How to Install Passbolt Password Manager on Ubuntu 22.04 Server
Passbolt is an open-source self-hosted password manager, which allows you to securely store and share login credentials of website, router password, Wi-Fi password, etc. This tutorial will be showing you how to install Passbolt Community Edition (CE) on Ubuntu 22.04 with Apache or Nginx web server.
Passbolt Features
- Free & open source
- Passwords are encrypted with OpenPGP, a proven cryptographic standard.
- Browser extensions are available for Firefox, Google Chrome, Microsoft Edge and Brave Browser.
- Mobile app is available for iOS and Android.
- Easily share login credentials with your team without compromising security.
- Clean, user-friendly interface.
- Import and export passwords. You can export your passwords to
.kdbxor.csvfile format for use with KeepassX, LastPass or 1password. - You can manually add login credentials.
Prerequisites of installing Passbolt on Ubuntu 22.04 Server
Passbolt is written in PHP and relies on MySQL/MariaDB database server. So you need to set up a LAMP stack or LEMP stack before installing Passbolt.
- If you prefer Apache web server, then set up LAMP stack: How to Install LAMP Stack on Ubuntu 22.04
- If you prefer Nginx web server, then set up LEMP stack: How to Install LEMP Stack on Ubuntu 22.04
It’s very important that your server can send emails, so you can recover your Passbolt account if you forget the password. Follow the tutorial linked below to set up SMTP relay on Ubuntu.
You also need a domain name, so you will be able to securely access Passbolt from anywhere with a web browser. I registered my domain name from NameCheap because the price is low and they give whois privacy protection free for life.
After the above requirements are met, follow the instructions below to install Passbolt.
Step 1: Download Passbolt onto Your Ubuntu 22.04 Server
If you go to the official website to download Passbolt, you are required to enter your name and email address. If that’s not what you like, then download the latest stable version from Github by executing the following commands on your server.
sudo apt install git sudo mkdir -p /var/www/ sudo chown www-data:www-data /var/www/ -R cd /var/www/ sudo -u www-data git clone https://github.com/passbolt/passbolt_api.git
The files will be saved in passbolt_api directory. We rename it to passbolt.
sudo mv passbolt_api passbolt
Then make the web server user (www-data) as the owner of this directory.
sudo chown -R www-data:www-data /var/www/passbolt
Run the following command to install PHP modules required or recommended by Passbolt
sudo apt install php-imagick php-gnupg php8.1-gnupg php8.1-common php8.1-mysql php8.1-fpm php8.1-ldap php8.1-gd php8.1-imap php8.1-curl php8.1-zip php8.1-xml php8.1-mbstring php8.1-bz2 php8.1-intl php8.1-gmp php8.1-xsl
Then restart Apache. (If you use Nginx, you don’t need to restart Nginx.)
sudo systemctl restart apache2
Change directory.
cd /var/www/passbolt/
Install Composer – the PHP dependency manager.
sudo apt install composer
Create cache directory for Composer.
sudo mkdir /var/www/.composer
Make www-data as the owner.
sudo chown -R www-data:www-data /var/www/.composer
Use Composer to install dependencies.
sudo -u www-data composer install --no-dev
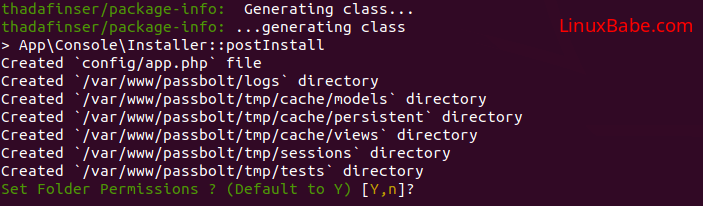
If it asks you to set folder permissions, choose Y.
Step 2: Create a MariaDB Database and User for Passbolt
Log into MariaDB console.
sudo mysql -u root
Next, create a new database for Passbolt using the following command. This tutorial names it passbolt, you can use whatever name you like for the database. We also specify utf8mb4 as the character set to support non-Latin characters and emojis.
