Part 2: Install Dovecot IMAP server on Ubuntu & Enable TLS Encryption
This is part 2 of building your own secure email server on Ubuntu from scratch tutorial series. In part 1, we showed you how to set up a basic Postfix SMTP server. In this tutorial, we are going to configure our email server so that we can receive and send emails using a desktop email client like Mozilla Thunderbird or Microsoft Outlook.
To be able to send emails using a desktop email client, we need to enable the submission service in Postfix. To receive emails using a desktop email client, we can install an open-source IMAP server named Dovecot on the Ubuntu server. And to encrypt our communications, we need a TLS certificate.
Open Ports in Firewall
Ubuntu doesn’t enable firewall by default. If you have enabled the UFW firewall, then you need to run the following command to open email related ports in firewall.
sudo ufw allow 80,443,587,465,143,993/tcp
If you use POP3 to fetch emails (I personally don’t), then also open port 110 and 995.
sudo ufw allow 110,995/tcp
Securing Email Server Traffic with TLS Certificate
When we configure our desktop email clients, It’s always a good idea to enable TLS encryption to prevent hackers from snooping on our emails. We can easily obtain a free TLS certificate from Let’s Encrypt. Issue the following commands to install Let’s Encrypt client (certbot) on Ubuntu server from the default software repository.
sudo apt update sudo apt dist-upgrade sudo apt install certbot
If you don’t have a web server running yet, I recommend you install one (Apache or Nginx), because it’s easier to obtain and install TLS certificate with a web server than using other methods. And in a later tutorial, I will show you how to set up webmail, which requires running a web server.
If you use Apache web server, you need to install the Apache plugin. (The following command will install Apache web server if it’s not already installed on your system.)
sudo apt install python3-certbot-apache
If you use Nginx web server, then install the Nginx plugin. (The following command will install Nginx web server if it’s not already installed on your system.)
sudo apt install python3-certbot-nginx
Obtaining TLS Certificate with Apache Web Server
You need to have an Apache virtual host for mail.your-domain.com before obtaining Let’s Encrypt TLS certificate. Create the virtual host file:
sudo nano /etc/apache2/sites-available/mail.your-domain.com.conf
Then paste the following text into the file.
<VirtualHost *:80>
ServerName mail.your-domain.com
DocumentRoot /var/www/html/
</VirtualHost>
Save and close the file. Enable this virtual host.
sudo a2ensite mail.your-domain.com.conf
Then disable the default virtual host, because it might interfere with other virtual hosts.
sudo a2dissite 000-default
Reload Apache for the changes to take effect.
sudo systemctl reload apache2
Once the virtual host is created and enabled, run the following command to obtain Let’s Encrypt TLS certificate.
sudo certbot certonly -a apache --agree-tos --no-eff-email --staple-ocsp --email [email protected] -d mail.your-domain.com
Where:
-a apache: Use the Apache plugin for authentication--agree-tos: Agree to terms of service.--no-eff-email: Don’t receive emails from EFF foundation.--staple-ocsp: Enables OCSP Stapling. A valid OCSP response is stapled to the certificate that the server offers during TLS.--email: Enter your email address, which is used for important notifications and account recovery.-d: domain, aka your mail server hostname.
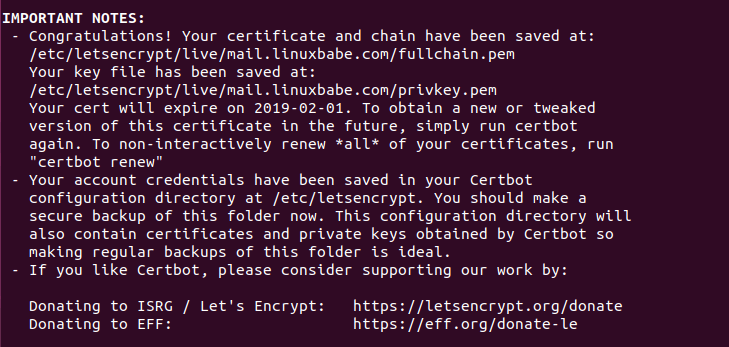
Substitute the red text with your actual data. You should see the following which means the certificate is successfully obtained. You can also see the directory under which your cert is stored.
