Install Roundcube Webmail on Ubuntu 22.04/20.04 with Apache/Nginx
Roundcube is a free open-source, full-featured webmail client written in PHP. A webmail is a mail client in your browser. Instead of reading and sending emails from a desktop mail client like Mozilla Thunderbird, you can access your email from a web browser. This tutorial is going to show you how to install Roundcube webmail on Ubuntu 22.04/20.04 with Apache or Nginx web server.
Roundcube Features
Roundcube functionality includes:
- Address book
- Folder management
- Message searching
- Message filter
- Spell checking
- MIME support
- PGP encryption and signing
- Mailvelope integration
- Users are able to change their passwords in Roundcube.
- Import MIME or Mbox formatted emails.
- Email Resent (Bounce)
- Support for Redis and Memcached cache
- Support for SMTPUTF8 and GSSAPI
- A responsive skin called Elastic with full mobile device support
- OAuth2/XOauth support (with plugin hooks)
- Collected recipients and trusted senders
- Full unicode support with MySQL database
- Support of IMAP LITERAL- extension
Requirements
To follow this tutorial, it’s assumed that
- Postfix SMTP server and Dovecot IMAP server have been installed on your Ubuntu 22.04/20.04 server
- You have already installed a LAMP stack or LEMP stack on Ubuntu 22.04/20.04 server.
If not, please click the above links and follow the instructions to complete prerequisites. Note that if you set up your email server using iRedMail before, then your server meets all requirements and Roundcube is already installed on your server.
Now let’s proceed to install Roundcube.
Step 1: Download Roundcube Webmail on Ubuntu 22.04/20.04
Log in to your Ubuntu server via SSH, then run the following command to download the latest 1.6 stable version from Roundcube Github repository.
wget https://github.com/roundcube/roundcubemail/releases/download/1.6.0/roundcubemail-1.6.0-complete.tar.gz
Note: You can always use the above URL format to download Roundcube from command line. If a new version comes out, simply replace 1.6.0 with the new version number. You can check if there’s a new release on Roundcube downloade page.
Extract the tarball, and move the newly created folder to web root (/var/www/) and rename it as roundcube at the same time.
tar xvf roundcubemail-1.6.0-complete.tar.gz sudo mkdir -p /var/www/ sudo mv roundcubemail-1.6.0 /var/www/roundcube
Change into the roundcube directory.
cd /var/www/roundcube
Make the web server user (www-data) as the owner of the temp and logs directory so that web server can write to these two directories.
sudo chown www-data:www-data temp/ logs/ -R
Step 2: Install PHP Extensions
Run the following command to install the required PHP extensions. PHP8.1 is fully supported in the 1.6 release.
sudo apt install software-properties-common sudo add-apt-repository ppa:ondrej/php sudo apt update sudo apt install php-net-ldap2 php-net-ldap3 php-imagick php8.1-common php8.1-gd php8.1-imap php8.1-mysql php8.1-curl php8.1-zip php8.1-xml php8.1-mbstring php8.1-bz2 php8.1-intl php8.1-gmp php8.1-redis
Step 3: Create a MariaDB Database and User for Roundcube
Log into MariaDB shell as root.
sudo mysql -u root
Then create a new database for Roundcube using the following command. This tutorial name it roundcubemail, you can use whatever name you like for the database.
CREATE DATABASE roundcubemail DEFAULT CHARACTER SET utf8 COLLATE utf8_general_ci;
Next, create a new database user on localhost using the following command. Again, this tutorial name it roundcube, you can use whatever name you like. Replace password with your preferred password.
CREATE USER roundcube@localhost IDENTIFIED BY 'roundcube_password';
Then grant all permission of the new database to the new user so later on Roundcube webmail can write to the database.
GRANT ALL PRIVILEGES ON roundcubemail.* TO roundcube@localhost;
Flush the privileges table for the changes to take effect.
flush privileges;
Exit MariaDB Shell:
exit;
Import the initial tables to roundcube database.
sudo mysql roundcube < /var/www/roundcube/SQL/mysql.initial.sql
Step 4: Create Apache Virtual Host or Nginx Config File for Roundcube
Apache
If you use Apache web server, create a virtual host for Roundcube.
sudo nano /etc/apache2/sites-available/roundcube.conf
Note: If you followed my Postfix/Dovecot tutorial, a virtual host already exists. you should edit the following file. (Delete the existing content.)
sudo nano /etc/apache2/sites-available/mail.example.com.conf
Put the following text into the file. Replace mail.example.com with your real domain name and don’t forget to set DNS A record for it.
<VirtualHost *:80>
ServerName mail.example.com
DocumentRoot /var/www/roundcube/
ErrorLog ${APACHE_LOG_DIR}/roundcube_error.log
CustomLog ${APACHE_LOG_DIR}/roundcube_access.log combined
<Directory />
Options FollowSymLinks
AllowOverride All
</Directory>
<Directory /var/www/roundcube/>
Options FollowSymLinks MultiViews
AllowOverride All
Order allow,deny
allow from all
</Directory>
</VirtualHost>
Save and close the file. Then enable this virtual host with:
sudo a2ensite roundcube.conf
Reload Apache for the changes to take effect.
sudo systemctl reload apache2
Now you should be able to see the Roundcube web-based install wizard at http://mail.example.com/installer.
Nginx
If you use Nginx web server, create a virtual host for Roundcube.
sudo nano /etc/nginx/conf.d/roundcube.conf
Note: If you followed my Postfix/Dovecot tutorial, a virtual host already exists. you should edit the following file. (Delete the existing content.)
sudo nano /etc/nginx/conf.d/mail.example.com.conf
Put the following text into the file. Replace the domain name and don’t forget to set DNS A record for it.
server {
listen 80;
listen [::]:80;
server_name mail.example.com;
root /var/www/roundcube/;
index index.php index.html index.htm;
error_log /var/log/nginx/roundcube.error;
access_log /var/log/nginx/roundcube.access;
location / {
try_files $uri $uri/ /index.php;
}
location ~ \.php$ {
try_files $uri =404;
fastcgi_pass unix:/run/php/php8.1-fpm.sock;
fastcgi_index index.php;
fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name;
include fastcgi_params;
}
location ~ /.well-known/acme-challenge {
allow all;
}
location ~ ^/(README|INSTALL|LICENSE|CHANGELOG|UPGRADING)$ {
deny all;
}
location ~ ^/(bin|SQL)/ {
deny all;
}
# A long browser cache lifetime can speed up repeat visits to your page
location ~* \.(jpg|jpeg|gif|png|webp|svg|woff|woff2|ttf|css|js|ico|xml)$ {
access_log off;
log_not_found off;
expires 360d;
}
}
Save and close the file. Then test Nginx configurations.
sudo nginx -t
If the test is successful, reload Nginx for the changes to take effect.
sudo systemctl reload nginx
Now you should be able to see the Roundcube web-based install wizard at http://mail.example.com/installer.
Step 5: Enabling HTTPS
It’s highly recommended that you use TLS to encrypt your webmail. We can enable HTTPS by installing a free TLS certificate issued from Let’s Encrypt. Run the following command to install Let’s Encrypt client (certbot) on Ubuntu 22.04/20.04 server.
sudo apt install certbot
If you use Nginx, then you also need to install the Certbot Nginx plugin.
sudo apt install python3-certbot-nginx
Next, run the following command to obtain and install TLS certificate.
sudo certbot --nginx --agree-tos --redirect --hsts --staple-ocsp --email [email protected] -d mail.example.com
If you use Apache, install the Certbot Apache plugin.
sudo apt install python3-certbot-apache
And run this command to obtain and install TLS certificate.
sudo certbot --apache --agree-tos --redirect --hsts --staple-ocsp --email [email protected] -d mail.example.com
Where
--nginx: Use the nginx plugin.--apache: Use the Apache plugin.--agree-tos: Agree to terms of service.--redirect: Force HTTPS by 301 redirect.--hsts: Add the Strict-Transport-Security header to every HTTP response. Forcing browser to always use TLS for the domain. Defends against SSL/TLS Stripping.--staple-ocsp: Enables OCSP Stapling. A valid OCSP response is stapled to the certificate that the server offers during TLS.