CREATE DATABASE passbolt DEFAULT CHARACTER SET utf8mb4 COLLATE utf8mb4_unicode_ci;
The following command will create a database user and password, and at the same time grant all permission of the new database to the new user so later on Passbolt can write to the database. Replace red texts with your preferred database name, username, and password.
GRANT ALL ON passbolt.* TO 'passboltuser'@'localhost' IDENTIFIED BY 'password';
Flush privileges table and exit MariaDB console.
FLUSH PRIVILEGES; EXIT;
Step 3: Generate OpenPGP Key
If you are using a VPS (Virtual Private Server), it’s recommended to install the haveged package to generate enough entropy.
sudo apt install haveged
The haveged.service will automatically start after installation. You can check its status with:
sudo systemctl status haveged
Then run the following command to generate a new key pair.
sudo -u www-data gpg --quick-gen-key --pinentry-mode=loopback 'first_name last_name <[email protected]>' default default never
- Enter your first name and last name.
- Replace
[email protected]with your real email address. - Don’t leave out the angle bracket.
Like this:
sudo -u www-data gpg --quick-gen-key --pinentry-mode=loopback 'Xiao Guoan <[email protected]>' default default never
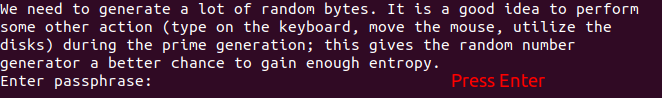
If you are asked to set a passphrase, skip it by pressing Enter, because the php-gnupg module doesn’t support using passphrase at the moment.
Copy the private key to the passbolt configuration location.
sudo -u www-data gpg --armor --export-secret-keys [email protected] | sudo tee /var/www/passbolt/config/gpg/serverkey_private.asc > /dev/null
And copy the public key as well.
sudo -u www-data gpg --armor --export [email protected] | sudo tee /var/www/passbolt/config/gpg/serverkey.asc > /dev/null
Initialize the www-data user’s keyring.
sudo su -s /bin/bash -c "gpg --list-keys" www-data
Step 4: Configure Passbolt
Make sure you are in /var/www/passbolt/ directory.
cd /var/www/passbolt/
Copy the sample configuration file to a production configuration file.
sudo cp config/passbolt.default.php config/passbolt.php
Edit the configuration file with a command-line text editor, such as Nano.
sudo nano config/passbolt.php
First, find the following line.
'fullBaseUrl' => 'https://www.passbolt.test',
Replace the URL with your own URL, like https://passbolt.yourdomain.com. Don’t forget to create DNS A record for this subdomain in your DNS zone editor.
In the database configuration section, enter the database name, database username and password you created in step 2.
// Database configuration.
'Datasources' => [
'default' => [
'host' => 'localhost',
//'port' => 'non_standard_port_number',
'username' => 'user',
'password' => 'secret',
'database' => 'passbolt',
],
],
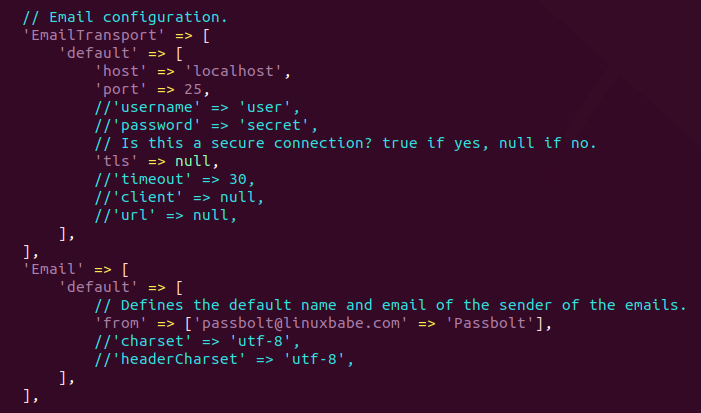
In the email configuration section,
- Specify the SMTP hostname, port number, login credentials, so your passbolt can send emails. Usually, you need to use port 587 to sumbit emails to remote SMTP server. Make sure you set
tlstotrue, so the SMTP transaction will be encrypted. If you use the free Sendinblue SMTP relay service, then enter your Sendinblue credentials here. - Also set the
From:email address and From name.