If there’s a problem when trying to obtain the TLS certificate, please read the following article to learn how to troubleshoot.
Obtaining TLS Certificate with Nginx Web Server
You need to have an Nginx virtual host for mail.your-domain.com before obtaining Let’s Encrypt TLS certificate. Create the virtual host file:
sudo nano /etc/nginx/conf.d/mail.your-domain.com.conf
Next, paste the following text into the file.
server {
listen 80;
listen [::]:80;
server_name mail.your-domain.com;
root /usr/share/nginx/html/;
location ~ /.well-known/acme-challenge {
allow all;
}
}
Save and close the file. Make sure the /usr/share/nginx/html/ directory exists on your server.
sudo mkdir -p /usr/share/nginx/html/
Reload Nginx for the changes to take effect.
sudo systemctl reload nginx
Once the virtual host is created and enabled, run the following command to obtain Let’s Encrypt certificate with Nginx plugin.
sudo certbot certonly -a nginx --agree-tos --no-eff-email --staple-ocsp --email [email protected] -d mail.your-domain.com
Where:
-a nginx: Use the Nginx plugin for authentication--agree-tos: Agree to terms of service.--no-eff-email: Don’t receive emails from EFF foundation.--staple-ocsp: Enables OCSP Stapling. A valid OCSP response is stapled to the certificate that the server offers during TLS.--email: Enter your email address, which is used for important notifications and account recovery.-d: domain, aka your mail server hostname.
You should see the following which means the certificate is successfully obtained. You can also see the directory under which your cert is stored.
If there’s a problem when trying to obtain the TLS certificate, please read the following article to learn how to troubleshoot.
Enable Submission Service in Postfix
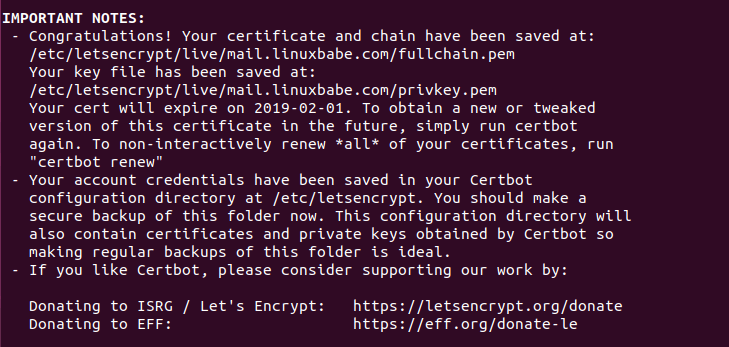
To send emails from a desktop email client, we need to enable the submission service of Postfix so that the email client can submit emails to Postfix SMTP server. Edit the master.cf file.
sudo nano /etc/postfix/master.cf
In submission section, uncomment or add the following lines. Please allow at least one whitespace (tab or spacebar) before -o. In postfix configurations, a preceding whitespace character means that this line is continuation of the previous line. (By default the submission section is commented out. You can copy the following lines and paste them into the file, so you don’t have to manually uncomment or add new text.)
submission inet n - y - - smtpd -o syslog_name=postfix/submission -o smtpd_tls_security_level=encrypt -o smtpd_tls_wrappermode=no -o smtpd_sasl_auth_enable=yes -o smtpd_relay_restrictions=permit_sasl_authenticated,reject -o smtpd_recipient_restrictions=permit_mynetworks,permit_sasl_authenticated,reject -o smtpd_sasl_type=dovecot -o smtpd_sasl_path=private/auth
The above configuration enables the submission daemon of Postfix and requires TLS encryption. So later on our desktop email client can connect to the submission daemon in TLS encryption. The submission daemon listens on TCP port 587. STARTTLS is used to encrypt communications between email client and the submission daemon.
