command to rebuild hash table.
sudo postmap /etc/postfix/smtp_header_checks
Reload Postfix for the change to take effect.
sudo systemctl reload postfix
Now Postfix won’t include User-Agent: Roundcube Webmail in the headers when sending outgoing emails.
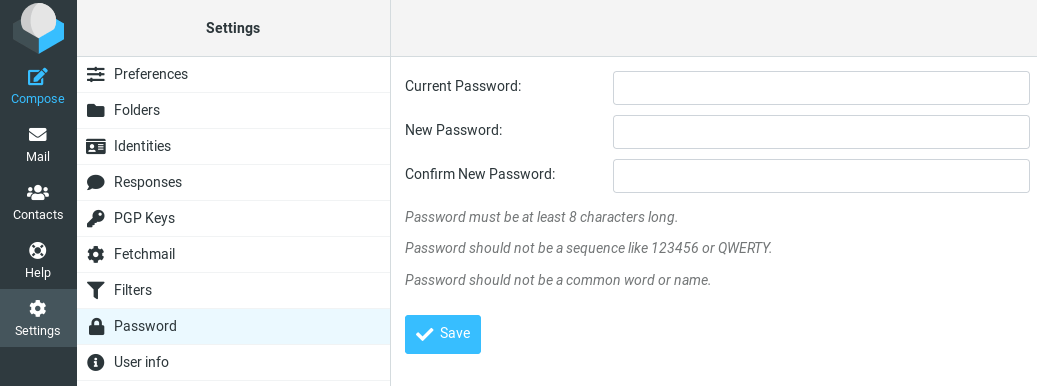
Step 11: Configure the Password Plugin in Roundcube
Roundcube includes a password plugin that allows users to change their passwords from the webmail interface. Edit the config.inc.php file.
sudo nano /var/www/roundcube/config/config.inc.php
Make sure the password plugin in the plugin list at the end of this file. The plugin order doesn’t matter.
$config['plugins'] = array('acl', 'additional_message_headers', 'password', .....);
Save and close the file.
However, we need to configure this plugin before it will work. Edit the password plugin configuration file.
sudo nano /var/www/roundcube/plugins/password/config.inc.php
If your Roundcube doesn’t have the config.inc.php file, then copy the default config file and edit the file.
cd /var/www/roundcube/plugins/password/ sudo cp config.inc.php.dist config.inc.php sudo nano config.inc.php
Find the following line:
$config['password_db_dsn'] = '';
This parameter is used to tell the password plugin where the user passwords are stored. By default, the value is empty and it will query the roundcube database, which doesn’t store user passwords. If you followed my PostfixAdmin tutorial, then user passwords are stored in the postfixadmin database, so we need to change the value to:
$config['password_db_dsn'] = 'mysql://postfixadmin:postfixadmin_database_password@127.0.0.1/postfixadmin';
The tells the password plugin to connect to the postfixadmin database. If you don’t remember your postfixadmin database password, you can find it in the /etc/dovecot/dovecot-sql.conf.ext file. If your PostfixAdmin password contains a single quote character, then you can use backslash (\') to escape it.
Then find the following line.
$config['password_query'] = 'SELECT update_passwd(%c, %u)';
Change it to the following.
$config['password_query'] = 'UPDATE mailbox SET password=%D,modified=NOW() WHERE username=%u';
I recommend enabling a password strength checker to prevent users from setting week passwords. Go to the beginning of this file, you can find the following line.
$config['password_strength_driver'] = null;
We can use the zxcvbn password strength driver, so change it to:
$config['password_strength_driver'] = 'zxcvbn';
Add the following line in this file to allow strong passwords only.
$config['password_zxcvbn_min_score'] = 5;
Note: The $config['password_minimum_score'] parameter doesn’t work with the zxcvbn driver, so leave it alone.
You can also set a minimum length for the password. Find the following line.
$config['password_minimum_length'] = 0;
Change it to:
$config['password_minimum_length'] = 8;
Recall that we used the BLF-CRYPT password scheme in the PostfixAdmin tutorial, so we also need to configure the password plugin to use BLF-CRYPT. Find the following lines in the file.
$config['password_algorithm'] = 'clear';
By default, the password will be stored as clear text, change the value to the following to use Dovecot’s builtin password algorithm.
