Host Multiple Mail Domains in PostfixAdmin on CentOS/RHEL
This tutorial will be showing you how to set up multiple mail domains (virtual hosting) on CentOS/RHEL server with PostfixAdmin, which is an open-source web-based interface to configure and manage a Postfix based email server for many domains and users.
Prerequisites
To follow this tutorial, it’s required that
- You have configured PostfixAdmin with one mail domain.
- You have followed part 4 to set up SPF and DKIM.
- You have installed Roundcube Webmail.
Once the above requirements are met, follow the instructions below.
What You Need to Do
If you want to host multiple mail domains, then you need to
- Add a new mail domain and user in PostfixAdmin web-based panel.
- Create MX, A and SPF record for the new mail domain.
- Set up DKIM signing for the new domain.
- Create DMARC Record for the new domain.
- Set up RoundCube Webmail, Postfix and Dovecot for multiple domains
Step 1: Adding Additional Domains in PostfixAdmin Panel
Log into PostfixAdmin panel with the postmaster account. (https://postfixadmin.your-domain.com/) Then go to Domain List -> New Domain to add a new domain.
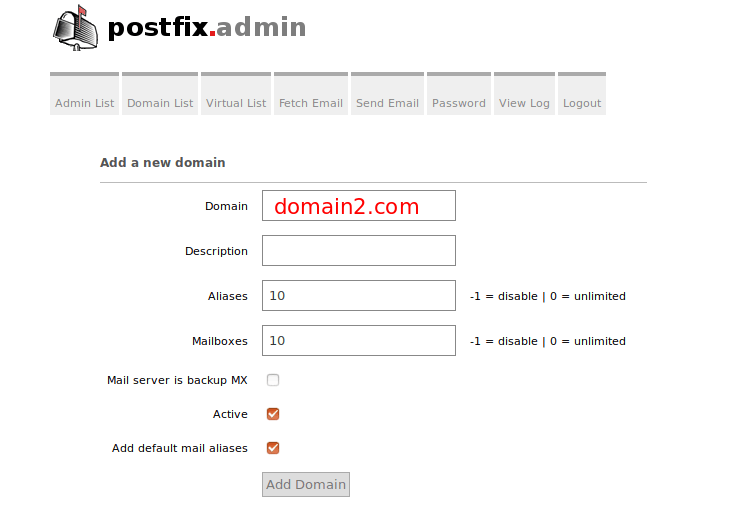
Note that the new domain should have DNS A record, or PostfixAdmin would throw the following error message. You can check the DNS propagation status on dnsmap.io.
Invalid domain domain2.com, and/or not discoverable in DNS
Next, add a user under the new domain.

Step 2: Creating MX, A and SPF record for the new mail domain
In your DNS manager, add MX record for the new domain like below.
Record Type Name Value
MX @ mail.domain2.com
The A record points to your mail server’s IP address.
Record Type Name Value
A mail IP-address-of-mail-server
If your server uses IPv6 address, be sure to add AAAA record.
Then create SPF record to allow the MX host to send email for the new mail domain.
Record Type Name Value
TXT @ v=spf1 mx ~all
Step 3: Setting up DKIM signing for the new domain
We have installed and configured OpenDKIM for a single domain in part 4 of this tutorial series. Now we need to tell OpenDKIM to sign every outgoing email for the new mail domain.
Edit the OpenDKIM signing table file.
sudo nano /etc/opendkim/SigningTable
Add the second domain like below.
*@domain1.com 20200308._domainkey.domain1.com *@domain2.com 20200308._domainkey.domain2.com
Edit the key table file.
sudo nano /etc/opendkim/KeyTable
Add the second domain like below.
20200308._domainkey.domain1.com domain1.com:20200308:/etc/opendkim/keys/domain1.com/20200308.private 20200308._domainkey.domain2.com domain2.com:20200308:/etc/opendkim/keys/domain2.com/20200308.private
Edit the trusted hosts file.
sudo nano /etc/opendkim/TrustedHosts
Add the second domain like below.