The certificate should now be obtained and automatically installed.
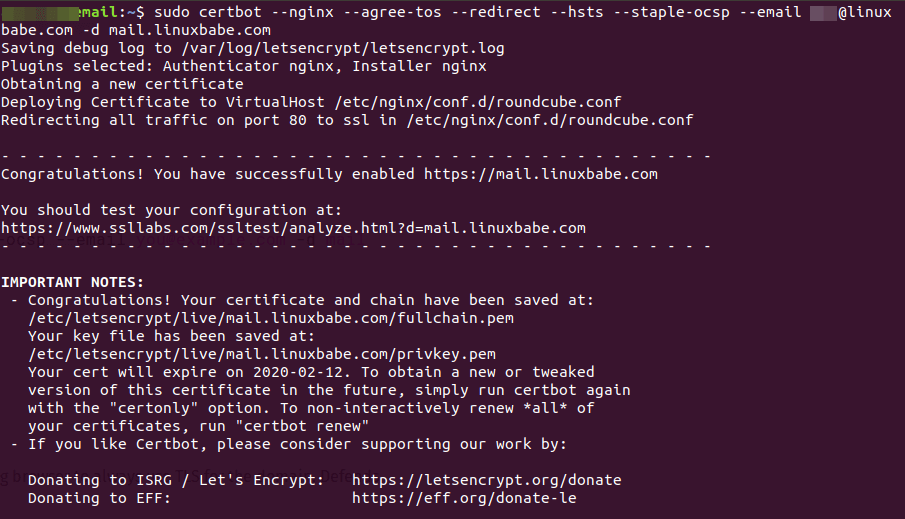
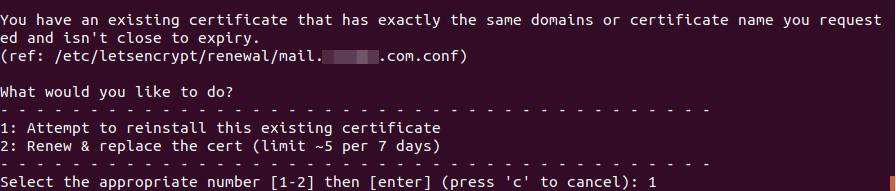
Note: If you followed my Postfix/Dovecot tutorial, and now you install Roundcube on the same server, then certbot will probably tell you that a certificate for mail.example.com already exists as shown below, so you can choose to install the existing TLS certificate to your web server configuration file.
Step 6: Adding Local DNS Entry
It’s recommended to edit the /etc/hosts file on the mail server and add the following entry, so that Roundcube won’t have to query the public DNS, which will speed up web page loading a little bit.
127.0.0.1 localhost mail.example.com
Step 7: Configure Roundcube
Go to the Roundcube configuration directory.
cd /var/www/roundcube/config/
Copy the sample configuration file.
sudo cp config.inc.php.sample config.inc.php
Edit the new file.
sudo nano config.inc.php
Find the following line, which tells Roundcube how to connect to the database.
$config['db_dsnw'] = 'mysql://roundcube:pass@localhost/roundcubemail';
You need to replace pass with the real Roundcube password. If the password contains special characters, you need to use percent encoding. For example, if the password is mPcEIRxyJhCz8uiWIUopqWzaSTk=, then the line will look like this:
$config['db_dsnw'] = 'mysql://roundcube:mPcEIRxyJhCz8uiWIUopqWzaSTk%3D@localhost/roundcubemail';
The special character = is represented by %3D.
Then find the following two lines.
$config['imap_host'] = 'localhost:143'; $config['smtp_host'] = 'localhost:587';
Replace the value as follows:
$config['imap_host'] = 'tls://mail.example.com:143'; $config['smtp_host'] = 'tls://mail.example.com:587';
Find the following line.
$config['des_key'] = 'rcmail-!24ByteDESkey*Str';
Replace the default key with some random characters like below.
$config['des_key'] = '58kptbzEcNKi/bc9OL90//3ATnQ=';
Next, find the following lines
// List of active plugins (in plugins/ directory)
$config['plugins'] = [
'archive',
'zipdownload',
];
By default, only two plugins are enabled. We can enable more plugins like below.
// List of active plugins (in plugins/ directory) $config['plugins'] = ['acl', 'additional_message_headers', 'archive', 'attachment_reminder', 'autologon', 'debug_logger', 'emoticons', 'enigma', 'filesystem_attachments', 'help', 'hide_blockquote', 'http_authentication', 'identicon', 'identity_select', 'jqueryui', 'krb_authentication', 'managesieve', 'markasjunk', 'new_user_dialog', 'new_user_identity', 'newmail_notifier', 'password', 'reconnect', 'redundant_attachments', 'show_additional_headers', 'squirrelmail_usercopy', 'subscriptions_option', 'userinfo', 'vcard_attachments', 'virtuser_file', 'virtuser_query', 'zipdownload'];
Finally, we can enable the built-in spell-checker by adding the following line at the end of this file.
$config['enable_spellcheck'] = true;
Save and close the file.
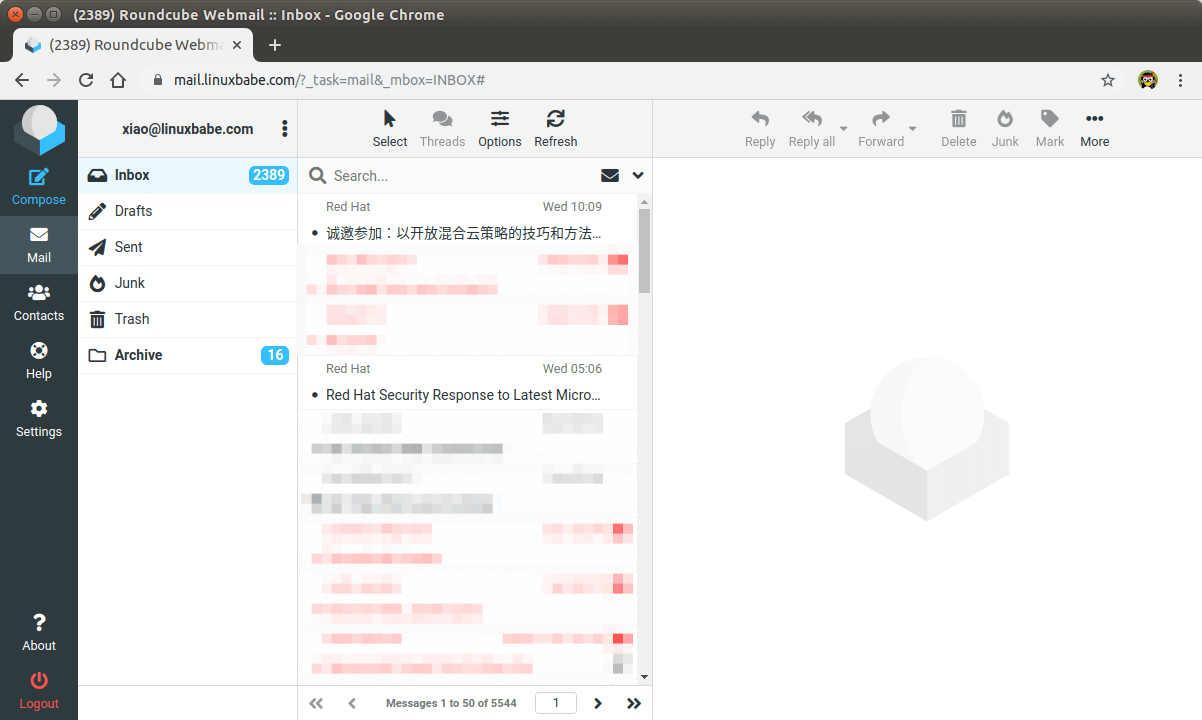
Go to your Webmail domain and log in.