$config['password_algorithm'] = 'dovecot';
Then find the following line, which tells where the Dovecot’s password hash generator is located.
$config['password_dovecotpw'] = '/usr/local/sbin/dovecotpw'; // for dovecot-1.x
Change it to the following.
$config['password_dovecotpw'] = '/usr/bin/doveadm pw -r 12';
Then find the following line, which tells which password scheme will be used.
$config['password_dovecotpw_method'] = 'CRAM-MD5';
Change it to:
$config['password_dovecotpw_method'] = 'BLF-CRYPT';
Find the following line.
$config['password_dovecotpw_with_method'] = false;
Change false to true. This will add a {BLF-CRYPT} prefix to the hashed password, so you will recognize which password scheme is used.
$config['password_dovecotpw_with_method'] = true;
Save and close the file. Since this file contains the database password, we should allow only the web server user to read and write to this file.
Apache
sudo chown apache:apache /var/www/roundcube/plugins/password/config.inc.php sudo chmod 600 /var/www/roundcube/plugins/password/config.inc.php
Nginx
sudo chown nginx:nginx /var/www/roundcube/plugins/password/config.inc.php sudo chmod 600 /var/www/roundcube/plugins/password/config.inc.php
Now users should be able to change their passwords in the Roundcube webmail interface.
How to Set Up Vacation/Out-of-Office Messages
We can use the sieve filter to create vacation/out-of-office messages. Go to Roundcube Settings -> Filters. Then click the create button to create a filter.
- Give this filer a name like “out of office”.
- New filters are not disabled, so you can leave the button alone.
- In the Scope field, select all messages.
- Select Replay with message in the Actions settings, and enter the message that will be automatically sent.
- Enter 1 in how often send messages, so the auto-reply will be sent only once per day for each sender. If you set this value to 7, then the auto-reply will be sent once per 7 days for each sender.
- Leave other text fields empty.
- Click the Save button and you are done.
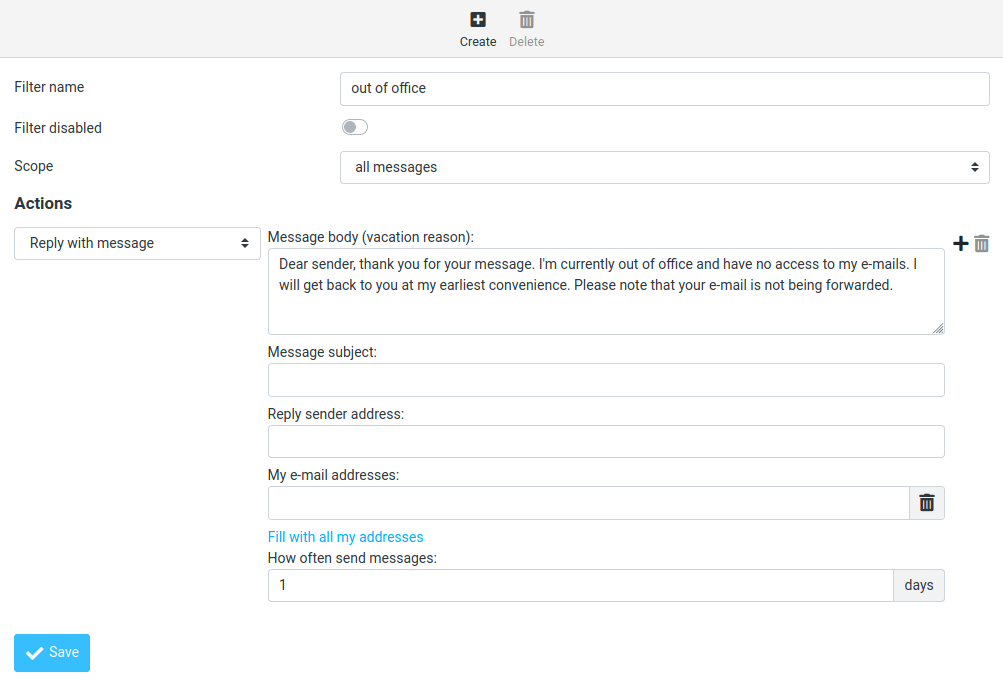
When you are back to office, you can toggle the “Filter disabled” button, and click the Save button to disable this filter.