127.0.0.1 localhost .domain1.com .domain2.com
Next, we need to generate a priavte/public keypair for the second domain. Create a separate folder for the second domain.
sudo mkdir /etc/opendkim/keys/domain2.com
Generate keys using opendkim-genkey tool.
sudo opendkim-genkey -b 2048 -d domain2.com -D /etc/opendkim/keys/domain2.com -s 20200308 -v
The above command will create 2048 bits keys. -d (domain) specifies the domain. -D (directory) specifies the directory where the keys will be stored and we use 20200308 (current date) as the selector (-s). Once the command is executed, the private key will be written to 20200308.private file and the public key will be written to 20200308.txt file.
Make opendkim as the owner of the private key.
sudo chown opendkim:opendkim /etc/opendkim/keys/domain2.com/20200308.private
Display the public key
sudo cat /etc/opendkim/keys/domain2.com/20200308.txt
The string after the p parameter is the public key.
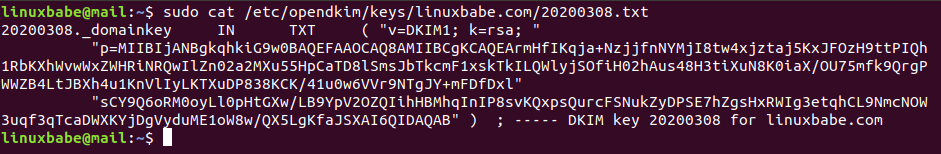
In your DNS manager, create a TXT record for the second domain. Enter 20200308._domainkey in the Name field. Copy everything in the parentheses and paste into the value field. Delete all double-quotes. (You can paste it into a text editor first, delete all double quotes, then copy it to your DNS manager. Your DNS manager may require you to delete other invalid characters, such as carriage return.)
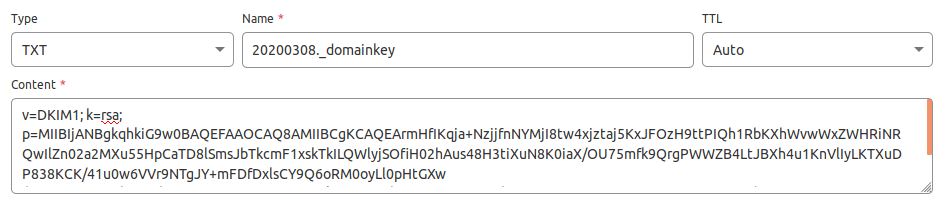
After saving your changes. Check the TXT record with this command.
dig TXT 20203008._domainkey.domain2.com
Now you can run the following command to test if your DKIM DNS record is correct.
sudo opendkim-testkey -d domain2.com -s 20200308 -vvv
If everything is OK, you will see
opendkim-testkey: using default configfile /etc/opendkim.conf opendkim-testkey: checking key '20203008._domainkey.domain2.com' opendkim-testkey: key secure opendkim-testkey: key OK
If you see “Key not secure”, don’t panic. This is because DNSSEC isn’t enabled on your domain name. DNSSEC is a security standard for secure DNS query. Most domain names haven’t enabled DNSSEC. You can continue to follow this guide.
Restart OpenDKIM so it will start signing emails for the second domain.
sudo systemctl restart opendkim
Step 4: Creating DMARC Record For the New Domain
To create a DMARC record, go to your DNS manager and add a TXT record. In the name field, enter _dmarc. In the value field, enter the following. Note that you need to create the [email protected] email address.
v=DMARC1; p=none; pct=100; rua=mailto:[email protected]
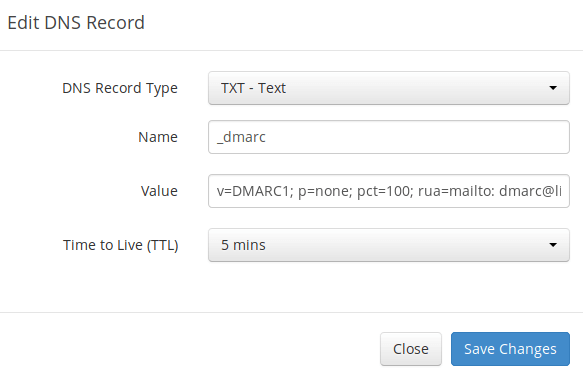
The above DMARC record is a safe starting point. If you want to read a detailed explanation of DMARC, please check the following article.
Step 5: Setting up RoundCube, Postfix and Dovecot for Multiple Domains
I assume you installed Roundcube Webmail for the first mail domain.
