Setup OwnCloud 9 Server with Nginx, MariaDB and PHP7 on Arch Linux
A reader asked me how to set up ownCloud personal cloud storage on Arch Linux with Nginx, MariaDB and PHP7. Today I’m going to show you how to achieve that. You can follow this guide on a Arch Linux server or your Arch desktop.
This tutorial assumes that you have already configured a LEMP stack on Arch Linux. If you haven’t done so, please check out the below easy-to-follow guide to see how to do it.
Install (LEMP) Nginx, MariaDB, PHP7 on Arch Linux
When you are finished setting up LEMP stack, come back here. If you encounter any errors in the process, let me know in the comment section.
Step 1: Install ownCloud 9 Server on Arch Linux
ownCloud is in the Arch Linux community repository, so we can install it using pacman:
sudo pacman -S owncloud
The above command also installs php-gd, the graphics library. GD stands for Graphics Draw. OwnCloud program files are stored in /usr/share/webapps/owncloud directory. We need to set http as the owner of webapps directory so Nginx can write to this directory.
sudo chown http:http /usr/share/webapps/ -R
Step 2: Create a Database and User for ownCloud
Log into MariaDB database server:
mysql -u root -p
Then create a database for owncloud.
create database owncloud;
You can check out all your databases with:
show databases;
Now create a database user on localhost for ownCloud database. Replace password with your preferred password.
create user ownclouduser@localhost identified by 'password';
Grant this user all privileges on owncloud database.
grant all privileges on owncloud.* to ownclouduser@localhost identified by 'password';
Flush privileges and exit.
flush privileges; exit;
Step 3: Enable Binary Logging in MariaDB
Open my.cnf file.
sudo nano /etc/mysql/my.cnf
Add the following two lines in [mysqld] section. You may find that these two lines are already there (line 54 and 57) because the MariaDB package of Arch Linux enables binary logging by default. If you cannot find them, then manually add them to my.cnf file.
log-bin = mysql-bin binlog_format = mixed
The format of binary log must be mixed. Save and close the file. Then reload MariaDB service.
sudo systemctl reload mysqld or sudo systemctl restart mysqld
Step 4: Get A Free SSL Certificate from Let’s Encrypt
This step is only necessary on a server because you want to make sure your ownCloud username and password are not sniffed by malicious people. Skip it if you are setting up ownCloud on your home computer.
First we need to install the letsencrypt client which is available in Arch Linux community repository.
sudo pacman -S letsencrypt
Then use the webroot plugin to obtain a certificate for Nginx Web server.
sudo letsencrypt certonly --webroot --email <your-email-address> -d owncloud.your-domain.com -w /usr/share/nginx/html/
I assume you are using a domain name like owncloud.your-domain.com to access the ownCloud web interface. You also need to point your domain name to your server IP in DNS before running the above command.
certonly means the client obtains SSL certificate but will not install it. Because Let’s Encrypt is still in beta and does not support auto SSL configuration for Nginx, so we have to manually configure(install) SSL.
Your SSL certificate will be saved under /etc/letsencrypt/live/owncloud.your-domain.com directory.
If you see a 403 forbidden error after running the above command, that’s probably because your Nginx configurations doesn’t allow access to hidden files. To enable access to your-web-root/.well-known/acme-challenge, add the following directive to your Nginx config file.
location ~ /.well-known/acme-challenge {
allow all;
}
Then reload Nginx configuration.
sudo systemctl reload nginx
And run the letsencrypt command again to obtain your certificate.
