How to Set Up SMTP Relay Between 2 Postfix SMTP Servers on Ubuntu
Previously we discussed setting up Postfix SMTP relay with mailjet, which is useful when you have to use a commercial SMTP relay service. This tutorial will be showing you how to set up SMTP relay between 2 Postfix SMTP servers on Ubuntu.
Use Case
Let’s say there are two servers: server A and server B.
- You have set up a full-featured mail server on server A with Postfix as the SMTP server. You can use it to send emails directly to recipients, because port 25 isn’t blocked.
- Later you use server B to set up a website, which needs to send notification emails to users.
You can set up another mail server on server B, but it’s a waste of time and hardware resources. A more sensible solution is to install Postfix SMTP server on server B and configure it to send emails via server A, which can relay emails from server B to the final recipients. Server A has built up its IP reputation, so you don’t have to build IP reputation for server B.
If you run WordPress on your own Linux server, I recommend you follow this tutorial to set up Postfix SMTP relay. This way, you can get rid of SMTP plugins in WordPress. WordPress plugins slow down your site and they can be vulnerable, such as the recent vulnerability found in the Easy WP SMTP plugin, which allows unauthorized users to modify WordPress options and execute malicious code. My site has been compromised once, because of vulnerability in WordPress plugin. So I get rid of as many plugins as I can, when I can implement the same function with the underlying operating system.
Without further ado, let’s get started.
Installing Postfix SMTP Server on Server B
First, let’s install Postfix SMTP server on server B with the following command. If Postfix is already running on server B, then skip installing Postfix, but you still need to install the libsasl2-modules package.
sudo apt install postfix libsasl2-modules
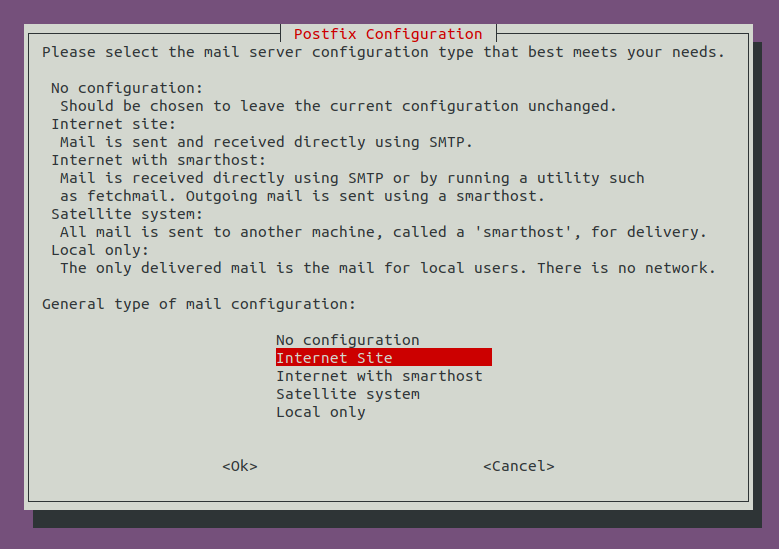
When you see the following message, press Enter to choose the second option: Internet Site.
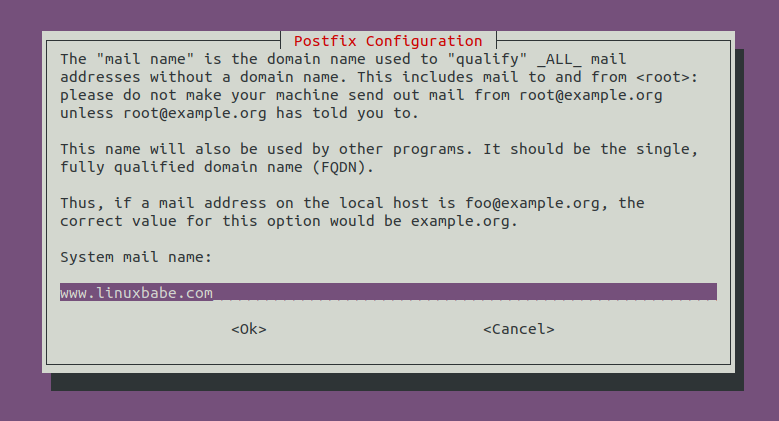
Next, set the system mail name. For example, I enter my domain name www.linuxbabe.com. Note that you should not enter your main domain name like linuxbabe.com, because that will make server B as a destination for your main domain name, which means emails generated from server B for [email protected] will be sent to server B itself, instead of server A.
Once Postfix SMTP server is installed on server B, let’s configure SMTP relay.
Postfix SMTP Relay via port 587
Edit the Postfix main configuration file on server B.
sudo nano /etc/postfix/main.cf
Find the following line.
relayhost =
By default, its value is not set. You need to set the hostname of server A (your mail server) as the relay host like below.
relayhost = mail.linuxbabe.com:587
Then add the following lines to the end of this file to configure SASL authentication. We specify that the /etc/postfix/sasl_password file contains the username and password.