It makes sense to let users of the first domain use mail.domain1.com and users of the second domain use mail.domain2.com when using RoundCube webmail. I will show you how to do it with Apache and Nginx.
Apache
If Roundcube is served by Apache web server, then create a virtual host for the second domain.
sudo nano /etc/httpd/conf.d/mail.domain2.com.conf
Put the following text into the file.
<VirtualHost *:80> ServerName mail.domain2.com DocumentRoot /var/www/roundcube/ ErrorLog /var/log/httpd/mail.domain2.com_error.log CustomLog /var/log/httpd/mail.domain2.com_access.log combined <Directory /> Options FollowSymLinks AllowOverride All </Directory> <Directory /var/www/roundcube/> Options FollowSymLinks MultiViews AllowOverride All Order allow,deny allow from all </Directory> </VirtualHost>
Save and close the file. Reload Apache for the changes to take effect.
sudo systemctl reload httpd
Nginx
If Roundcube is served by Nginx web server, then create a virtual host for the second domain.
sudo nano /etc/nginx/conf.d/mail.domain2.com.conf
Put the following text into the file.
server {
listen 80;
server_name mail.domain2.com;
root /var/www/roundcube/;
index index.php index.html index.htm;
error_log /var/log/nginx/roundcube.error;
access_log /var/log/nginx/roundcube.access;
location / {
try_files $uri $uri/ /index.php;
}
location ~ \.php$ {
try_files $uri =404;
fastcgi_pass unix:/run/php-fpm/www.sock;
fastcgi_index index.php;
fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name;
include fastcgi_params;
}
location ~ /.well-known/acme-challenge {
allow all;
}
location ~ ^/(README|INSTALL|LICENSE|CHANGELOG|UPGRADING)$ {
deny all;
}
location ~ ^/(bin|SQL)/ {
deny all;
}
# A long browser cache lifetime can speed up repeat visits to your page
location ~* \.(jpg|jpeg|gif|png|webp|svg|woff|woff2|ttf|css|js|ico|xml)$ {
access_log off;
log_not_found off;
expires 360d;
}
}
Save and close the file. Then test Nginx configurations.
sudo nginx -t
If the test is successful, reload Nginx for the changes to take effect.
sudo systemctl reload nginx
Obtaining TLS Certificate
Now use Certbot to obtain TLS certificate for all your mail domains, so you will have a single TLS certificate with multiple domain names on it and mail clients won’t throw security warnings.
Apache
sudo certbot --apache --agree-tos --redirect --hsts --staple-ocsp -d mail.domain1.com,mail.domain2.com --cert-name mail.domain1.com --email [email protected]
Nginx
sudo certbot --nginx --agree-tos --redirect --hsts --staple-ocsp -d mail.domain1.com,mail.domain2.com --cert-name mail.domain1.com --email [email protected]
Notice that in the above command, we specified the cert name using the first mail domain, which will be used in the file path, so you don’t have to change the file path in Postfix or Dovecot configuration file.
When it asks if you want to update the existing certificate to include the new domain, answer U and hit Enter.
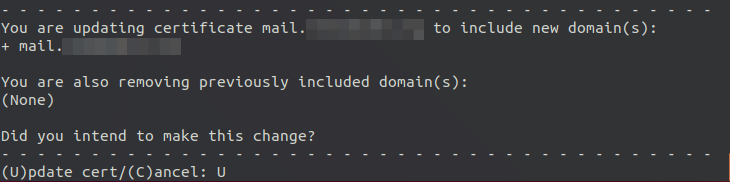
Now you should see the following message, which indicates the multi-domain certificate is successfully obtained.
Run the following command to grant permissions to read Let’s Encrypt TLS certificates.