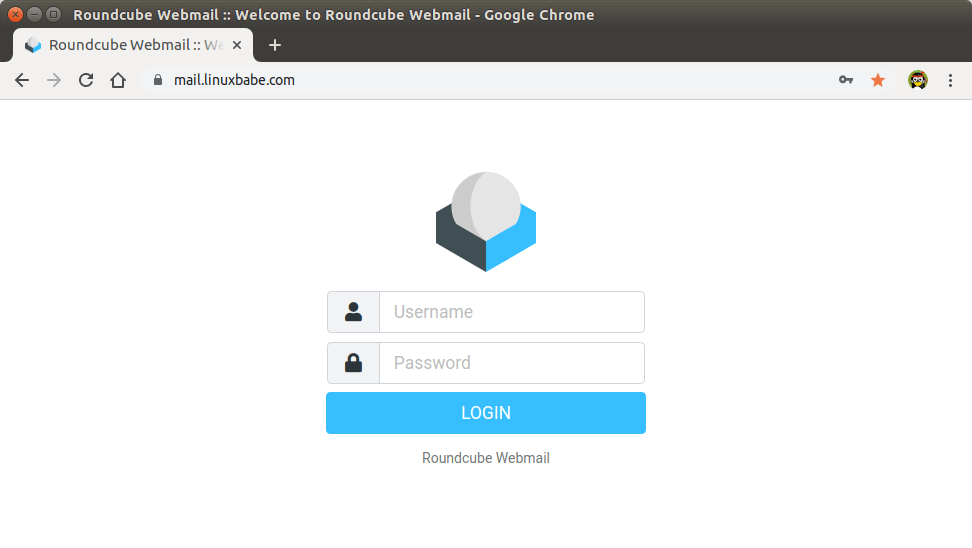
Roundcube Webmail interface
Now you should remove the whole installer folder from the document root or make sure that enable_installer option in config.inc.php file is disabled.
sudo rm /var/www/roundcube/installer/ -r
These files may expose sensitive configuration data like server passwords and encryption keys to the public. Make sure you cannot access the installer page from your browser.
Step 8: Configure the Sieve Message Filter
You can create folders in Roundcube webmail and then create rules to filter email messages into different folders. In order to do this, you need to install the ManageSieve server with the following command.
sudo apt install dovecot-sieve dovecot-managesieved
By default, Postfix uses its builtin local delivery agent (LDA) to move inbound emails to the message store (inbox, sent, trash, Junk, etc). We can configure it to use Dovecot to deliver emails, via the LMTP protocol, which is a simplified version of SMTP. LMTP allows for a highly scalable and reliable mail system and it is required if you want to use the sieve plugin to filter inbound messages to different folders.
Install the Dovecot LMTP Server.
sudo apt install dovecot-lmtpd
Edit the Dovecot main configuration file.
sudo nano /etc/dovecot/dovecot.conf
Add lmtp and sieve to the supported protocols.
protocols = imap lmtp sieve
Save and close the file. Then edit the Dovecot 10-master.conf file.
sudo nano /etc/dovecot/conf.d/10-master.conf
Change the lmtp service definition to the following.
service lmtp {
unix_listener /var/spool/postfix/private/dovecot-lmtp {
group = postfix
mode = 0600
user = postfix
}
}
Next, edit the Postfix main configuration file.
sudo nano /etc/postfix/main.cf
Add the following lines at the end of the file. The first line tells Postfix to deliver emails to local message store via the dovecot LMTP server. The second line disables SMTPUTF8 in Postfix, because Dovecot-LMTP doesn’t support this email extension.
mailbox_transport = lmtp:unix:private/dovecot-lmtp smtputf8_enable = no
Save and close the file. Open the /etc/dovecot/conf.d/15-lda.conf file.
sudo nano /etc/dovecot/conf.d/15-lda.conf
Scroll to the end of the file, uncomment the mail_plugins line and add the sieve plugin to local delivery agent (LDA).
protocol lda {
# Space separated list of plugins to load (default is global mail_plugins).
mail_plugins = $mail_plugins sieve
}
Save and close the file. If you can find the 20-lmtp.conf file under /etc/dovecot/conf.d/ directory, then you should also enable the sieve plugin in that file like below.
protocol lmtp {
mail_plugins = quota sieve
}
Edit the /etc/dovecot/conf.d/10-mail.conf file.
sudo nano /etc/dovecot/conf.d/10-mail.conf
Sieve scripts are stored under each user’s home directory. If you followed my PostfixAdmin tutorial and are using virtual mailbox domains, then you need to enable mail_home for the virtual users by adding the following line in the file, because virtual users don’t have home directories by default.
mail_home = /var/vmail/%d/%n
Save and close the file.
Finally, restart Postfix and Dovecot.
sudo systemctl restart postfix dovecot
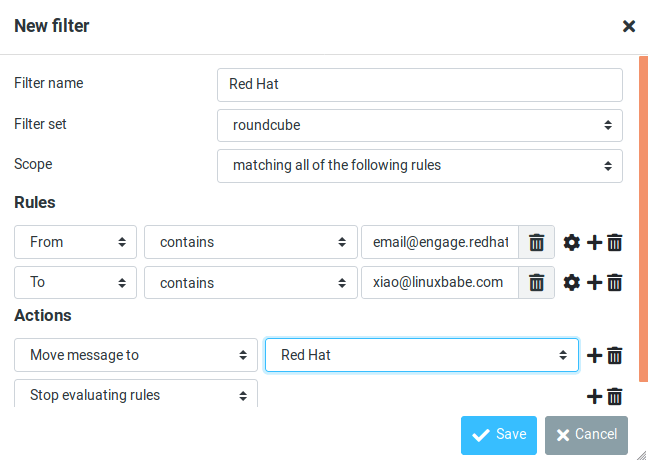
Now you can go to Roundcube webmail, open an email message and click the more button, and select create filters to create message filters. For example, I create a filter that moves every email sent from redhat.com to the Red Hat folder.
If you don’t have the create filter option, it’s probably because you didn’t enable the managesieve plugin. Edit the config.inc.php file.
sudo nano /var/www/roundcube/config/config.inc.php
At the end of this file, you will find a list of active plugins. add the managesieve plugin in the arrary. The plugin order doesn’t matter.
// ----------------------------------
// PLUGINS
// ----------------------------------
// List of active plugins (in plugins/ directory)
$config['plugins'] = ['acl', 'additional_message_headers', 'archive', 'attachment_reminder', 'autologon', 'database_attachments', 'debug_logger', 'emoticons', 'enigma', 'filesystem_attachments', 'help', 'hide_blockquote', 'http_authentication', 'identicon', 'identity_select', 'jqueryui', 'krb_authentication', 'managesieve', 'markasjunk', 'new_user_dialog', 'new_user_identity', 'newmail_notifier', 'password', 'reconnect', 'redundant_attachments', 'show_additional_headers', 'squirrelmail_usercopy', 'subscriptions_option', 'userinfo', 'vcard_attachments', 'virtuser_file', 'virtuser_query', 'zipdownload'];
Save and close the file.