Microsoft Outlook mail client only supports submission over port 465. If you are going to use Microsoft Outlook, then you also need to enable submission service on port 465 by adding the following lines in the file.
smtps inet n - y - - smtpd -o syslog_name=postfix/smtps -o smtpd_tls_wrappermode=yes -o smtpd_sasl_auth_enable=yes -o smtpd_relay_restrictions=permit_sasl_authenticated,reject -o smtpd_recipient_restrictions=permit_mynetworks,permit_sasl_authenticated,reject -o smtpd_sasl_type=dovecot -o smtpd_sasl_path=private/auth
Save and close the file.
Hint: The SMTP protocol is used when an email client submits emails to an SMTP server.
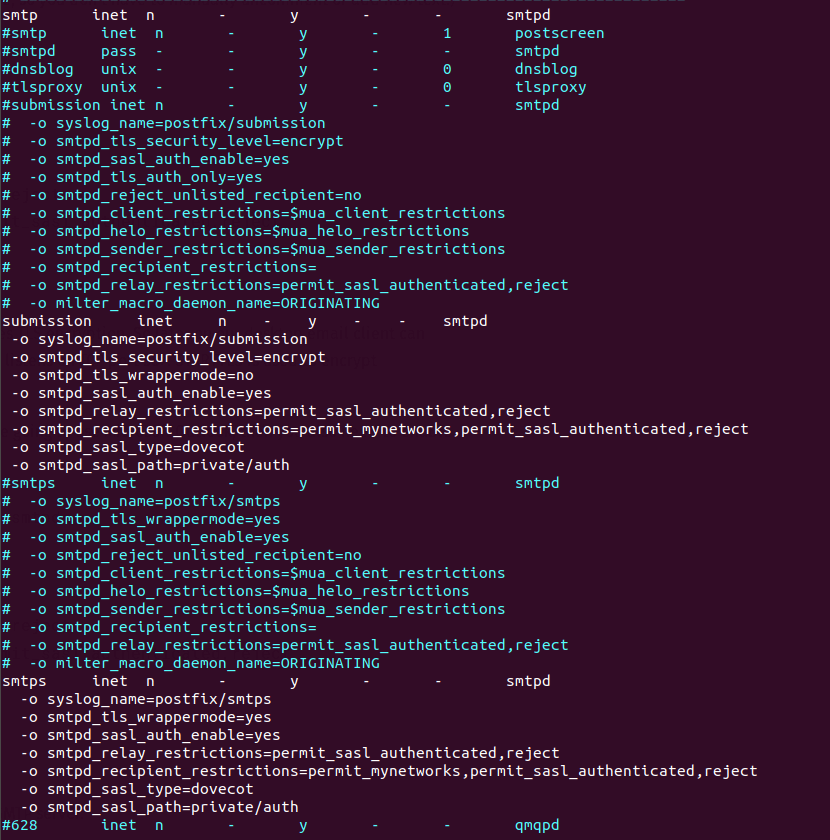
Next, we need to specify the location of TLS certificate and private key in Postfix configuration file. Edit main.cf file.
sudo nano /etc/postfix/main.cf
Edit the TLS parameter as follows. Remember to replace mail.your-domain.com with your real hostname.
#Enable TLS Encryption when Postfix receives incoming emails smtpd_tls_cert_file=/etc/letsencrypt/live/mail.your-domain.com/fullchain.pem smtpd_tls_key_file=/etc/letsencrypt/live/mail.your-domain.com/privkey.pem smtpd_tls_security_level=may smtpd_tls_loglevel = 1 smtpd_tls_session_cache_database = btree:${data_directory}/smtpd_scache #Enable TLS Encryption when Postfix sends outgoing emails smtp_tls_security_level = may smtp_tls_loglevel = 1 smtp_tls_session_cache_database = btree:${data_directory}/smtp_scache #Enforce TLSv1.3 or TLSv1.2 smtpd_tls_mandatory_protocols = !SSLv2, !SSLv3, !TLSv1, !TLSv1.1 smtpd_tls_protocols = !SSLv2, !SSLv3, !TLSv1, !TLSv1.1 smtp_tls_mandatory_protocols = !SSLv2, !SSLv3, !TLSv1, !TLSv1.1 smtp_tls_protocols = !SSLv2, !SSLv3, !TLSv1, !TLSv1.1
Your Let’s Encrypt certificate and private key are stored under /etc/letsencrypt/live/mail.your-domain.com/ directory.