Setting Up Multiple Mail Domains
To host multiple mail domains, please read the following article:
Troubleshooting Tips
If you encounter errors, you can check the web server error logs at /var/log/apache2/roundcube_error.log (if you are using Apache), or /var/log/nginx/roundcube.error (if you are using Nginx.), also the Roundcube error logs in /var/www/roundcube/logs/ directory.
Connection to Storage Server Failed
If you see the Connection to storage server failed error when trying to log into RoundCube, it’s probably because
- Dovecot server isn’t running. You can restart Dovecot with
sudo systemctl restart dovecotand check its status withsystemctl status dovecot. - You are using a self-signed TLS certificate. Roundcube requires a valid TLS certificate issued from a trusted certificate authority such as Let’s Encrypt.
- Your TLS certificate expired. You can renew the Let’s Encrypt TLS certificate with
sudo certbot renew, then restart Postfix and Dovecot (sudo systemctl restart postfix dovecot).
You can also try adding a custom DNS entry in /etc/hosts file as described in step 9 on the Roundcube server, so Roundcube can properly resolve the mail server hostname.
Could Not Load Message From Server
If you see the “Internal error: could not load message from server” error, it’s probabaly because you are trying to open an deleted email (invalid URL). Try going to the mail root domain (mail.example.com) to see if it works.
Wrapping Up
I hope this tutorial helped you install Roundcube Webmail on CentOS 8/RHEL 8. As always, if you found this post useful, subscribe to our free newsletter to get more tips and tricks 🙂



Thanks for sharing.
Thank you for the detailed guide!
Hi,
don’t you have to set owner of /var/www/roundcube to the correct user depending if you’re using roundcube or nginx user ?
regards
The web server needs to have write permission on
/var/www/roundcube/temp/and/var/www/roundcube/logs/directory, and have read permission on the main /var/www/roundcube/ directory.HI, great tutorial, just having issues with the roundcube install:
when running commands like:
sudo chcon -t httpd_sys_content_t /var/www/roundcube/ -R
&
sudo chcon -t httpd_sys_rw_content_t /var/www/roundcube/temp/ /var/www/roundcube/logs/ -R
getting lots of error:
chcon: can’t apply partial context to unlabeled file…
How do I get around this?
I think selinux may be disabled if you’re seeing errors like that. enter “sestatus” at the command prompt and see if it’s set to disabled.
Hi, it is a great tutorial, i have used all of its parts to deploy a mail server, and it works perfect!
But I’m having a problem with configuring nginx as it says in step 4 of this tutorial, because a lot of settings appeared in /etc/nginx/conf.d/mail.your-domain.com.conf after previous tutorials.
By adding settings from step 4 as a result I recieve 404, by changing root for https I recieve 403 Forbidden. I have tried to complete further steps, but it didn’t help(((
I’m stuck in it, so it would be very kind if You could help me. THX
Simply remove the texts in this file that was added in part 2 and add the new texts.
hi,
new install of CentOS 8, installed roundcubemail 1.4.9, I can check email, sending email fails just get notification down in lower right corner, which goes away and email never sent. selinux is in permissive mode, I can get it fail if I change the smtp host line from tls to ssl
apache logs and php-fpm logs don’t show anything, anyone know how to trouble shoot this issue?
For sending email:
Prefix
tls://should be used with port 587 (STARTTLS).Prefix
ssl://should be used with port 465 (SMTPS).Hello Xiao,
have followed all your tutorials postfix,dovecot,postfixadmin, really appreciate the time you have put in. I seem to be having an issue where. I dont seem to be able to test smtp or imap config, always times out takes forever.
[proxy_fcgi:error] [pid 75448:tid 140460764440320] (70007)The timeout specified has expired: [client IP:34550] AH01075: Error dispatching request to : (polling), referer: https://webmail.domain.co.uk/installer/index.php?_step=3
Any ideas, dont see anything else in any logs postfix,dovecot even checked in amavis.
Hi! Great tutorial, followed all steps. My goal is to test SPF and DKIM on my private network (not connected to external DNS servers) thus I do not need an SSL certificate nor any additional encryption. My network contents of two centos8 mail servers and two DNS each pair in its own subnet. DNS servers added to resolv.conf.
I omitted TLS entry in
and similar steps related to SSL/TLS and changed
to
Is that correct? Should I change some more? What should the configuration look like?