// Email configuration.
'EmailTransport' => [
'default' => [
'host' => 'smtp-relay.sendinblue.com',
'port' => 587,
'username' => 'smtp_username',
'password' => 'smtp_password',
// Is this a secure connection? true if yes, null if no.
'tls' => true,
//'timeout' => 30,
//'client' => null,
//'url' => null,
],
],
'Email' => [
'default' => [
// Defines the default name and email of the sender of the emails.
'from' => ['[email protected]' => 'Passbolt'],
//'charset' => 'utf-8',
//'headerCharset' => 'utf-8',
],
],
Follow the tutorial linked below to set up SMTP relay on Ubuntu.
Hint #1: If passbolt is installed on the same box as your mail server, then you don’t need to specify the username and password in the EmailTransport. Simply use // to comment out these two lines. The following screenshot shows a sample configuration for this scenario.
Hint #2: Don’t forget to add Passbolt Cron job in step 9, or Passbolt won’t send emails.
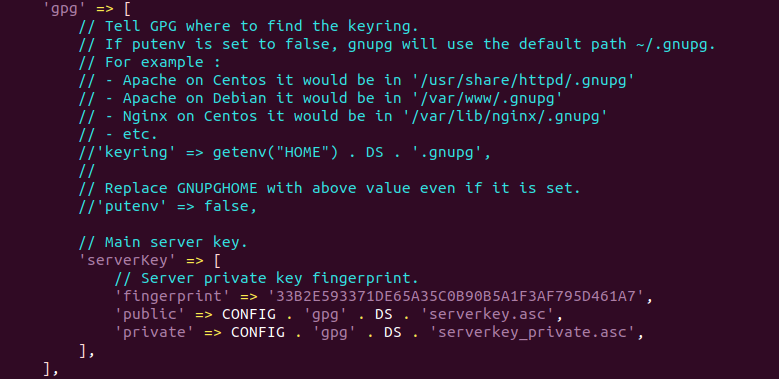
In the gpg section, enter the GPG key fingerprint like below. You need to delete all whitespaces in the fingerprint.
'fingerprint' => '2FC8945833C51946E937F9FED47B0811573EE67E',
You can get your key fingerprint with the following command. Replace [email protected] with your email address when generating the PGP key pair.
sudo su -s /bin/bash -c "gpg --list-keys" www-data

After entering the fingerprint, uncomment the following two lines.
'public' => CONFIG . 'gpg' . DS . 'serverkey.asc', 'private' => CONFIG . 'gpg' . DS . 'serverkey_private.asc',
Save and close the file.
Step 5: Run the Install Script
Run the install script as the www-data user.
sudo su -s /bin/bash -c "/var/www/passbolt/bin/cake passbolt install --force" www-data
During the installation, you will be asked to create an admin account.
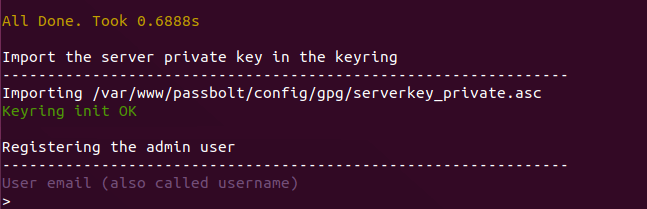
Once you create an account, you will be provided an URL to finish the installation in web browser. Before doing that, we need to configure the web server using Apache or Nginx.
Step 6: Create Apache Virtual Host or Nginx Config File for Passbolt
Apache
If you use Apache web server, create a virtual host for Passbolt.
sudo nano /etc/apache2/sites-available/passbolt.conf
Put the following text into the file. Replace passbolt.example.com with your real domain name and don’t forget to set DNS A record for it. Also note that the web root for Passbolt is /var/www/passbolt/webroot/, not /var/www/passbolt/.