Note that if you move a sieve filter set from an old mail server to your new mail server, you need to go to Settings -> Filters, then click Actions and enable the filter set, or Dovecot LMTP server won’t execute the sieve filter.
Step 9: Removing Sensitive Information from Email Headers
By default, Roundcube will add a User-Agent email header, indicating that you are using Roundcube webmail and the version number. You can tell Postfix to ignore it so recipient can not see it. Run the following command to create a header check file.
sudo nano /etc/postfix/smtp_header_checks
Put the following lines into the file.
/^User-Agent.*Roundcube Webmail/ IGNORE
Save and close the file. Then edit the Postfix main configuration file.
sudo nano /etc/postfix/main.cf
Add the following line at the end of the file.
smtp_header_checks = regexp:/etc/postfix/smtp_header_checks
Save and close the file. Then run the following command to rebuild hash table.
sudo postmap /etc/postfix/smtp_header_checks
Reload Postfix for the change to take effect.
sudo systemctl reload postfix
Now Postfix won’t include User-Agent: Roundcube Webmail in the headers when sending outgoing emails.
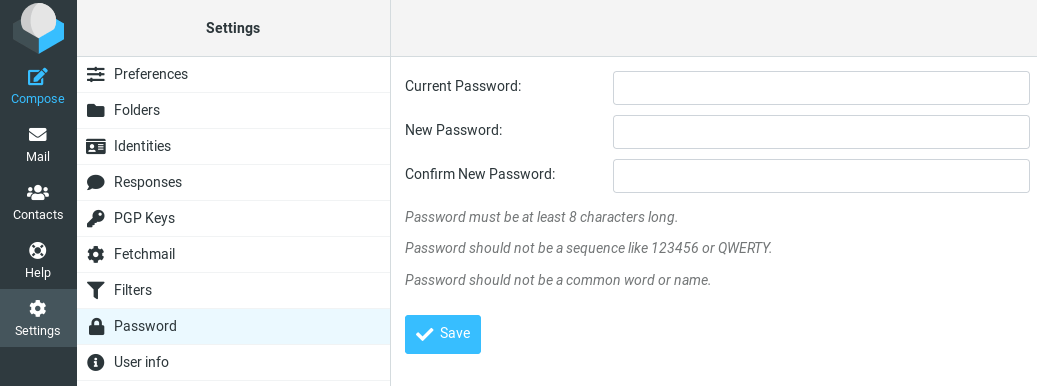
Step 10: Configure the Password Plugin in Roundcube
Roundcube includes a password plugin that allows users to change their passwords from the webmail interface. Edit the config.inc.php file.
sudo nano /var/www/roundcube/config/config.inc.php
Make sure the password plugin in the plugin list at the end of this file. The plugin order doesn’t matter.
$config['plugins'] = array('acl', 'additional_message_headers', 'password', .....);
Save and close the file.
However, we need to configure this plugin before it will work. Run the following command to copy the distributed password plugin config file to a new file.
sudo cp /var/www/roundcube/plugins/password/config.inc.php.dist /var/www/roundcube/plugins/password/config.inc.php
Edit the password plugin configuration file.
sudo nano /var/www/roundcube/plugins/password/config.inc.php
Find the following line:
$config['password_db_dsn'] = '';
This parameter is used to tell the password plugin where the user passwords are stored. By default, the value is empty and it will query the roundcube database, which doesn’t store user passwords. If you followed my PostfixAdmin tutorial, then user passwords are stored in the postfixadmin.mailbox table, so we need to change the value to:
$config['password_db_dsn'] = 'mysql://postfixadmin:postfixadmin_database_password@127.0.0.1/postfixadmin';
The tells the password plugin to connect to the postfixadmin database. If you don’t remember your postfixadmin database password, you can find it in the /etc/dovecot/dovecot-sql.conf.ext file. If your PostfixAdmin password contains a single quote character, then you can use backslash (\') to escape it.
Then find the following line.
$config['password_query'] = 'SELECT update_passwd(%c, %u)';
Change it to the following.
$config['password_query'] = 'UPDATE mailbox SET password=%P,modified=NOW() WHERE username=%u';
I recommend enabling a password strength checker to prevent users from setting weak passwords. Go to the beginning of this file, you can find the following line.
$config['password_strength_driver'] = null;
We can use the zxcvbn password strength driver, so change it to:
$config['password_strength_driver'] = 'zxcvbn';
Add the following line in this file to allow strong passwords only.
$config['password_zxcvbn_min_score'] = 5;
Note: The $config['password_minimum_score'] parameter doesn’t work with the zxcvbn driver, so leave it alone.
You can also set a minimum length for the password. Find the following line.
$config['password_minimum_length'] = 0;
Change it to:
$config['password_minimum_length'] = 8;
Recall that we used the ARGON2I password scheme in the PostfixAdmin tutorial, so we also need to configure the password plugin to use ARGON2I. Find the following lines in the file.
$config['password_algorithm'] = 'clear';
By default, the password will be stored as clear text, change the value to the following to use Dovecot’s builtin password algorithm.
$config['password_algorithm'] = 'dovecot';
Then find the following line, which tells where the Dovecot’s password hash generator is located.
$config['password_dovecotpw'] = '/usr/local/sbin/dovecotpw'; // for dovecot-1.x
Change it to the following.
$config['password_dovecotpw'] = '/usr/bin/doveadm pw -r 5';
Then find the following line, which tells which password scheme will be used.
$config['password_dovecotpw_method'] = 'CRAM-MD5';
Change it to:
$config['password_dovecotpw_method'] = 'ARGON2I';
Find the following line.
$config['password_dovecotpw_with_method'] = false;
Change false to true. This will add a {ARGON2I} prefix to the hashed password, so you will recognize which password scheme is used.
$config['password_dovecotpw_with_method'] = true;
Save and close the file. Since this file contains the database password, we should allow only the www-data user to read and write to this file.
sudo chown www-data:www-data /var/www/roundcube/plugins/password/config.inc.php sudo chmod 600 /var/www/roundcube/plugins/password/config.inc.php
Now users should be able to change their passwords in the Roundcube webmail interface.
How to Set Up Vacation/Out-of-Office Messages
We can use the sieve filter to create vacation/out-of-office messages. Go to Roundcube Settings -> Filters. Then click the create button to create a filter.
- Give this filer a name like “out of office”.
- New filters are not disabled, so you can leave the button alone.
- In the Scope field, select all messages.
- Select Reply with message in the Actions settings, and enter the message that will be automatically sent.
- Enter 1 in how often send messages, so the auto-reply will be sent only once per day for each sender. If you set this value to 7, then the auto-reply will be sent once per 7 days for each sender.
- Leave other text fields empty.
- Click the Save button and you are done.