I case you need further information, I can easly provide them! 🙂
can not to send,error log:
[12-Feb-2021 19:18:10 +0000]: PHP Error: php_network_getaddresses: getaddrinfo failed: 未知的名称或服务 (POST /?_task=mail&_unlock=loading1613157488353&_framed=1&_lang=en&_action=send)
[12-Feb-2021 19:18:10 +0000]: PHP Error: Failed to connect socket: php_network_getaddresses: getaddrinfo failed: 未知的名称或服务 (POST /?_task=mail&_unlock=loading1613157488353&_framed=1&_lang=en&_action=send)
[12-Feb-2021 19:18:10 +0000]: SMTP Error: Connection failed: Failed to connect socket: php_network_getaddresses: getaddrinfo failed: 未知的名称或服务 in /var/www/html/webmail/program/lib/Roundcube/rcube.php on line 1702 (POST /?_task=mail&_unlock=loading1613157488353&_framed=1&_lang=en&_action=send)
[12-Feb-2021 19:20:02 +0000]: PHP Error: php_network_getaddresses: getaddrinfo failed: 未知的名称或服务 (POST /?_task=mail&_unlock=loading1613157600630&_framed=1&_lang=en&_action=send)
I’m having trouble importing mysql to /var/www/roundcube/SQL/mysql.initial.sql.
when I tried it the first time it said there was no such file or directory, so I made dir, but I still cant put it in the file there.
How could I solve it ?
I figured it out.
To those who struggle with the same problem:
You have to download roundcube before you can do this.
Tecmint.com had a better explanation on this.
1. wget -c https://github.com/roundcube/roundcubemail/releases/download/1.4.9/roundcubemail-1.4.9-complete.tar.gz
2. tar xzf roundcubemail-1.4.9-complete.tar.gz
3. mv roundcubemail-1.4.9 /var/www/html/roundcubemail
4. cd /var/www/html/roundcubemail/
5. mysql -u root -p roundcubemail flush privileges;
6. Set new password by ALTER USER ‘root’@’localhost’ IDENTIFIED BY ‘NewPassword’;
7. Go back to /etc/my.cnf and remove/comment skip-grant-tables
8. Restart Mysql
9. Now you will be able to login with the new password mysql -u root -p
Good luck!
Excellent comprehensive howto 🙂
Hi, I’m looking for php-imap for aarch64 (rpi4) – do you know link to rpm or repo? Thank you.
# dnf module reset php
Status code: 403 for http://cdn.remirepo.net/enterprise/8/modular/aarch64/mirror
For Roundcube and PostfixAdmin on the same server:
VirtualHost definitions look like this (ServerName is the same):
ServerName mymailserver.example.com
DocumentRoot /var/www/postfixadmin/public/
…
ServerName mymailserver.example.com
DocumentRoot /var/www/roundcube/
…
When I try to go to http://mymailserver.example.com/installer to complete Roundcube’s install, the logs say I am trying to access /var/www/postfixadmin/public/installer
What the heck ?
Also, have you been able to get the Roundcube Password Plugin to work ?
I keep getting an error code of 600 and a message “Service not available”
If possible, I would prefer to have the customers do everything in Roundcube.
You can’t have two same ServerName in Apache.
Use different ServerName for Roundcube and PostfixAdmin. For example
If I am not mistaken, that would mean a CNAME in DNS for the second name and both names in the TLS certificate. We do not use Let’s Encrypt (yet).
Your method would then be using separate Let’s Encrypt certs for Roundcube and PostfixAdmin. right ?
Whether you use Let’s Encrypt or not doesn’t matter. You can’t use the same ServerName to represent different applications in Apache.
I understand that I need two, unique ServerName entries.
I would do that in DNS with an A record and a CNAME record.
Would you do it differently ?
For the (not Let’s Encrypt)-certificate, it would need to include both FQDN’s, right ?
If one follows your examples exactly, you end up with two LE-certs, right ?
And, finally, have you been able to get the Roundcube Password Plugin to work ?
I cannot.
Yes. You can use CNAME record.
Yes. I have two Let’s Encrypt certificates.
I don’t publish tutorial that doesn’t work. It works on my server when I publish it.
What plugins does your roundcube have enabled ?
I have
I am still getting error code of 600 “Service not available”
I turned up log levels and debugging and I find nothing in the logs
OOPS !