# outbound relay configurations smtp_sasl_auth_enable = yes smtp_sasl_password_maps = hash:/etc/postfix/sasl_passwd smtp_sasl_security_options = noanonymous smtp_tls_security_level = may header_size_limit = 4096000
Save and close the file. Next, you should create a dedicated email account on your mail server, so server B can use this email account to login via port 587. After that, create the /etc/postfix/sasl_passwd file.
sudo nano /etc/postfix/sasl_passwd
Add the SMTP relay host and SMTP credentials to this file like below. Replace these values with the hostname of your own mail server, the email account and password. Notice that there’s a colon between the email account and password.
mail.linuxbabe.com:587 [email protected]:password
Save and close the file. Then create the corresponding hash db file with postmap.
sudo postmap /etc/postfix/sasl_passwd
Now you should have a file /etc/postfix/sasl_passwd.db. Restart Postfix for the changes to take effect.
sudo systemctl restart postfix
By default, sasl_passwd and sasl_passwd.db file can be read by any user on the server. Change the permission to 600 so only root can read and write to these two files.
sudo chmod 0600 /etc/postfix/sasl_passwd /etc/postfix/sasl_passwd.db
From now on, Websites on server B can use Postfix to send emails, which will be relayed through your mail server. Note that many web applications provides two email-sending modes:
- SMTP
- Sendmail
SMTP usually refers to the SMTP relay function in the web application itself and sendmail refers to using the SMTP server on the underlying operating system. You need to choose the sendmail option in order to use Postfix SMTP relay. If you installed SMTP plugin on your WordPress site, remove the SMTP plugin and WordPress will use Postfix SMTP relay.
If You Have iRedMail on Server A
If you used iRedMail to set up mail server on server A, then the iRedAPD policy daemon will likely to reject email relay from server B, because the sender is not same as SMTP authenticate username. To solve this problem, we need to add the SMTP authentication username to the allowed list.
Edit the iRedAPD configuration file.
sudo nano /opt/iredapd/settings.py
Add the following line at the end of the file. Replace the red text as necessary.
ALLOWED_LOGIN_MISMATCH_SENDERS = ['[email protected]']
Save and close the file. Then restart iRedAPD for the change to take effect.
sudo systemctl restart iredapd
Preventing Spammers on Server B
By default, Postfix SMTP server listens on all active interfaces on the machine. Since the Postfix SMTP server on server B is only used for sending transactional emails to users, we can make it listens on localhost only, so bad actors can’t send spam to it.
Edit the Postfix main configuration file on server B.
sudo nano /etc/postfix/main.cf
Find the following line.
inet_interfaces = all
Change it to:
inet_interfaces = loopback-only
Save and close the file. Restart Postfix for the change to take effect.
sudo systemctl restart postfix
Setting the From Address, From Name and Return-Path
By default, the From address and From name are the same as the email account that is used to authenticate login, and the return-path will be something like www-data@postfix-hostname. You can set custom From address, From name and Return-Path in your web application.
Let’s use WordPress as an example. You can add the following lines in your WordPress theme’s functions.php file to override the default From address, From name and return-path. Replace the red text as necessary. You should create the From email address on your mail server to prevent send failure.
// Function to change From email address
function wpb_sender_email( $original_email_address ) {
return '[email protected]';
}
// Function to change sender name
function wpb_sender_name( $original_email_from ) {
return 'LinuxBabe';
}
// Set return-path the same as From address
function fix_my_email_return_path( $phpmailer ) {
$phpmailer->Sender = $phpmailer->From;
}
// Hooking up our functions to WordPress filters
add_filter( 'wp_mail_from', 'wpb_sender_email' );
add_filter( 'wp_mail_from_name', 'wpb_sender_name' );
add_action( 'phpmailer_init', 'fix_my_email_return_path' );
Save the file and you are done.
Checking Email Sender Score
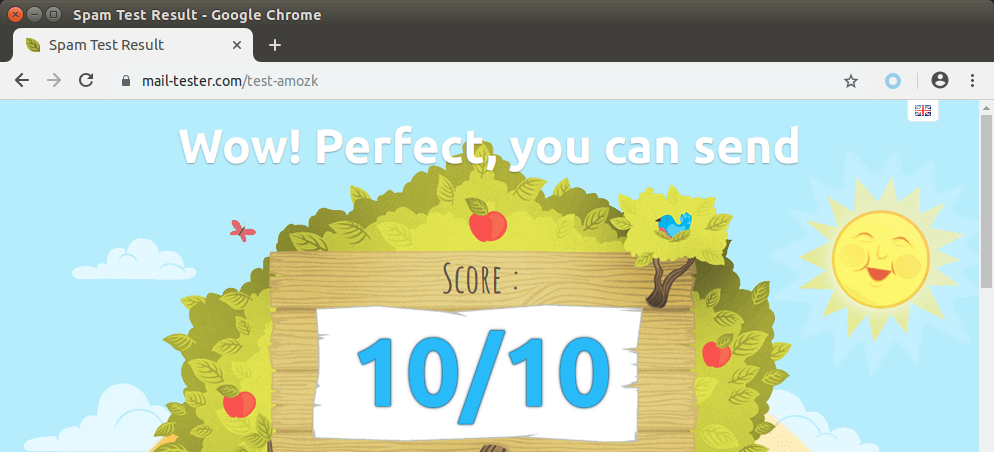
Now you should go to https://www.mail-tester.com and send an email from the website on server B to the mail tester address. Check your sender score and see if SPF, DKIM and DMARC would pass. As you can see, I got a perfect score.