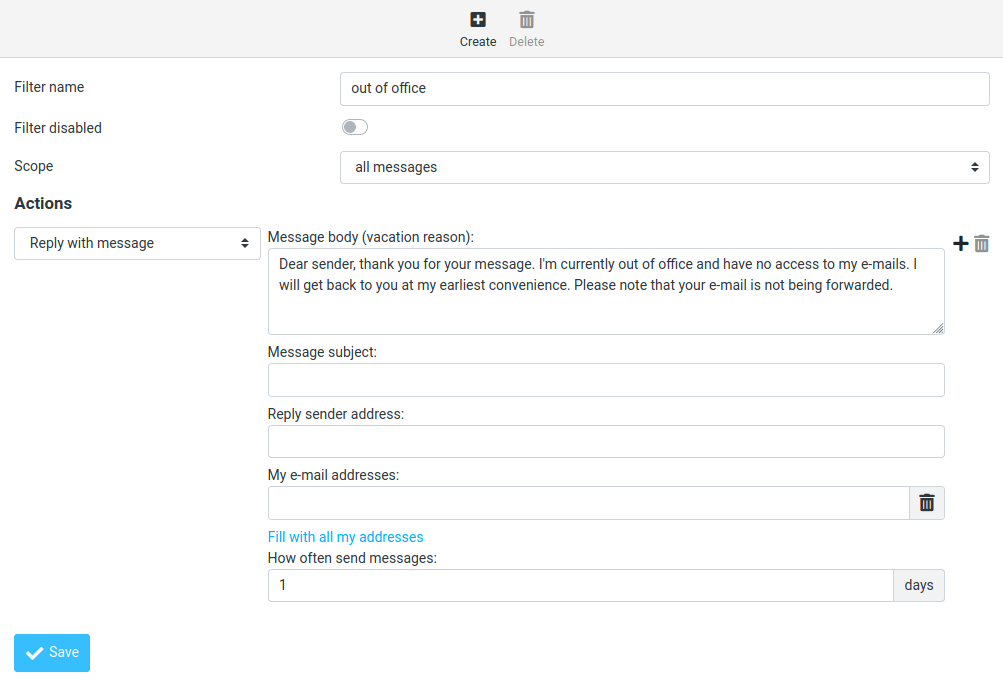
When you are back to office, you can toggle the “Filter disabled” button, and click the Save button to disable this filter.
Increase Upload File Size Limit
If you use PHP-FPM to run PHP scripts, then files such as images, PDF files uploaded to Roundcube can not be larger than 2MB. To increase the upload size limit, edit the PHP configuration file.
sudo nano /etc/php/8.1/fpm/php.ini
Find the following line (line 846).
upload_max_filesize = 2M
Change the value like below. Note that this value should not be larger than the attachment size limit set by Postfix SMTP server.
upload_max_filesize = 50M
Then find the following line (line 694).
post_max_size = 8M
Change the maximum size of POST data that PHP will accept.
post_max_size = 50M
Save and close the file. Alternatively, you can run the following two commands to change the value without manually opening the file.
sudo sed -i 's/upload_max_filesize = 2M/upload_max_filesize = 50M/g' /etc/php/8.1/fpm/php.ini sudo sed -i 's/post_max_size = 8M/post_max_size = 50M/g' /etc/php/8.1/fpm/php.ini
Then restart PHP-FPM.
sudo systemctl restart php8.1-fpm
Nginx also sets a limit of upload file size. The default maximum upload file size limit set by Nginx is 1MB. If you use Nginx, edit the Nginx configuration file.
sudo nano /etc/nginx/conf.d/mail.example.com.conf
Add the following line in the SSL virtual host.
client_max_body_size 50M;
Save and close the file. Then reload Nginx for the changes to take effect.
sudo systemctl reload nginx
There are 3 plugins in Roundcube for attachments/file upload:
- database_attachments
- filesystem_attachments
- redundant_attachments
Roundcube can use only one plugin for attachments/file uploads. I found that the database_attachment plugin can be error_prone and cause you trouble. To disable it, edit the Roundcube config file.
sudo nano /var/www/roundcube/config/config.inc.php
Scroll down to the end of this file. You will see a list of active plugins. Remove 'database_attachments' from the list. Note that you need to activate at least one other attachment plugin, for example, filesystem_attachments.
// ---------------------------------- // PLUGINS // ---------------------------------- // List of active plugins (in plugins/ directory) $config['plugins'] = ['acl', 'additional_message_headers', 'archive', 'attachment_reminder', 'autologon', 'debug_logger', 'emoticons', 'enigma', 'filesystem_attachments', 'help', 'hide_blockquote', 'http_authentication', 'identicon', 'identity_select', 'jqueryui', 'krb_authentication', 'managesieve', 'markasjunk', 'new_user_dialog', 'new_user_identity', 'newmail_notifier', 'password', 'reconnect', 'redundant_attachments', 'show_additional_headers', 'squirrelmail_usercopy', 'subscriptions_option', 'userinfo', 'vcard_attachments', 'virtuser_file', 'virtuser_query', 'zipdownload'];
Save and close the file.
Setting Up Multiple Mail Domains
To host multiple mail domains, please read the following article:
Troubleshooting Tips
If you encounter errors, you can check the web server error logs at /var/log/apache2/roundcube_error.log (if you are using Apache), or /var/log/nginx/roundcube.error (if you are using Nginx.), also the Roundcube error logs in /var/www/roundcube/logs/ directory.
Connection to Storage Server Failed
If you see the Connection to storage server failed error when trying to log into RoundCube, it’s probably because
- Dovecot server isn’t running. You can restart Dovecot with
sudo systemctl restart dovecotand check its status withsystemctl status dovecot. - You are using a self-signed TLS certificate. Roundcube requires a valid TLS certificate issued from a trusted certificate authority such as Let’s Encrypt.
- Your TLS certificate expired. You can renew the Let’s Encrypt TLS certificate with
sudo certbot renew, then restart Postfix and Dovecot (sudo systemctl restart postfix dovecot).
You can also try adding a custom DNS entry in /etc/hosts file as described in step 8 on the Roundcube server, so Roundcube can properly resolve the mail server hostname.
Could Not Load Message From Server
If you see the “Internal error: could not load message from server” error, it’s probabaly because you are trying to open an deleted email (invalid URL). Try going to the mail root domain (mail.example.com) to see if it works.
Sieve Message Filter Doesn’t Work?
If you followed step 8 to set up sieve filter to the letter, but still can’t get it to work, then you can enable debugging in Dovecot to find out what’s wrong.
sudo nano /etc/dovecot/dovecot.conf
Add the following line at the end of this file to enable debugging in Dovecot.
mail_debug=yes
Save and close the file. Then restart Dovecot.
sudo systemctl restart dovecot
Next, send a test email to your domain email address and open the mail log file.
sudo nano /var/log/mail.log
You can find debugging information for Sieve message filter. For example, I found that Dovecot was unable to run my Sieve script.
Jan 10 11:35:24 mail dovecot: lmtp([email protected]) Debug: sieve: Aborted running script `/var/vmail/linuxbabe.com/xiao/.dovecot.svbin'
It turns out that my Sieve filter has too many rules and some of them are conflicting with each other. I delete those conflicting rules and it works again.
Temporary lookup failure (Code: 451)
If you encounter this error when trying to send an email in Roundcube, it’s probably something wrong with your Postfix configuration. For example, some folks might have the following error in the /var/log/mail.log file.
warning: connect to pgsql server localhost: connection to server at "localhost" (127.0.0.1), port 5432 failed: FATAL: password authentication failed for user "postfixadmin"?connection to server at "localhost" (127.0.0.1), port 5432 failed: FATAL: password authentication failed for user "postfixadmin"?
This means your password authentication for the Postfixadmin database is not working.
How to Upgrade Roundcube
It’s very simple. For example, here’s how to upgrade to Roundcube 1.5.3 after it’s released.
Download the Roundcube latest version to your home directory.
cd ~ wget https://github.com/roundcube/roundcubemail/releases/download/1.5.3/roundcubemail-1.5.3-complete.tar.gz
Extract the archive.
tar xvf roundcubemail-1.5.3-complete.tar.gz
Change the owner to www-data.
sudo chown www-data:www-data roundcubemail-1.5.3/ -R
Then run the install script.
sudo roundcubemail-1.5.3/bin/installto.sh /var/www/roundcube/
Once it’s done, log in to Roundcube webmail and click the About button to check what version of Rouncube you are using.