Apache user
sudo setfacl -R -m u:apache:rx /etc/letsencrypt/live/ /etc/letsencrypt/archive/
Nginx user
sudo setfacl -R -m u:nginx:rx /etc/letsencrypt/live/ /etc/letsencrypt/archive/
Reload Apache or Nginx to pick up the new certificate.
sudo systemctl reload httpd sudo systemctl reload nginx
You should now be able to use different domains to access RoundCube webmail. Also, you need to reload Postfix SMTP server and Dovecot IMAP server in order to let them pick up the new certificate. That’s all you need to do for Postfix and Dovecot to serve multiple domains.
sudo systemctl reload postfix dovecot
Using Mail Client on Your Computer or Mobile Device
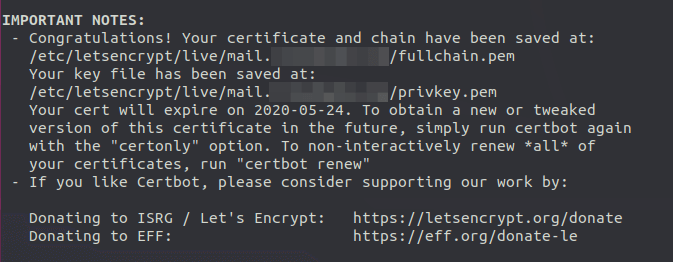
Fire up your desktop email client such as Mozilla Thunderbird and add a mail account of the second domain.
- In the incoming server section, select IMAP protocol, enter
mail.domain2.comas the server name, choose port 143 and STARTTLS. Choosenormal passwordas the authentication method. - In the outgoing section, select SMTP protocol, enter
mail.domain2.comas the server name, choose port 587 and STARTTLS. Choosenormal passwordas the authentication method.
Hint: You can also use port 993 with SSL/TLS encryption for IMAP, and use port 465 with SSL/TLS encryption for SMTP. You should not use port 25 as the SMTP port to submit outgoing emails.
Although Postfix SMTP server and Dovecot IMAP server are using the hostname of the first mail domain (mail.domain1.com) when communicating with others, they are now using a multi-domain certificate, so the mail client won’t display certificate warnings.
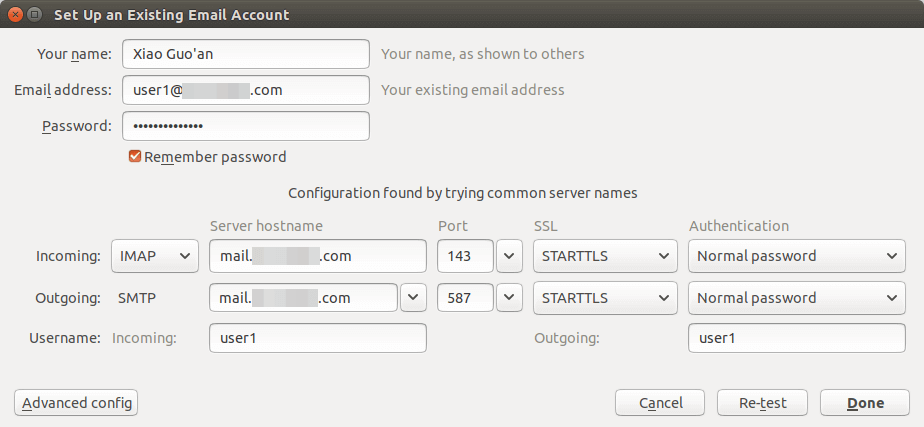
SPF and DKIM Check
Now you can use your desktop email client or webmail client to send a test email to [email protected] and get a free email authentication report. Here’s the report I got from port25.com
Don’t forget to test your email score at https://www.mail-tester.com and also test email placement with GlockApps.
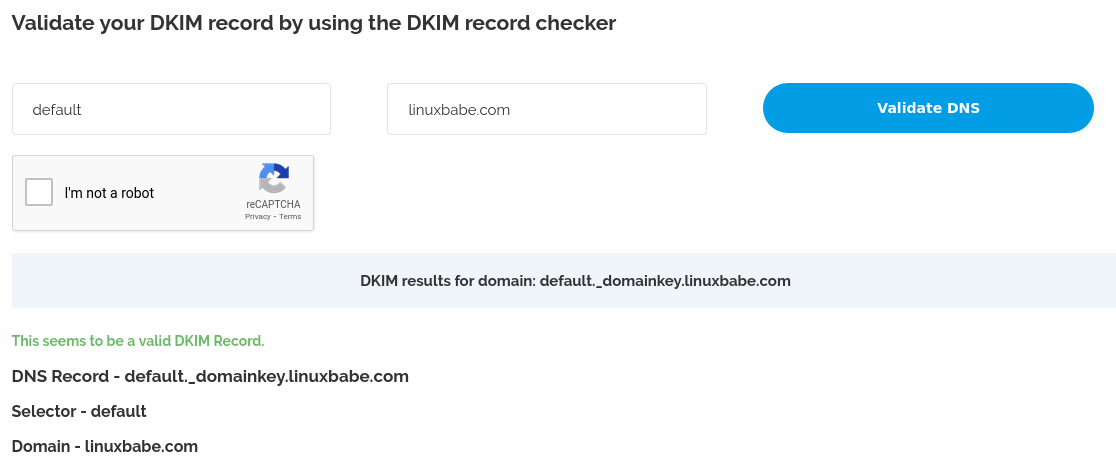
If DKIM check fails, you can go to https://www.dmarcanalyzer.com/dkim/dkim-check/ to see if there are any errors with your DKIM record.