Step 5: Create a Nginx Config File for owncloud
First, create a conf.d directory for individual Nginx config files.
sudo mkdir /etc/nginx/conf.d
Then create a config file for ownCloud.
sudo nano /etc/nginx/conf.d/owncloud.conf
Put the following text into the file.
upstream php-handler {
#server 127.0.0.1:9000;
server unix:/run/php-fpm/php-fpm.sock;
}
server {
listen 80;
server_name owncloud.your-domain.com;
# enforce https
return 301 https://$server_name$request_uri;
}
server {
listen 443 ssl;
server_name owncloud.your-domain.com;
ssl_certificate /etc/letsencrypt/live/owncloud.your-domain.com/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/live/owncloud.your-domain.com/privkey.pem;
# Add headers to serve security related headers
add_header Strict-Transport-Security "max-age=15768000; includeSubDomains; preload;";
add_header X-Content-Type-Options nosniff;
add_header X-Frame-Options "SAMEORIGIN";
add_header X-XSS-Protection "1; mode=block";
add_header X-Robots-Tag none;
# Path to the root of your installation
root /usr/share/webapps/owncloud;
# set max upload size
client_max_body_size 10G;
fastcgi_buffers 64 4K;
# Disable gzip to avoid the removal of the ETag header
gzip off;
# Uncomment if your server is build with the ngx_pagespeed module
# This module is currently not supported.
#pagespeed off;
index index.php;
error_page 403 /core/templates/403.php;
error_page 404 /core/templates/404.php;
rewrite ^/.well-known/carddav /remote.php/carddav/ permanent;
rewrite ^/.well-known/caldav /remote.php/caldav/ permanent;
# The following 2 rules are only needed for the user_webfinger app.
# Uncomment it if you're planning to use this app.
#rewrite ^/.well-known/host-meta /public.php?service=host-meta last;
#rewrite ^/.well-known/host-meta.json /public.php?service=host-meta-json last;
location = /robots.txt {
allow all;
log_not_found off;
access_log off;
}
location ~ ^/(build|tests|config|lib|3rdparty|templates|data)/ {
deny all;
}
location ~ ^/(?:\.|autotest|occ|issue|indie|db_|console) {
deny all;
}
location / {
rewrite ^/remote/(.*) /remote.php last;
rewrite ^(/core/doc/[^\/]+/)$ $1/index.html;
try_files $uri $uri/ =404;
}
location ~ \.php(?:$|/) {
fastcgi_split_path_info ^(.+\.php)(/.+)$;
include fastcgi_params;
fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name;
fastcgi_param PATH_INFO $fastcgi_path_info;
fastcgi_param HTTPS on;
fastcgi_param modHeadersAvailable true; #Avoid sending the security headers twice
fastcgi_pass php-handler;
fastcgi_intercept_errors on;
}
# Adding the cache control header for js and css files
# Make sure it is BELOW the location ~ \.php(?:$|/) { block
location ~* \.(?:css|js)$ {
add_header Cache-Control "public, max-age=7200";
# Add headers to serve security related headers
add_header Strict-Transport-Security "max-age=15768000; includeSubDomains; preload;";
add_header X-Content-Type-Options nosniff;
add_header X-Frame-Options "SAMEORIGIN";
add_header X-XSS-Protection "1; mode=block";
add_header X-Robots-Tag none;
# Optional: Don't log access to assets
access_log off;
}
# Optional: Don't log access to other assets
location ~* \.(?:jpg|jpeg|gif|bmp|ico|png|swf)$ {
access_log off;
}
}
Replace the red-colored text with your actual data. This configuration file assumes that your php-fpm process listens on Unix socket. If your php-fpm listens on 127.0.0.1:9000, you need to change the upstream section.
If you are setting up ownCloud on your home computer:
- You need to configure it to only listen on port 80
- server_name will be set to 127.0.0.1 or localhost.
- SSL configurations are not needed.
Next, edit /etc/nginx/nginx.conf file
sudo nano /etc/nginx/nginx.conf
Add this line in the http section.
include /etc/nginx/conf.d/*.conf;
Like this:
http {
include /etc/nginx/conf.d/*.conf;
include mime.types;
default_type application/octet-stream;
.....
Save and close the file. Then reload Nginx.
sudo systemctl reload nginx
Step 6: Enable PHP Modules
ownCloud requires mysql and gd modules to be enabled in order to work properly.
Edit php.ini file.
sudo nano /etc/php/php.ini
Find the following 3 lines. Remove the semicolons to enable these 3 modules.