<VirtualHost *:80>
ServerName passbolt.exmaple.com
DocumentRoot /var/www/passbolt/webroot/
ErrorLog ${APACHE_LOG_DIR}/error.log
CustomLog ${APACHE_LOG_DIR}/access.log combined
<Directory />
Options FollowSymLinks
AllowOverride All
</Directory>
<Directory /var/www/passbolt/>
Options FollowSymLinks MultiViews
AllowOverride All
Order allow,deny
allow from all
</Directory>
</VirtualHost>
Save and close the file. Then enable this virtual host with:
sudo a2ensite passbolt.conf
Reload Apache for the changes to take effect.
sudo systemctl reload apache2
Nginx
If you use Nginx web server, create a virtual host for Passbolt.
sudo nano /etc/nginx/conf.d/passbolt.conf
Put the following text into the file. Replace passbolt.example.com with your real domain name and don’t forget to set DNS A record for it. Also note that the web root for Passbolt is /var/www/passbolt/webroot/, not /var/www/passbolt/.
server {
listen 80;
listen [::]:80;
server_name passbolt.example.com;
root /var/www/passbolt/webroot/;
error_log /var/log/nginx/passbolt.error;
access_log /var/log/nginx/passbolt.access;
index index.php index.html index.htm index.nginx-debian.html;
location / {
try_files $uri $uri/ /index.php?$query_string;
}
location ~ \.php$ {
# try_files $uri =404;
fastcgi_split_path_info ^(.+\.php)(/.+)$;
# NOTE: You should have "cgi.fix_pathinfo = 0;" in php.ini
fastcgi_pass unix:/var/run/php/php8.1-fpm.sock;
fastcgi_index index.php;
fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name;
include fastcgi_params;
fastcgi_buffer_size 128k;
fastcgi_buffers 256 16k;
fastcgi_busy_buffers_size 256k;
fastcgi_temp_file_write_size 256k;
}
# Don't log favicon
location = /favicon.ico {
log_not_found off;
access_log off;
}
# Don't log robots
location = /robots.txt {
access_log off;
log_not_found off;
}
# Deny all attempts to access hidden files/folders such as .htaccess, .htpasswd, .DS_Store (Mac), etc...
location ~ /\. {
deny all;
access_log off;
log_not_found off;
}
# Deny all grunt, composer files
location ~* (Gruntfile|package|composer)\.(js|json)$ {
deny all;
access_log off;
log_not_found off;
}
# A long browser cache lifetime can speed up repeat visits to your page
location ~* \.(jpg|jpeg|gif|png|webp|svg|woff|woff2|ttf|css|js|ico|xml)$ {
access_log off;
log_not_found off;
expires 360d;
}
}
Save and close the file. Then test Nginx configuration.
sudo nginx -t
If the test is successful, reload Nginx for the changes to take effect.
sudo systemctl reload nginx
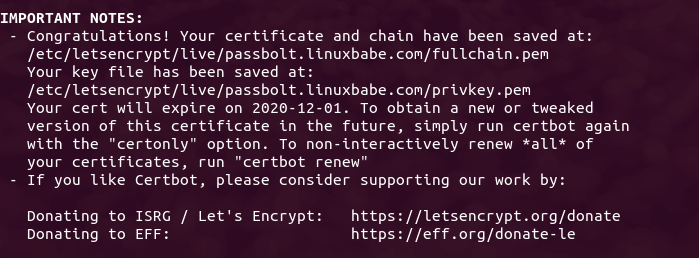
Step 7: Enabling HTTPS
To encrypt the HTTP traffic, we can enable HTTPS by installing a free TLS certificate issued from Let’s Encrypt. Run the following command to install Let’s Encrypt client (certbot) on Ubuntu 22.04 server.
sudo apt install certbot
If you use Nginx, then you also need to install the Certbot Nginx plugin.
sudo apt install python3-certbot-nginx
Next, run the following command to obtain and install TLS certificate.
sudo certbot --nginx --agree-tos --redirect --hsts --staple-ocsp --email [email protected] -d passbolt.example.com
If you use Apache, install the Certbot Apache plugin.
sudo apt install python3-certbot-apache
And run this command to obtain and install TLS certificate.
sudo certbot --apache --agree-tos --redirect --hsts --staple-ocsp --email [email protected] -d passbolt.example.com
Where
--nginx: Use the nginx plugin.--apache: Use the Apache plugin.--agree-tos: Agree to terms of service.--redirect: Force HTTPS by 301 redirect.--hsts: Add the Strict-Transport-Security header to every HTTP response. Forcing browser to always use TLS for the domain. Defends against SSL/TLS Stripping.--staple-ocsp: Enables OCSP Stapling. A valid OCSP response is stapled to the certificate that the server offers during TLS.