What if Your Emails Are Still Being Marked as Spam?
I have more tips for you in this article: 7 effective tips to stop your emails being marked as spam. Although it requires some time and effort, your emails will eventually be placed in the inbox after applying these tips.
rDNS for Multiple Mail Domains?
Reverse DNS (rDNS), aka PTR record, is used to check if the sender’s IP address matches the HELO hostname. You don’t need to add another PTR record when adding a new mail domain. Your rDNS should be set to just one hostname, i.e. the hostname set in Postfix, which can be shown with the following command.
postconf myhostname
rDNS is a record for IP addresses. It’s not a record for domain name. If you have just one IP address, then you need just one rDNS record pointing to one hostname. Reverse DNS check doesn’t verify what From: domain is in your email, as long as your IP address has an rDNS record and the hostname can resolve back to the same IP address, you can pass reverse DNS check.
Also, you don’t need to change the following settings in Postfix when hosting multiple domains on one server.
- myhostname
- myorigin
- mydestination
Hosted email services like G Suite and Microsoft Exchange Online all use one hostname for a server to send an email for their customers. Emails sent from G Suite users all use google.com in the hostname and emails sent from Microsoft Exchange Online users all use outlook.com in the hostname. This is also true for other email service providers like Mailchimp, SendinBlue, SendPluse, etc. They all use one hostname for a single server and one IP address has just one rDNS record.
Multiple TLS Certificates
If you manage email servers for lots of clients, you might not want to bundle all TLS certificates into one file, as it tells the information of your clients. Instead of using the following command to obtain a multi-domain certificate,
sudo certbot --nginx --agree-tos --redirect --hsts --staple-ocsp -d mail.domain1.com,mail.domain2.com
You can just use the following command to obtain a separate TLS certificate for the second mail domain.
sudo certbot --nginx --agree-tos --redirect --hsts --staple-ocsp -d mail.domain2.com
Next, you need to configure Postfix and Dovecot.
Postfix Multiple TLS Certificates
If you use Postfix version 3.4 or higher, you can use multiple TLS certificates. Edit the main.cf file.
sudo nano /etc/postfix/main.cf
Add the following line at the end of this file to enable multiple TLS certificates.
tls_server_sni_maps = hash:/etc/postfix/sni_maps
Save and close the file. Then create the sni_maps file.
sudo nano /etc/postfix/sni_maps
In this file, add each mail hostname and its certificate file.
mail.domain1.com /etc/letsencrypt/live/mail.domain1.com/privkey.pem /etc/letsencrypt/live/mail.domain1.com/fullchain.pem mail.domain2.com /etc/letsencrypt/live/mail.domain2.com/privkey.pem /etc/letsencrypt/live/mail.domain2.com/fullchain.pem
Save and close the file. Next, build the lookup table.
sudo postmap -F /etc/postfix/sni_maps
Restart Postfix.
sudo systemctl restart postfix
You must use the -F option in postmap to base64-decode each value in the SNI map, or Postfix will throw the malformed BASE64 value error in the /var/log/mail.log file. The following command is wrong.
sudo postmap /etc/postfix/sni_maps
Dovecot Multiple TLS Certificates
If you use multiple TLS certificates in Postfix, you should also enable it in Dovecot. Edit the Dovecot 10-ssl.conf file.
sudo nano /etc/dovecot/conf.d/10-ssl.conf
You can find the following lines.