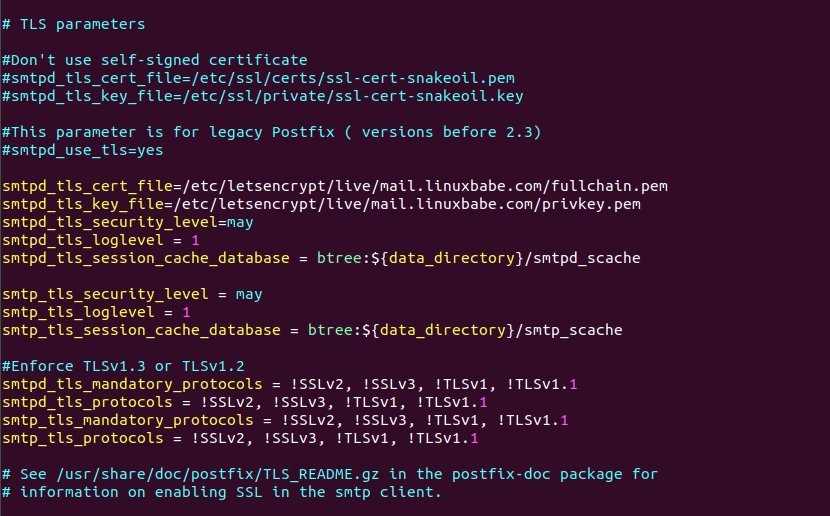
Save and close the file. Then restart Postfix.
sudo systemctl restart postfix
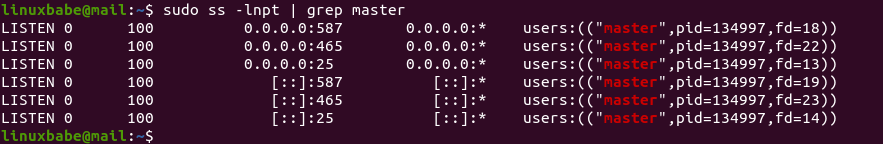
If you run the following command, you will see Postfix is now listening on port 587 and 465.
sudo ss -lnpt | grep master
Installing Dovecot IMAP Server
Enter the following command to install Dovecot core package and the IMAP daemon package on Ubuntu server.
sudo apt install dovecot-core dovecot-imapd
If you use POP3 to fetch emails, then also install the dovecot-pop3d package.
sudo apt install dovecot-pop3d
Check Dovecot version:
dovecot --version
Sample output:
2.3.16 (7e2e900c1a)
Enabling IMAP/POP3 Protocol
Edit the main config file.
sudo nano /etc/dovecot/dovecot.conf
Add the following line to enable IMAP protocol.
protocols = imap
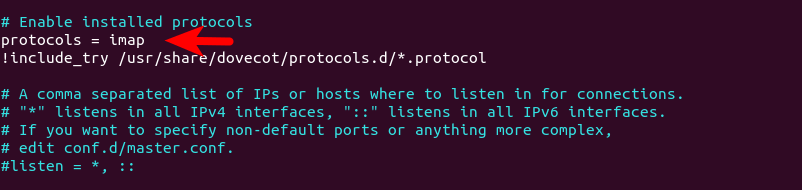
If you use POP3 to fetch emails, then also add POP3 protocol.
protocols = imap pop3
Save and close the file.