Wrapping Up
I hope this tutorial helped you install Roundcube Webmail on Ubuntu 22.04/20.04. As always, if you found this post useful, subscribe to our free newsletter to get more tips and tricks 🙂



Hi! Thank you very much for the tutorials you provide. I am wondering if it’s possible to allow users to register for free on my own mail server. Just like what Gmail is providing. Thanks awaiting your response.
I didn’t find any open-source web applications that allow you to do that with PostfixAdmin/Roundcube. I think you need to develop this kind of web app by yourself.
Hi! Excellent tutorials!
How would one go about configuring roundcube (on the same server with: postfix, dovecot and postfixadmin) running behind haproxy?
SSL is terminated in haproxy and roundcube is running on the mail server.
Ports 587 and 993 are forwarded respectively as send-proxy and send-proxy-v2 to the mail server.
Postfix is listening to 10587(STARTTLS) and dovecot to 10993(SSL) on the mail server.
Just can’t get a connection from roundcube to smtp and imap. Everything else is running smoothly thanks to your HAProxy tutorial! Any advice would be much appreciated. Cheers!
You can add a custom DNS record in /etc/hosts file on the mail server, pointing the A record to the mail server itself, instead of pointing it to the HAProxy server.
Hello Xiao,
before starting the roundcube installation I want to ask you a question, please:
So, if we have already our mail.example.com.conf virtual host file from the previousDovecot/Postfix tutorial file from previous we do not need to create a roundcube.conf file and to use our mail.example.com instead, right? Then, this file is already populated with content, much of it on behalf of certbot. So, what should we do, adding extra the text you provide us or delete all the old content and add this new one?
Thank You!
Delete the old content and add the lines provided in this article.
Thank You sir!
Hello I followed you steps but apache doesn’t show me anything i can’t see the installer could you give a hand ?
If you encounter errors, you can check the error logs at
/var/log/apache2/roundcube_error.log(if you are using Apache), or/var/log/nginx/roundcube.error(if you are using Nginx.)Hello i’m getting this error when trying to send a mail
SMTP Error (451): Failed to add recipient “mail.mail.com” (4.3.0) “mail.mail.com” Temporary lookup failure
It’s not an email address. Of course it would fail.
It is I’m sending it to my Gmail to test it and I get this error
Is there anything I can check why I’m getting this error tried different emails same error I get
Check your mail log (/var/log/mail.log)
This is the error.
Open the
/etc/postfix/sql/mysql_virtual_alias_domain_maps.cffile. Make sure you have entered the correct password for thepostfixadminuser.I’ve checked and get same error…
Is there anything else I can check ? Why is this happening ?
Perhaps the postfixadmin password contains some special characters that are interpreted as meta-characters.
Only letters and numbers
I will try and install maybe IRedMail but could you tell me how can I run more then just the mail website as I don’t understand how to use the templates there to run the mail and other subdomains
You can edit the /etc/postfix/master.cf file
Find the following line
Add the
-vflag.Save and close the file. Then restart Postfix
Postfix will produce more verbose debugging logs in
/var/log/mail.logquery = SELECT goto FROM alias,alias_domain WHERE alias_domain.alias_domain = '%d' and alias.address = CONCAT('%u', '@', alias_domain.target_domain) AND alias.active = 1 AND alias_domain.active='1I’ve fixed it but now I get this error
host gmail-smtp-in.l.google.com[173.194.76.26] said: 550-5.7.1 [82.44.14.114] The IP you're using to send mail is not authorized to 550-5.7.1 send email directly to our servers. Please use the SMTP relay at your 550-5.7.1 service provider instead. Learn more at 550 5.7.1 https://support.google.com/mail/?p=NotAuthorizedError b18si22548156wrs.358 - gsmtp (in reply to end of DATA command)It seems you are running a mail server with a residential IP address. That’s why Gmail refused to receive emails from your mail server. Consider using a data center IP address (VPS).
Many thanks for this fantastic setup guide.
I’ve followed all the steps above, and my set up is from your tutorials on how to set up a mail server from scratch, got all the way through DMARC and decided to set up Roundcube. Get to the installer, and everything checks out OK. Make the config file and everything checks OK, and then I try to test the IMAP and SMTP, and get NOT OK.
Checked error logs and the apache2 roundcube log says there is an issue with deprecated {}. The error log in /var/www/roundcube/logs says:
Mail log give:
My SSL is a wildcard SSL. Can you help me figure this out? I’ve googled until my fingers hurt, and there seems to be no answer.
BTW: Thunderbird can send and receive just fine, as can my phone email client. Just seems this web thing is problematic.
UPDATE: So I was able to get the login to work. Had to add the ssl config from defaults.inc.php and point to my certificate chain. Still having trouble with SMTP Invalid sender or recipient. Can’t seem to see what the issue is.
UPDATE: So, after fiddling and fiddling, I just decided to log into Roundcube, since I could, and see if I could send an email. I was able. So, I guess it is fixed.
Hello,
Thank’s a lot fo tutorial everything works perfect.
Is someone find a way to fix The maximum upload file size: 2 MB?
I try many things but no result. I remember that in old Roundcube е versions there is such options in installer , but now when I make the configurations there is no such option.
Hello dilyan,
I just added instructions here on how to increase upload file size limit in Roundcube 🙂
Hello Xiao,
Do you have any fail2ban jail to protect roundcube installations?
Thank You so much.
Use a self-hosted VPN to restrict access to Roundcube: https://www.linuxbabe.com/debian/secure-email-server-against-hacking
Hello Xiao,
Thank you very much for your time, the information was very useful for me.
Hi, this is a really good tutorial – however, I think I’ve missed a step. I’m receiving the error :
Sep 12 12:44:06 myhost dovecot: imap(pt): Error: mkdir(/home/pt/Maildir) failed: Permission denied (euid=1000(pt) egid=1000(pt) missing +w perm: /home, dir owned by 0:0 mode=0755)
Sep 12 12:44:06 myhost dovecot: imap(pt): Error: mkdir(/home/pt/Maildir) failed: Permission denied (euid=1000(pt) egid=1000(pt) missing +w perm: /home, dir owned by 0:0 mode=0755)
Sep 12 12:44:06 myhost dovecot: imap(pt): Error: Mailbox INBOX: Failed to autocreate mailbox: Internal error occurred. Refer to server log for more information. [2020-09-12 12:44:06]
I’m hoping you can help with this as to where I’ve gone wrong or how I can resolve this. Also, when you create a new user is there any thing else I would need to do ?
Are you using a canonical domain or virtual mailbox domain in Postfix?
Hi, at the beginning I would like to thank you for the mass of valuable content, thanks to which I am preparing a new mail server.
I would like to ask you how to change the settings so that when creating a new user in linux he will have a default mailbox with a domain without the host name “mail”.
Command: `sudo adduser user` I created a new user and when I log in to the Roundcube panel an account is assigned to the mail.example.com domain instead of example.com. How to change it ?
Translated with www.DeepL.com/Translator (free version)
Simply use the full email address ([email protected]) to log in to Roundcube.
Hey, I have been using a number of your guides for the past few weeks and find them to be some of the best on the internet. Well done!!
I have a single server that is totally under my control. It is serving 4 domains. I used a new Ubuntu 20.04 installation and configured Postfix, Dovecot, and PostfixAdmin to establish a number of virtual users with associated “mailboxes” using your other guides. I can receive and send mail via Thunderbird and a phone (both remote). So far, all is well.
When I attempt to configure the Roundcube software to connect to the email accounts, I cannot seem to find the correct combination of parameters to make the connection. When I use a “tls://mail.my-domain.com” for the IMAP or SMTP connections I get error messages. The IMAP reports “unable to negotiate TLS”. The SMTP error was “STARTTLS failed”.
I tried using localhost as the sever and was able to connect to IMAP, but the SMTP connection indicated an error that authentication was not enabled.