ssl_cert =</etc/letsencrypt/live/mail.domain1.com/fullchain.pem ssl_key =</etc/letsencrypt/live/mail.domain1.com/privkey.pem
Then add the following lines.
local_name mail.domain1.com { ssl_cert =</etc/letsencrypt/live/mail.domain1.com/fullchain.pem ssl_key =</etc/letsencrypt/live/mail.domain1.com/privkey.pem } local_name mail.domain2.com { ssl_cert =</etc/letsencrypt/live/mail.domain2.com/fullchain.pem ssl_key =</etc/letsencrypt/live/mail.domain2.com/privkey.pem }
Save and close the file. Then restart Dovecot.
sudo systemctl restart dovecot
Run the following command to grant permissions to read Let’s Encrypt TLS certificates.
Apache user
sudo setfacl -R -m u:apache:rx /etc/letsencrypt/live/ /etc/letsencrypt/archive/
Nginx user
sudo setfacl -R -m u:nginx:rx /etc/letsencrypt/live/ /etc/letsencrypt/archive/
Cron Job
If you use SNI map in Postfix, then you should run the sudo postmap -F /etc/postfix/sni_maps command after TLS certificate is renewed. If you don’t do this, then email clients might complain your TLS certificate has expired. You can add this command to Crontab file, so it will be automated.
sudo crontab -e
Apache web server user:
@daily certbot renew --quiet; /usr/sbin/postmap -F /etc/postfix/sni_maps; systemctl reload postfix dovecot httpd
Nginx web server user:
@daily certbot renew --quiet; /usr/sbin/postmap -F /etc/postfix/sni_maps; systemctl reload postfix dovecot nginx
Wrapping Up
That’s it! I hope this tutorial helped you host multiple email domains with PostfixAdmin. As always, if you found this post useful, then subscribe to our free newsletter to get more tips and tricks. Take care 🙂



Will the fact that I have one server hosting multiple domains cause an issue with dkim or spamassian or any other item. The PRT record for the IP points to the mail server and it’s domain. Will adding additional domains cause problems with mail delivery?
If you follow my tutorial and get a 10/10 score on each domain name, it will not create any problem.
Hi,
I’ve added my second domain.
I have the error message “postfix/smtpd[12493]: NOQUEUE: reject: RCPT […] Relay access denied; […]” in my “/var/log/maillog” with other lines “warning: connect to Milter service inet:127.0.0.1:8893: Connection refused”
I don’t know where is the problem. I can send email from my second domain with Roundcube (on this server), but i can’t send with thunderbird : REJECTED.
Can you help me ? I don’t find the solution…
Thanks for your wonderful documentation !
My bad, I configured Thunderbird with port 25 for SMTP. With the use of port 587, it’s working better.
How do I fix the issue with DKIM & SPF not passing for virtual domains, because they’re sent using the mail server domain?
So, my mail server is: mail.domain1.com, and has been set up in line with everything from your tutorial.
Virtual domain: domain2.com with email: [email protected] – email sent to gmail address states SPF as neutral, and then in my server logs it states that there no signing table match / no signature data for ‘[email protected]’ (because the data in the signing table is set to email addresses with “@domain1.com” in them).
Is there a way for the steps from this tutorial to be automated when adding new domains with postfix admin? So, when adding domains to postfix admin the “Create Signing Table, Key Table and Trusted Hosts File”, “Generate Private/Public Keypair” & “Publish Your Public Key in DNS Records” steps are done automatically and the data for DNS TXT records is emailed to a specific email address so that who ever is in charge of setting up DNS related tasks can simply add the correct TXT record to the DNS records.
Is this possible?
Thanks – great tutorial by the way. I’ve learnt a lot more about what’s going on behind the scenes by following your tutorials!
Matt
If you followed step 3 correctly, then emails sent from domain2.com will be DKIM signed.
PostfixAdmin doesn’t provide an automatic way to add new domains for DKIM signing. Modoboa is better. However, Modoboa currently doesn’t support CentOS 8.
Hello,
Quick question, in Part 3 (https://www.linuxbabe.com/redhat/postfixadmin-create-virtual-mailboxes-centos-mail-server), under Step 7, the certbot command installs a certification that points to postfixadmin.example.com:
yet, on the current page, the command is
If I went through Part 3, successfully, should I keep the ‘-d postfixadmin.example.com,’ whereby the command would thus be
or, should I change it to what is outlined on this current page? I just wanted clarification before trying the command.