That was me.
hi,
the roundcube managesieve abend with the existing configuration. The issue is rather simple add vmail in authorized_submit_users = root,www-data,vmail (/etc/postfix/main.cf). The problem may disappear. But if the problem persists: https://easyengine.io/tutorials/mail/server/sieve-filtering/ may provide an answer
hi,
/roundcube/plugins/password/config.inc.php may have a problem of being utilised as the it needs to be chown nginx:nginx config.inc.php, Another issue is when the content security policy is set too tight, the change password screen may look a bit funny (as the old password field did not appear).
I thoroughly enjoy this series of work done by Xiao, wonderful work that help us learn a lot.
Hello,I’m new to this and I can solve many problems, but I can’t figure this one out. When I try login to my email (via Roundcube or via Thunderbird), it always fails and Dovecot writes this messages to log:
I get that I need to specify passdb section in dovecot config file. But this is missing in this tutorial and since I’m new to this, I would appreciate help. I have no clue what to write there. Just for info, this is my dovecot configuration (dovecot -n):
# 2.3.8 (9df20d2db): /etc/dovecot/dovecot.conf# OS: Linux 4.18.0-305.10.2.el8_4.x86_64 x86_64 CentOS Linux release 8.4.2105# Hostname: mta1.bartie.czauth_debug = yesauth_debug_passwords = yesauth_mechanisms = plain loginauth_username_format = %ufirst_valid_uid = 1000mail_home = /var/vmail/%d/%nmail_location = maildir:~/Maildirmail_privileged_group = mailmbox_write_locks = fcntlnamespace inbox { inbox = yes location = mailbox Drafts { auto = create special_use = Drafts } mailbox Junk { auto = create special_use = Junk } mailbox Sent { auto = create special_use = Sent } mailbox "Sent Messages" { special_use = Sent } mailbox Trash { auto = create special_use = Trash } prefix =}protocols = imap lmtpservice auth { unix_listener /var/spool/postfix/private/auth { group = postfix mode = 0600 user = postfix }}service lmtp { unix_listener /var/spool/postfix/private/dovecot-lmtp { group = postfix mode = 0600 user = postfix }}service stats { unix_listener stats-reader { group = apache mode = 0660 user = apache } unix_listener stats-writer { group = apache mode = 0660 user = apache }}Thank very much to anybody, who will spare some time to think about this
Check the /etc/dovecot/conf.d/auth-dict.conf.ext file.
The default content should be as follows:
If I try this, it is still doing nothing. Unless I include auth-dict.conf.ext in 10-auth.conf. But then I need to create file mentioned in
The dovecot-dict-auth.conf.ext i set up like here: https://github.com/dovecot/core/blob/master/doc/example-config/dovecot-dict-auth.conf.ext.
But then it throws error:
So I tried set uri variable like this
But then I have error
As I think, auth-token-secret.dat it’s related to PAM authentication, but we are going to use DICT. I’m a bit confused and don’t know if I got this right.
I have the following content at the end of the
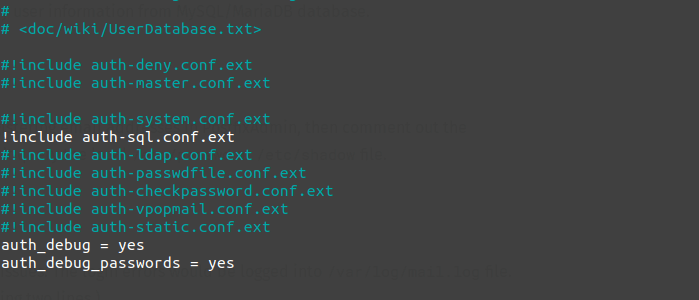
/etc/dovecot/conf.d/10-auth.conffile.It uses SQL-based authentication, as described in my PostfixAdmin tutorial. DICT-based authentication is not enabled.
Hi, Please enter the beginning that this is not for aarch64. Remirepo does not support this architecture. Unable to install eg php-imap / imagic.
Dear Xiao,
Many thanks ur great tutorial.
Now I have a equiry. my roundcube could change password when Selinux permission. If Selinux enforcing, Selinux will stop roundcube change password.
I have realized this is a permissions issue. After the below sentences, it still does not work:
Apache
sudo chown apache:apache /var/www/roundcube/plugins/password/config.inc.php
sudo chmod 600 /var/www/roundcube/plugins/password/config.inc.php
How to fix it?