Configuring Mailbox Location
By default, Postfix and Dovecot use mbox format to store emails. Each user’s emails are stored in a single file /var/mail/username. You can run the following command to find the mail spool directory.
postconf mail_spool_directory
Sample output:
mail_spool_directory = /var/mail
However, nowadays it’s almost always you want to use the Maildir format to store email messages. The config file for mailbox location is /etc/dovecot/conf.d/10-mail.conf.
sudo nano /etc/dovecot/conf.d/10-mail.conf
The default configuration uses mbox mail format.
mail_location = mbox:~/mail:INBOX=/var/mail/%u
Change it to the following to make Dovecot use the Maildir format. Email messages will be stored under the Maildir directory under each user’s home directory.
mail_location = maildir:~/Maildir
We need to add the following line in the file. (On Ubuntu 18.04 and 20.04, this line is already in the file.)
mail_privileged_group = mail
Save and close the file. Then add dovecot to the mail group so that Dovecot can read the INBOX.
sudo adduser dovecot mail
Using Dovecot to Deliver Email to Message Store
Although we configured Dovecot to store emails in Maildir format, by default, Postfix uses its built-in local delivery agent (LDA) to move inbound emails to the message store (inbox, sent, trash, Junk, etc), and it will be saved in mbox format.
We need to configure Postfix to pass incoming emails to Dovecot, via the LMTP protocol, which is a simplified version of SMTP, so incoming emails will saved in Maildir format by Dovecot. LMTP allows for a highly scalable and reliable mail system. It also allows us to use the sieve plugin to filter inbound messages to different folders.
Install the Dovecot LMTP Server.
sudo apt install dovecot-lmtpd
Edit the Dovecot main configuration file.
sudo nano /etc/dovecot/dovecot.conf
Add lmtp to the supported protocols.
protocols = imap lmtp
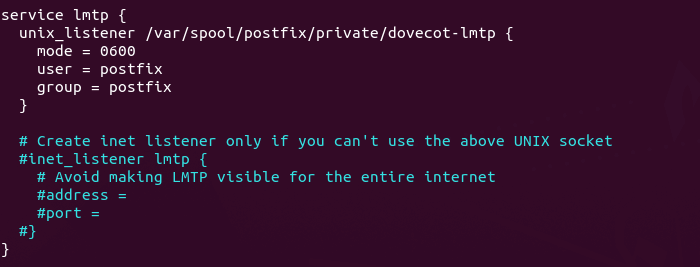
Save and close the file. Then edit the Dovecot 10-master.conf file.
sudo nano /etc/dovecot/conf.d/10-master.conf
Change the lmtp service definition to the following.
service lmtp {
unix_listener /var/spool/postfix/private/dovecot-lmtp {
mode = 0600
user = postfix
group = postfix
}
}
Next, edit the Postfix main configuration file.
sudo nano /etc/postfix/main.cf
Add the following lines at the end of the file. The first line tells Postfix to deliver incoming emails to local message store via the Dovecot LMTP server. The second line disables SMTPUTF8 in Postfix, because Dovecot-LMTP doesn’t support this email extension.
mailbox_transport = lmtp:unix:private/dovecot-lmtp smtputf8_enable = no
Save and close the file.
Configuring Authentication Mechanism
Edit the authentication config file.
sudo nano /etc/dovecot/conf.d/10-auth.conf
Uncomment the following line.
disable_plaintext_auth = yes
It will disable plaintext authentication when there’s no SSL/TLS encryption. Then find the following line,
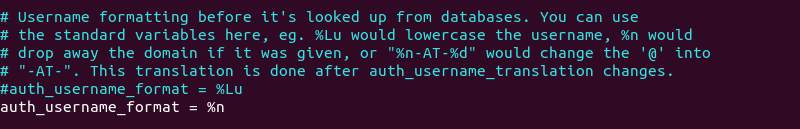
#auth_username_format = %Lu
Uncomment it and change its value to %n.
auth_username_format = %n
By default, when Dovecot tries to find or deliver emails for a user, it uses the full email address. Since in this part, we only set up canonical mailbox users (using OS users as mailbox users), Dovecot can’t find the mailbox user in full domain format ([email protected]), so we need to set auth_username_format = %n to drop the domain part, then Dovecot should be able to find the mailbox user. This also allows us to use the full email address ([email protected]) to log in.
Next, find the following line.
auth_mechanisms = plain
This line only enables the PLAIN authentication mechanism. LOGIN is another authentication mechanism you probably want to add to support older email clients.
auth_mechanisms = plain login
Save and close the file.