The certificate should now be obtained and automatically installed.
Step 8: Finish Passbolt Installation in Web Browser
First, you need to install the Passbolt extension on your Firefox or Google Chrome browser.
Now copy the URL you got after running the install script and paste it in your browser’s address bar. You will see the web-based set up wizard.
The first step is to create a passphrase.

Then download the recovery kit.
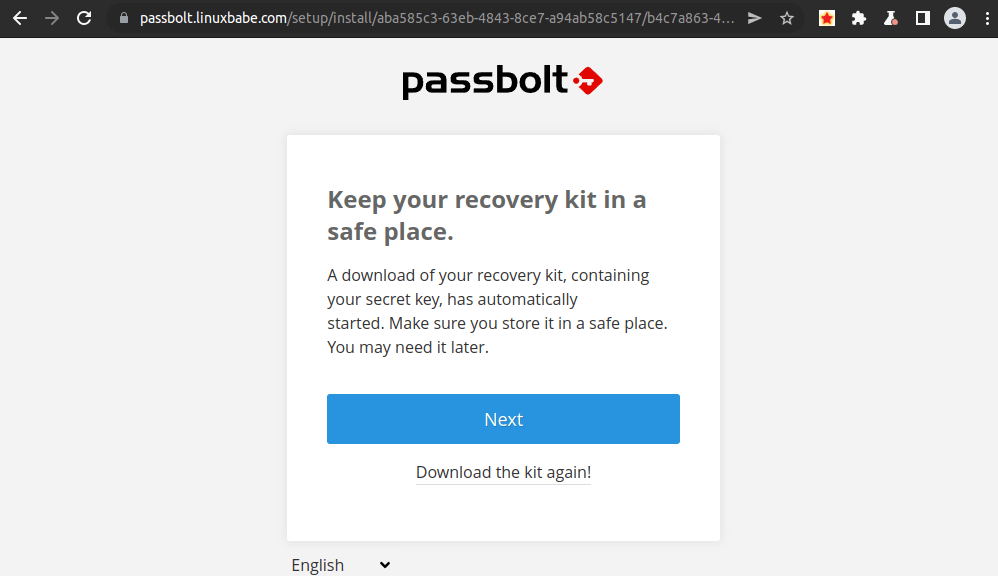
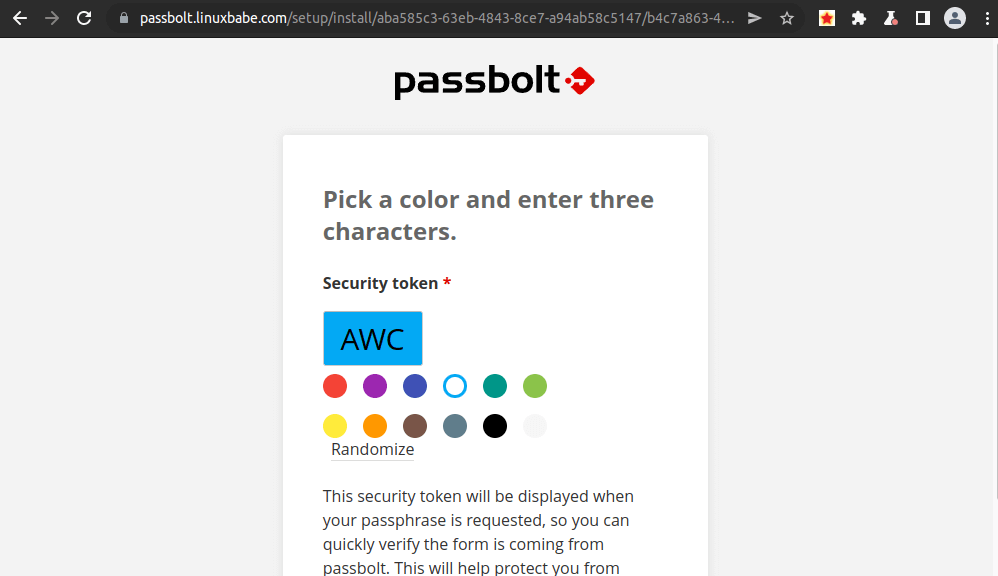
Next, create a custom security token.