;extension=gd.so (line 869) ;extension=mysqli.so (line 877) ;extension=pdo_mysql.so (line 881)
Save and close the file. Then reload php-fpm process.
sudo systemctl reload php-fpm
Step 7: Setup the Web Interface
In your browser address bar, type
owncloud.your-domain.com
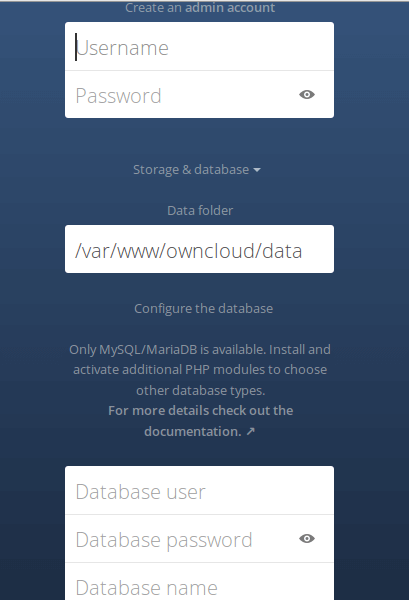
or 127.0.0.1 if you are configuring on a home computer. You need to create an administrative account and connect ownCloud service with MariaDB database. Enter the database username, password and database name you created earlier.
Once it’s done, you will enter the Web interface of ownCloud.
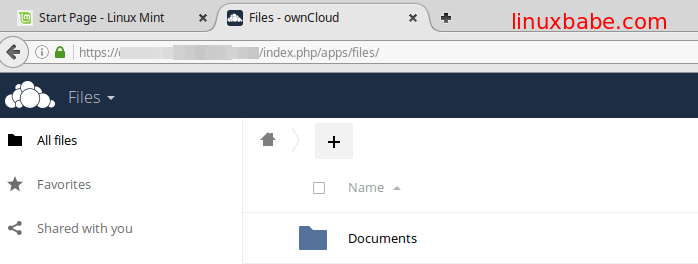
Congrats! You can now start using ownCloud as your private cloud storage. Don’t forget to install ownCloud client on your Linux desktop or your smart phone. The desktop client can be installed on Arch Linux with:
sudo pacman -S owncloud-client
Comments, questions or suggestions are always welcome. If you found this post useful, ? please share it with your friends on social media! Stay tuned for more Linux tutorials.



Thanks. It works! Only letsencrypt package is called now certbot. And in owncloud.conf file root dir is wrong: use the path /usr/share/webapps/owncloud.
Dont forghet to backup your generated cert keys!
Amazing it run perfect and fast
Thanks for pointing out the error. I updated the root dir in owncloud.conf
HI,
i have a issue in step 5 when i try to reload nginx. I have the message : ” unknown directive “uptream” in my owncloud config file.
Have you an idea why ?
It should be upstream instead of uptream.
Hi, thanx for this Tutorial.
Modify /etc/php/php-fpm.d/www.conf uncommenting the following: env[PATH] = /usr/local/bin:/usr/bin:/bin -> to fix the Warning in Admin Panel
But still the Mobile and the Desktop Clients do only work for the Admin. When i create a new Group or User it is not working, can you test and figure out whats wrong?
Is Owncloud still the Thing, what about that NextCloud?
I have the problem that OwnCloud tells me
Can’t write into config directory!
This can usually be fixed by giving the webserver write access to the config directory.
although I have given the permissions to the http user many times. Any ideas why that could be?
It would also be great if you could write an up-to-date guide!
this also may be rwalted to systemd file strict prorection, just add some lines in [Sevice] section, and this dirs can be writed by php-fpm, for example lines are
ReadWritePaths=/etc/webapps/owncloud/config
ReadWritePaths=/usr/share/webapps/owncloud
this also may be realted to systemd filesystem protection, just add some lines in [Sevice] section, and this dirs can be writed by php-fpm, for example lines are
ReadWritePaths=/etc/webapps/owncloud/config
ReadWritePaths=/usr/share/webapps/owncloud