Do you have any suggestions as to what I might be doing wrong? Is my problem potentially associated with the PostfixAdmin and/or the virtual users?
I have made some progress: I am able to authenticate IMAP login using “localhost” and not connecting through an SSL connection since I am on the same server. However, I am getting the following error when attempting SMTP using “localhost”: “Authentication failure: SMTP server does not support authentication (Code: )”.
This is probably correct since I think I recall disabling local SMTP authentication. However, the RoundCube site is on the same server. So do I need to re-enable local authentication? Is that dangerous?
As explained in the article, the IMAP host should be
The SMTP host should be
If you can login from Thunderbird, it doesn’t make sense you can’t log in from Roundcube using the above settings.
Well, you are correct: It doesn’t make sense. Until … I noticed that Thunderbird was accepting all certificates. I went and did a certificate check with a different E-mail client and found that the certificate did not list mail.example.com as served by that certificate.
I set up a number of sites on the same server and am using PostfixAdmin (some of your other tutorials) to serve virtual accounts. And RoundCube was looking for a certificate with the matching mail server name. Your other tutorial assumes that I already have RoundCube up and running. I did not. And RoundCube installer did not give enough information to tell me why it was failing.
It was my fault for not recognizing that the certificate had not been set up yet for multiple virtual servers. You might consider pointing to the other tutorial in this one. (Or perhaps indicating that a person would want to create a multi-site certificate if they are hosting more than one.) In any case I figured it out. Eventually.
Thanks for your help. And thanks for the wonderful tutorials.
Yes, you need a multi-site certificate, and thanks for the tip.
Hey, I’m getting an error while trying to import the initial tables to the roundcube database. I think it’s because I have a password set for my root sql user. Would there be any way to get around this?
Error:
If you use password authentication, then use the following command to import initial tables. It will prompt you to enter MariaDB root password.
Through the help of your tutorials I have been able to setup two virtual hosts, mail.teseling.me and mail.teseling.com and am able to send and receive email through Thunderbird.
I would like to also webmail for these two email hosts and followed your tutorial. However; when I type in https://mail.teseling.me/installer the Firefox returns a “Not Found – The requested URL was not found on this server.” It also indicates under the line “Apache/2.4.41 (Ubuntu) Server at mail.teseling.me Port 443”.
When I type just https://mail.teseling.me it returns “Index of /
[ICO] Name Last modified Size Description
Apache/2.4.41 (Ubuntu) Server at mail.teseling.me Port 443”
/var/www/roundcube/logs/errors.log indicates an access issue:
your feedback would be appreciated.
If you host multiple domains on your mail server, you only need to follow this once. You don’t need to apply this tutorial on the second domain.
As for the SQL database error, make sure you have entered the correct password for this
roundcuberuserin the setup wizard. You can try to login as theroundcubeuserwith the following command, which will ask you the password.If you messed up your roundcube files, you can remove the web directory.
Then download the Roundcube tar.gz file again and reinstall RoundCube.
Thanks Xiao,
I was able to log into mysql with the command you supplied and the password for roundcube.
In /var/www/roundcube/config/config.inc.php I can see the following line:
and the password is correct.
Is there any other places I should look where I may need to correct it?
When I logged into mysql with the command you supplied and the entered the command mysql> show databases; it displays the following:
Should I be concerned that there isn’t a database roundcubemail listed?
It seems your RoundCube files are corrupted. I recommend reinstalling Roundcube.
Remove the web directory.
Remove the roundcube database.
Then download the Roundcube tar.gz file again and reinstall RoundCube.
Thanks Xiao,
I now realize the database shouldn’t have been roundcubemail (as in my second post but should have been roundcube.
I reinstalled roundcube as you suggested and it seems as if it installed correctly. However, when I try to send the test email I get the message:
“Trying to send email…
SMTP send: NOT OK(Authentication failure: STARTTLS failed (Code: ))”
and when I click on “Check login” to test IMAP config I get the following message:
“Connecting to ssl://mail.teseling.com…
IMAP connect: NOT OK(Login failed for [email protected] against mail.teseling.com from 127.0.0.1. Could not connect to ssl://mail.teseling.com:993: Unknown reason)”
I can’t see any error messages in the roundcube error logs.
Check the mail log (/var/log/mail.log) to debug this error.
Hi Xiao
thanks for taking the time for an excellent series of articles.
I have a ubuntu server with apache, mariadb, and wordpress. all working beautifully and no issues.
Hi 🙂 Thank you for all the guides, I’m finishing off setting up Postfix and Dovecot for someone with this Roundcube guide, I don’t suppose you’ve set up the Roundcube ACL plugin with your Postfix/Dovecot installation before?
I’ve found a couple of partial guides to simple ACL with Dovecot, but I can’t seem to enable ACL properly, testing it in telnet gives me “BAD Error in IMAP command SETACL: ACLs disabled” as soon as I try any SETACL command. I assume I’m just enabling it in the wrong place, the guides I’m following have a single dovecot.conf file rather than the conf.d directory but I’ve tried pretty much every combination that makes sense to me, plus a few that didn’t just in case…
Everything else is working beautifully, best guide to setting up a proper grown up mail server that I’ve seen since qmailrocks was a thing! 🙂
Thanks, the
Hello and Thank you for your tutorials.
I’m new to linux and creating a email server from scratch.
I’ve completed steps 1 to 3 (postfix, dovecot, postfixadmin) with success.
I’m able to send emails internally and outside however I’m really stuck with setting up roundcube
In the installer all checks were OK accept when testing the config.
Test SMPT config resulted in SMTP send:
Test IMAP config resulted in
looking in the /var/www/roundcube/logs I get an error when trying to log in
I also received a message “connection to storage server failed” when attempting to login on the webpage.
I made sure that dovecot status was active.
Would you have any suggestions where I can look to resolve this issue.
Your help would be much appreciated.
Thanks,
Are you using a self-signed TLS certificate, and is your TLS certificate expired?
Hello Xiao, and thank you for your reply.
No it is not a self singed certificate. The certificate was created from letsencrypt using your tutorial.
I just checked and it is in the directory /etc/letsencrypt/live/mail.mydomain.com
Test SMTP and IMAP again, then check the mail log (/var/log/mail.log).
I ran both tests, SMTP and IMAP, where both of them failed. I checked mail.log and nothing was written.
That could mean there’s firewall preventing you from connecting to the SMTP submission port and IMAP port.
You can use
telnetto check if you can access port 587 and 993.and
If port 587 and 993 can be accessed, you should see something like
Type
quitto close the connection.If port 587 and 993 can’t be accessed, you can see an output like
By the way, I see your client’s IP address is
10.10.0.80. Is RoundCube webmail installed on the mail server or on another box?I ran the telnet test as you requested on the mail server (virtualbox) with static IP 10.10.0.150 where both ports timed out with no connection.
when I run the telnet test on a virtualbox Ubuntu desktop PC (10.10.0.143) I’m able to connect on ports 587 and 993.
the 10.10.0.XX is on my LAN network behind a pfSense firewall. In order for me to send email internally between accounts and open postfixadmin on a web browser I need to add host overrides on dns resolver
So in a nut shell I’m able to send emails internally between email accounts e.g. test1, test2 and test3 and send email outbound.
When I send email from the outside (gmail) to the mail server I have a rule on the WAN interface which allows mail to reach the mail server using a public IP to private IP (1:1 NAT) which works perfectly.
10.10.0.80 is my windows pc which is hosting the virtualbox.
Just cannot figure out why I can’t get roundcube to connect
Karl
If you install Roundcube on the mail server, then there shouldn’t be a firewall problem.