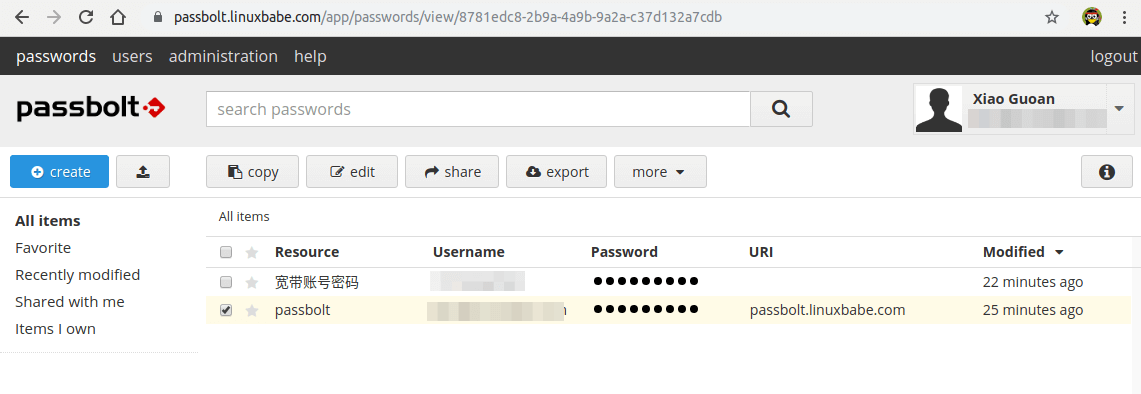
Now Passbolt is installed successfully, you can create password, import password from csv or kdbx file.
Step 9: Set Up Cron Job to Automatically Send Emails
To send system emails, run the following command.
sudo -u www-data /var/www/passbolt/bin/cake EmailQueue.sender
You can add the command in www-data user’s Crontab file to automatically process emails.
sudo crontab -u www-data -e
Add the following line in the file to process emails every minute.
* * * * * /var/www/passbolt/bin/cake EmailQueue.sender
Save and close the file.
(Optional) Setting Up ModSecurity
You may also want to set up the ModSecurity web application firewall to protect your PHP web applications from hacking. If you use Apache web server on Debian/Ubuntu, then read the following tutorial.
If you use Nginx web server on Debian/Ubuntu, then read the following tutorial:
TroubleShooting
If you are trying to create a password, but are stuck at the “take a deep breath and enjoy being in the present moment…” screen, it’s likely because there’s something wroing in your Apache or Nginx configuration file. If you copy the Apache/Nginx configuration from the article, you should have no problem when creating password.
If you enabled ModSecurity web application firewall, and you see the Could not verify the server key error.
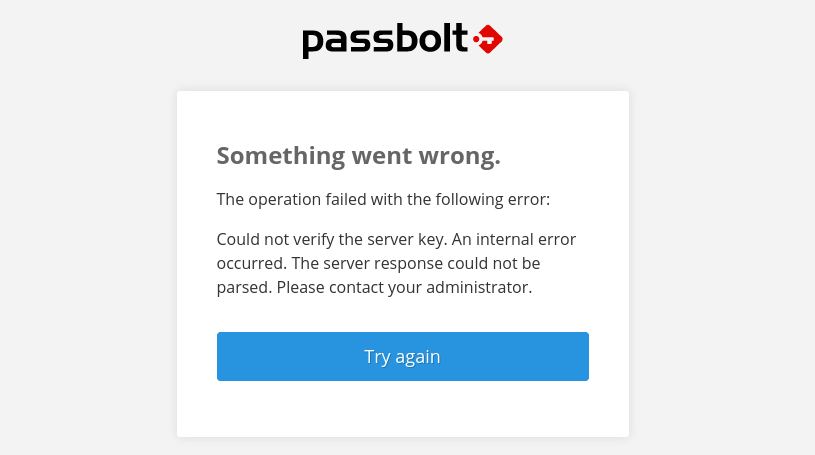
then you need to add the following custom rule exclusion in ModSecurity.