If There Are Multiple Websites on Server B
If you have multiple websites running on server B, then you need to use different relay host for each domain name. Edit the Postfix main configuration file on server B.
sudo nano /etc/postfix/main.cf
Add the following line in the file, which tells Postfix that we want to use different relayhosts for each sender domain.
sender_dependent_relayhost_maps = hash:/etc/postfix/relay_by_sender
Then create the file.
sudo nano /etc/postfix/relay_by_sender
Add parameters like below. The lefthand side are the sender domains. The righthand side are the hostnames of the mail servers and the port number.
@domain1.com mail.domain1.com:587 @domain2.com mail.domain2.com:587
Save and close the file. Then edit the SASL authentication file.
sudo nano /etc/postfix/sasl_passwd
Add login credentials like below.
mail.domain1.com [email protected]:password mail.domain2.com [email protected]:password
Save and close the file. Then create the hash db file.
sudo postmap /etc/postfix/relay_by_sender sudo postmap /etc/postfix/sasl_passwd
Restart Postfix SMTP server for the changes to take effect.
sudo systemctl restart postfix
From here on out, emails with domain1.com in the Envelope From address will be relayed via mail.domain1.com and emails with domain2.com in the Envelope From address will be relayed via mail.domain2.com. Emails with other domains names in the Envelope From address will be relayed via the host specified for relayhost parameter.
Mail.domain1.com and mail.domain2.com can point to the same IP address, which means the two domain names are using the same mail server. You can check one of the following tutorials to host multiple domains on a single mail server.
- How to host multiple mail domains in iRedMail with Nginx
- How to host multiple mail domains in Modoboa mail server
You can also host emails on different servers for the two domain names. If you have multiple WordPress sites on server B, you should also change each functions.php file in your WordPress themes to set custom From address and names for each domain name.
Removing Sensitive Information from Email Headers
By default, Postfix SMTP server will add a Received: email header, recording the IP address of server B, which can leak the IP address of your website (If it’s behind CDN). You can tell Postfix to ignore it. Create a header check file on server A.
sudo nano /etc/postfix/smtp_header_checks
Put the following lines into the file.
/^Received:/ IGNORE
Save and close the file. Then edit the Postfix main configuration file.
sudo nano /etc/postfix/main.cf
Add the following line at the end of the file.
smtp_header_checks = regexp:/etc/postfix/smtp_header_checks
Save and close the file. Then run the following command to rebuild hash table.
sudo postmap /etc/postfix/smtp_header_checks
Reload Postfix for the change to take effect.
sudo systemctl reload postfix
Now Postfix won’t include those sensitive information in email headers. Note that some folks may also like removing the MIME-Version header. I don’t recommend it, because this will cause DKIM verification failure.
Conclusion
I hope this tutorial helped you set up SMTP relay between 2 Postfix SMTP servers. As always, if you found this post useful, then subscribe to our free newsletter to get more tips and tricks. Take care 🙂



Hello everybody, if you need to set another relay for second domain located on another server:
Hi again. Quick question:
When I send an email from webserver2 through relay (mail.domain.com:587) get an error:
Can you help please?
I found the solution:
On my webserver
Add this line to /etc/postfix/main.cf
Then create file named /etc/postfix/generic
With content
Save file, postmap and reload postfix
Maybe it can helps to anybody.
Thanks for the tutorials! Very helpful! I followed your other tutorials but haven’t been able to get the SMTP relay to work. I’m running CyberPanel on Server B and iRedMail on Server A. I’m trying to get a form mail to relay through an email address on Server A. No luck. Any guidance? I’m a neophyte so please go easy on me. lol!
Sir, can I send more than 100,000 mails with iredMail daily, per day?
If yes then your mention scalahost vps perfect for this.
Please, let me know if possible without ban.
If not then which mail server (MTA) best for sending unlimited emails daily.
Thank you for this interesting article.
Yes, you can install iRedmail on scalahosting VPS to send more than 100,000 email per day, but please send legitimate emails only, don’t send spam.
Why Scalehosting VPS please?
Scalahosting VPS has very good IP reputation. However, recently the pricing of the self-hosted VPS plan has increased significantly ($59/month), so I don’t recommend it anymore.
Now I recommend Kamatera VPS, 30 day free trial.
How to Create a Linux VPS Server on Kamatera
Thanks for the tutorials! Very helpful! I am facing problem when using my own smtp in an application and allow a mail account it is working fine but not saved sent email in sent items as gmail behave. Please guide to solve this problem.