On the mail server, you can edit
/etc/hostsfile and add the following entry, so that Roundcube won’t have to query the public DNS, which will speed up web page loading a little bit.Thank You for your Help Xiao,
Adding 127.0.0.1 mail.mydomain.com to the /etc/hosts file worked.
Hi, i followed the tutorials and everything else seems to work, but virtual mailboxes wont work, so the mail cannot be delivered to me, but i can send mail just fine.
This is the error im getting in syslog.log:
Even if i manually create the corrent path i get the same error.
This is set, so it shouldnt it work?
/etc/dovecot/conf.d/10-mail.conf
Oh i figured it out…
i thought i didnt need
after we added
I added mail_location back and everything works 🙂
This is by far the best set of guides I have come across in setting up LEMP, PostfixAdmin, MariaDB, and Roundcube on Linux installs in the number of years I have been running a private email server.
One error I am coming across is when trying to send emails from the Roundcube interface. Emails are sent just fine if I use a mobile interface like my laptop or phone, but I cannot get the webmail interface from the server to send. I spun up a VPS instance at ScalaHosting to test drive this setup before I migrate my database data from the old server.
First issue to pop up was in the Roundcube test config screen after saving the config:
Like I said before, connecting from another source like a phone/computer works just fine, but something about the localhost is causing heartburn.
The mail.log file does not give a whole log of information to go on:
Content inside the master.cf file is straight from the guide:
Any insight would be very helpful. Thanks.
Woot just solved the issue!
The Roundcube installer is setup with a default port of 587 for the outgoing SMTP server. Changing from 587 to 465 fixed the issue.
Glad to know you solved the issue. Jus want to let you know that you must use
tls://as the prefix for port 587. Thessl://prefix should be used for port 465.Ahh that explains it. Thanks for replying back!
I follow you tutorial from scratch,
I was able to setup email server with postfix admin and virtual boxes.
It is working fine.
Then i try to follow this tutorial to setup roundcube.
I run the installer, but i setup round cube on mailweb.my-domain.com instead your default mail.my-domain.com.
On Test Config screen, all tests are Ok.
When i try to test SMTP config and IMAP Config, got the error bellow:
Trying to send email…
SMTP send: NOT OK(Authentication failure: Invalid response code received from server (Code: 535))
I forgot to tell you.
Try with tls and por 587 and ssl on port 465.
Also, i am using the mail.my-domain.com as mx reccords.
I belive that is because round cube is not reaching the virtual accounts database to authenticate.
Great tutorial, by the way.
It was the only i found that works.
Thanks.
Use the following SMTP settings in Roundcube:
IMAP settings
Make sure your TLS certificate is valid (not self-signed and not expired).
I did that.
Certificate is letsencrypt, not self-signed and is not expired.
Forgot other thing. I still need help.
;p
Just posting here a feedback.
Step 10: Configure the Password Plugin in Roundcube – This step is essential for roundcube to work.
All works fine now.
Thanks.
Sending an e-mail directly to my gmail doesn’t work. No errors in /var/log/mail.err. Replying to the e-mail from the Sent folder goes through. Replying back from gmail to my mail server fails and returns:
The mail system : host cloudnode.pro[private/dovecot-lmtp] said: 550 5.1.1 User doesn't exist: [email protected] (in reply to RCPT TO command)It seems you didn’t follow my Postfix and Dovecot tutorial. If you follow mail server tutorials from other websites, I don’t guarantee this Roundcube tutorial will work for you.
Thanks a lot for your reply. I followed both precisely as instructed. Could you recommend some software for Ubuntu 20.04 that is easy to install and to manage email accounts?
Otherwise after following your tutorials on postfix and dovecot, what steps would you recommend to safely start over? Maybe I accidentally missed something.
I see you use
cloudnode.proas the mail server hostname. As I said in the Postfix tutorial, you should usemail.cloudnode.proas the hostname.If you don’t want to set up everything from scratch, you can use iRedMail, which can automatically configure lots of the settings for you. iRedMail should be installed on a fresh clean server.
The server I am using is also utilised to host my website. The mail server is configured on the subdomain, as instructed.
Can I completely wipe postfix and davecot using `apt purge postfix davecot roundcube && apt autoremove`, `DROP DATABASE roundcube;`?
Will check out iRedMail. Does it really need to be a new/clean server?
I have a LAMP setup, my objectives are to be able to send mail via `php` and easily create and suspend e-mail accounts for my team to use.
Technically you can install iRedMail on an existing LAMP server, but it’s error-prone (may break your existing applications) and requires extra complicated steps. And I won’t help users with this without getting paid.
Fresh clean server means that there should not be any new software installed by the user. No Postfix, Dovecot, LAMP, whatsoever.
If you create an email address in PostfixAdmin and you see the “no such user” or “user doens’t exist” error in the mail log, it must be there’s something wrong with your Dovecot configuration, especially the
mail_locationandmail_homeparameter. I would recommend reading part 2 and part 3 again very carefully.I must have entirely missed that part with postfix admin as I do not have it set up. I’ll try to delete everything and make sure to follow the tutorial more closely this time.
Hi Xiao.
Sorry, I need to ask another question from you. I finish these roundcube installation, follow all the steps, but I cannot change the password from the web interface, it always gives an error:
> Encryption function missing.
I have all the configurations like you said, only difference is that I kept the default PostfixAdmin codification of MD5-CRYPT (I forgot to change before installing and now I don’t know if I can change it).
Do you have any idea of what could I be doing wrong?
Thanks
Hello Xiao.
I solved the problem with following this guide:
https://github.com/postfixadmin/postfixadmin/issues/381
I found that the problem was the doveadm command was giving an error of permission denied accessing the let’s encrypt certificates. I tried changing some permissions but did not manage to make it work, so I found that issue and the problem is fixed.
I leave it here because it could be helpful to other people.
Again, Thank you very much for your guides.
You Rock! Excellent tutorial.
There is however one issue I face when sending a mail to my own gmail account:
did I miss something?
You need to set PTR record for your IPv6 address.
this is very excellent tutorial, finally after all this time i have manage and undurstand how to build my own custom mail server, thank you very much xiao.
HI,
I have those problems:
When on test mail for roundcube installation:
Trying to send email…
SMTP send: NOT OK(Authentication failure: STARTTLS failed (Code: ))
and testing connection roundcube
Connecting to ssl://w3bmail.marmogres.tech…
IMAP connect: NOT OK(Login failed for [email protected] against w3bmail.marmogres.tech from [my IPv6] Could not connect to ssl://w3bmail.marmogres.tech:993: Unknown reason)
The let’s encrypt certs are configure in the /etc/nginx/site-enable/w3bmail.marmogres.tech
Ports are open in UFW
i have the A and AAAA DNS OK for w3bmail
have you an idea about the problem?
Don’t use the hostname of the webmail, which is an HTTP server. Use the hostname of the SMTP server & IMAP server.
Your webmail should connect to the SMTP and IMAP server, not connect to itself.
Hi Xiao Guoan,
I am following your excellent guide, but with a payed certificate in stead of the Let’s encrypt one.
I encountered a problem getting the Roundcube installer to establish the iMap connection and subsequently logging into Roundcube.
It turned out that Roundcube / PHP could not verify the certificate because the intermediate certificates were not where they were expected.
To solve this, I had to add the following to config.inc.php ( copied from defaults.inc.php )
// IMAP socket context options // See http://php.net/manual/en/context.ssl.php // The example below enables server certificate validation $config['imap_conn_options'] = array( 'ssl' => array( 'verify_peer' => true, 'verify_depth' => 3, 'cafile' => '/path_to_my_intermediate_certificate_file', ), );I hope this helps somebody 😉
Thanks and best regards,
Ernst