SecRule REQUEST_URI "@streq /auth/verify.json?api-version=v2" "id:1060,phase:2,ctl:ruleRemoveById=942100"
And restart your web server.
sudo systemctl restart apache2
or
sudo systemctl restart nginx
How to Upgrade Passbolt
Check the current version.
sudo su -s /bin/bash -c "/var/www/passbolt/bin/cake passbolt version" www-data
Change to the passbolt directory.
cd /var/www/passbolt
Get new tags from the Github repository.
sudo -u www-data git fetch --tags
Back up the Passbolt configuration file to your home directory.
sudo cp config/passbolt.php ~
Commit local changes.
sudo -u www-data git stash
Switch to the latest version.
sudo -u www-data git checkout v3.9.0
Use Composer to install dependencies.
sudo -u www-data composer install --no-dev
If it asks you to set folder permissions, choose Y.
Migrate database.
sudo su -s /bin/bash -c "/var/www/passbolt/bin/cake passbolt migrate" www-data
Check the current version.
sudo su -s /bin/bash -c "/var/www/passbolt/bin/cake passbolt version" www-data
Perform a health check.
sudo su -s /bin/bash -c "/var/www/passbolt/bin/cake passbolt healthcheck --verbose" www-data
If there’s an error in health check, Passbolt will give you a hint [help] on how to solve it. For example, if there’s no valid JWT key pair, then it will instruct you to run the following command to fix it.
sudo su -s /bin/bash -c "/var/www/passbolt/bin/cake passbolt create_jwt_keys" www-data
If your GPG private/public key pair expired, you need to extend the expiration date.
Wrapping Up
I hope this tutorial helped you install Passbolt on Ubuntu 22.04. As always, if you found this post useful, then subscribe to our free newsletter to get more tips and tricks. Take care 🙂



Hi friend, when I try to use:
sudo -u www-data /var/www/passbolt/bin/cake EmailQueue.sender
Get notification error:
PHP Warning: Use of undefined constant yes – assumed ‘yes’ (this will throw an Error in a future version of PHP) in /var/www/passbolt/config/passbolt.php on line 73
Why?
In the /var/www/passbolt/config/passbolt.php file, Change
to
Ok, work fine. Thank you
Thanks! The only extra step i had to do was to enable php url rewrite.
thanks!
Ni hao!
I’ve installed Passbolt according to your instructions, but when I try to complete the installation in either Firefox or Chrome I get a webpage asking me to either install the extension (which is already installed) or refresh to detect the extension. Refreshing does no good at all; I just keep getting the same webpage. Any ideas?
Update: It’s working now; apparently there was a mismatch between my Passbolt version and the extension.
I have some issues:
after “sudo -u www-data composer install –no-dev”
I receive a message:
# Package webmozart/path-util is abandoned, you should avoid using it. Use symfony/filesystem instead.
Hello,
thanks for the nice tutorial. After doing that, I have a problem connecting with the mobile app from IOS, it says “Network Request Validation failed”.
Additionally I cannot sse images, they are pointing to the domain passbolt.test. Do you have an idea where I can change that?
Thnaks in advance,
Daniel
Hello Daniel,
I have the exact same problem : “Network Request Validation Failed”.
Did you find a solution ?
I’m using CloudFlare Tunnel to access my server. Could it be the reason ?
Thanks
Laurent
I keep getting the same error no matter what I try: No Security.salt placeholder to replace.