Please follow step 6 to set up permissions.
Hint: Never disable SELinux.
Dear Xiao,
Many thanks for ur reply.
I followed step 6 step by step, but still does not work. When the Selinux status enforcing, roundcube could not modify password.
I try to audit2allow -a, it shows below:
#============= httpd_t ==============
allow httpd_t dovecot_etc_t:dir read;
allow httpd_t dovecot_etc_t:file { getattr open read };
then, I try to load, check the code below:
grep dove /var/log/audit/audit.log | audit2allow -M my-module
which is not helpful.
How to fix it?
Fei
I followed step 6 step by step when Selinux enable, but still does not work.
I’m facing ‘discarded duplicate vacation response to ‘ error,
/etc/dovecot/conf.d/90-sieve.conf
sieve_vacation_min_period = 0
sieve_vacation_default_period = 0
sieve_vacation_max_period = 0
.dovecot.sieve:
vacation :seconds 30 :addresses
having the same problem ‘discarded duplicate vacation response to‘ error which appeared suddenly.
tried the same modification as yours in 90-sieve.conf
does not work.
also added the vacation-seconds plugin and even the possibility to add values in seconds in roundcube, it doesn’t work.
the .dovecot.svbin file is generated (contains “{ vacation :seconds 10 :subject…”) but the parameter is not used.
using postfix/dovecot/roundcube on debian 11
Really appreciate all your hard work and these very helpful How Tos. I had this working on a fresh install of CentOS 8 Stream yesterday. Today, I go to read my system mail and its not working. I have checked every log I can think of, there is no error in any.
I am using MySQL 8.0.28, not MariaDB. I have default_authentication_plugin=mysql_native_password in /etc/my.cnf and I ran: ALTER USER roundcubeuser’@’localhost’ IDENTIFIED WITH mysql_native_password BY ‘password’;
So, I tried to rerun the installer. Now its saying MySQL is not available. MySQL is working fine for my other applications requiring MySQL.
I even dropped the database and user and started over. Still no ggod.
I have run out of ideas and things to check. Maybe someone here can help.
TIA
OK, figured it out, if using CentOS 8 Stream and MySQL 8.x, you need to install, php-mysqlnd. Not sure how it was working without it but it’s working now.
Hi there,
When working on installing Roudcube, I’m seeing the following error in my maillogs:
Error: sql(email_address_goes_here,127.0.0.1): Unknown scheme BLF-CRYPT
Any idea how to fix this, not found much information online.
Thanks.
Hi
Facing issue on after “Step 9: Configure the Sieve Message Filter”, Postfixadmin login was having conflict password hashing problem with encrypt backend (dovecot:BLF-CRYPT).
In my web browser, when I go to the Roundcube installer page.
https://mail.mydomain.com/installer
Browser is showing:
Index of /roundcube/installer
[ICO] Name Last modified Size Description
[PARENTDIR] Parent Directory –
[TXT] check.php 2022-06-26 10:26 8.8K
[ ] client.js 2022-06-26 10:26 1.6K
[TXT] config.php 2022-06-26 10:26 22K
[DIR] images/ 2022-07-08 15:18 –
[TXT] index.php 2022-06-26 10:26 6.6K
[TXT] styles.css 2022-06-26 10:26 3.3K
[TXT] test.php 2022-06-26 10:26 16K
So I read your Roundcube tutorial (and donated, keep up the good work! 👍) but had a problem with the password plugin.
I am getting: Could not save new password. Encryption function missing.
/srv/live/php/roundcubemail-1.6.0/logs/errors.log
/srv/live/php/roundcubemail-1.6.0/config/config.inc.php
I had a preexisting setup that was almost identical to yours, just without Roundcube and using MD5-crypt.
I had done all steps on RHEL 9 Machine, i login to roundcube ok, but no email send , it gives error of ” internal Server Error” and no recipients are added.. how to solve this problem.
great work! after all these years it’s still hot stuff 🙂 thx
one error tho
in Step 11: Configure the Password Plugin in Roundcube
$config[‘password_query’] should use %P not %D
HI, great tutorial, having issues with the Configure the Sieve Message Filter
After successfully log in to the web mail.
when I click settings and filters.
Error: unable to connect to server
Message Filter didn’t work.
Please help me on it.
How do I get around this?