Also, I love your webpage. I have learned so much from you. Thank you, so much!
The postfixadmin.domain1.com should used by admin only. End-users don’t need to visit this sub-domain. They only need to access the
mailsub-domains, which should be included in the certificate. Thepostfixadminsub-domain doesn’t need to be included in the certificate.By the way,
/usr/local/bin/certbotshould be changed to justcertbot. I forgot to update it in this article.Thank you for clarifying. I really appreciate your time!
I am sory for my bad english, this my problem, with postfix in linux
I work in a single vps, with two wordpress, ” contact form send mail just for mail “[email protected]”,
if I change file sasl_passwd like this contact form send mail just for "[email protected]",:
echo "this is the mail2" | sendmail -F "Bogus User" -f [email protected] [email protected]
echo "this is the mail2" | sendmail -F "Bogus User" -f [email protected] [email protected]
so I need find problem with config wordpress or config postfix ?
if there solution how send message from both wordpress, please help,
Suppose you have a WordPress VPS and another mail server VPS, here are the steps for relaying emails for your WordPress sites through the mail server.
First, install Postfix on the WordPress VPS.
Then, you need a
sender_dependent_relayhost_mapin your/etc/postfix/main.cffile.Next, in the
/etc/postfix/relay_by_senderfile, add the following lines.Then, create the
/etc/postfix/sasl_passwdfile.Save and close the file.
Build the hash table.
Also add the following lines to
/etc/postfix/main.cffile.Restart Postfix for the changes to take effect.
Howto deal with a password hash migration?
Let’s say from something to Argon2
As far as I can tell, Dovecot on CentOS/Rocky Linux/Alma Linux doesn’t support ARGON2.
Dear Xiao
I am sorry for my bad English, this my problem, with postfix in Centos 8 Linux
Please help me,
I want to using mail server two domains (mail.domain1.com, mail.domain2.com) on the one server (one public ip address).
After creating a new ssl and configuring it (certbot –nginx –agree-tos –redirect –hsts –staple-ocsp -d mail.domain1.com, certbot –nginx –agree-tos –redirect –hsts –staple-ocsp -d mail.domain2.com), I can’t log in to postfix anymore.
Check the error log to see if this error has occurred.
2022/09/19 15:07:44 [error] 2367#0: *1 FastCGI sent in stderr: "PHP message: Failed to read password from /usr/bin/doveadm pw -r 3 -s SCRAM-SHA-256 ... stderr: doveconf: Fatal: Error in configuration file /etc/dovecot/conf.d/10-ssl.conf line 15: ssl_key: Can't open file /etc/letsencrypt/live/mail.domain1.com/privkey.pem: Permission denied , password: PHP message: Error while trying to call pacrypt()PHP message: Exception: /usr/bin/doveadm pw -r 3 -s SCRAM-SHA-256 failed, see error log for details in /var/spool/postfixadmin/functions.inc.php:1059 Stack trace: #0 /var/spool/postfixadmin/functions.inc.php(1274): _pacrypt_dovecot() #1 /var/spool/postfixadmin/model/Login.php(36): pacrypt() #2 /var/spool/postfixadmin/public/login.php(63): Login->login() #3 {main}PHP message: PostfixAdmin admin login failed (username: [email protected], ip_address: 202.126.94.26)" while reading response header from upstream, client: xx.xx.xx.xx, server: www.postfixadmin.domain1.com, request: "POST /login.php HTTP/1.1", upstream: "fastcgi://unix:/run/php-fpm/www.sock:", host: "postfixadmin.domain1.com", referrer: "https://postfixadmin.domain1.com/login.php"Another issue, thing is can logging in with an email created [email protected] on a mail.domain1.com name.
[email protected] should refer to mail.domain1.com, and [email protected] to mail.domain2.com right? How to set it up?
Also, I love your webpage. I have learned so much from you. Thank you, so much!
Run the following command to grant permissions to read Let’s Encrypt TLS certificates.
Apache user
Nginx user
You can create another admin user ([email protected]) in PostfixAdmin after login.