Configuring SSL/TLS Encryption
Next, edit SSL/TLS config file.
sudo nano /etc/dovecot/conf.d/10-ssl.conf
Change ssl = yes to ssl = required to enforce encryption.
ssl = required
Then find the following lines.
ssl_cert = </etc/dovecot/private/dovecot.pem ssl_key = </etc/dovecot/private/dovecot.key
By default, Dovecot uses a self-signed TLS certificate. Replace them with the following values, which specify the location of your Let’s Encrypt TLS certificate and private key. Don’t leave out the < character. It’s necessary.
ssl_cert = </etc/letsencrypt/live/mail.your-domain.com/fullchain.pem ssl_key = </etc/letsencrypt/live/mail.your-domain.com/privkey.pem
Find the following line.
#ssl_prefer_server_ciphers = no
It’s a good practice to prefer the server’s order of ciphers over client’s. So uncomment this line and change the value to yes.
ssl_prefer_server_ciphers = yes
If you use Ubuntu 20.04 or Ubuntu 22.04, disable insecure SSLv3, TLSv1 and TLSv1.1 by adding the following line.
ssl_min_protocol = TLSv1.2
If you are using Dovecot version 2.2.x (as in Ubuntu 18.04), you should add the following line to disable insecure TLS.
ssl_protocols = !SSLv3 !TLSv1 !TLSv1.1
Save and close the file.
Disable the FIPS Providers in OpenSSL on Ubuntu 22.04
Ubuntu 22.04 ships with OpenSSL 3.0, which features a FIPS provider. However, it won’t work with Dovecot. We need to diable the FIPS provider.
sudo nano /etc/ssl/openssl.cnf
Find the following line (line 54).
providers = provider_sect
Add a # character to comment it out.
#providers = provider_sect
Save and close the file.
If you don’t disable the FIPS provider in OpenSSL, Dovecot would produce the following error.
imap-login: Error: Failed to initialize SSL server context: Can't load SSL certificate: error:25066067:DSO support routines:dlfcn_load:could not load the shared library: filename(libproviders.so)
Configuring SASL Authentication
Edit the following file.
sudo nano /etc/dovecot/conf.d/10-master.conf
Change service auth section to the following so that Postfix can find the Dovecot authentication server. Please be careful about the syntax. Every opening bracket should be terminated by a closing bracket.
service auth {
unix_listener /var/spool/postfix/private/auth {
mode = 0660
user = postfix
group = postfix
}
}

Save and close the file.
Auto-create Sent and Trash Folder
Edit the below config file.
sudo nano /etc/dovecot/conf.d/15-mailboxes.conf
To auto-create a folder, simply add the following line in the mailbox section.
auto = create
Example:
mailbox Trash {
auto = create
special_use = \Trash
}
Some common folders you will want to create includes: Drafts, Junk, Trash and Sent. The Sent folder will be created under the user’s home directory when the user send the first email. The Trash folder will be created when the user deletes an email for the first time, etc. After you save and close all above config files, restart Postfix and Dovecot.
sudo systemctl restart postfix dovecot
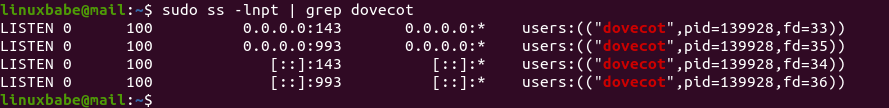
Dovecot will be listening on port 143 (IMAP) and 993 (IMAPS), as can be seen with:
sudo ss -lnpt | grep dovecot
If there’s a configuration error, dovecot will fail to restart, so it’s a good idea to check if Dovecot is running with the following command.
systemctl status dovecot
Configure Desktop Email Client
Now open up your desktop email client such as Mozilla Thunderbird. Go to Edit -> Account Settings -> Account Actions -> Add Mail Account to add a mail account.
- In the incoming server section, select IMAP protocol, enter
mail.your-domain.comas the server name, choose port 143 and STARTTLS. Choosenormal passwordas the authentication method. - In the outgoing section, select SMTP protocol, enter
mail.your-domain.comas the server name, choose port 587 and STARTTLS. Choosenormal passwordas the authentication method.
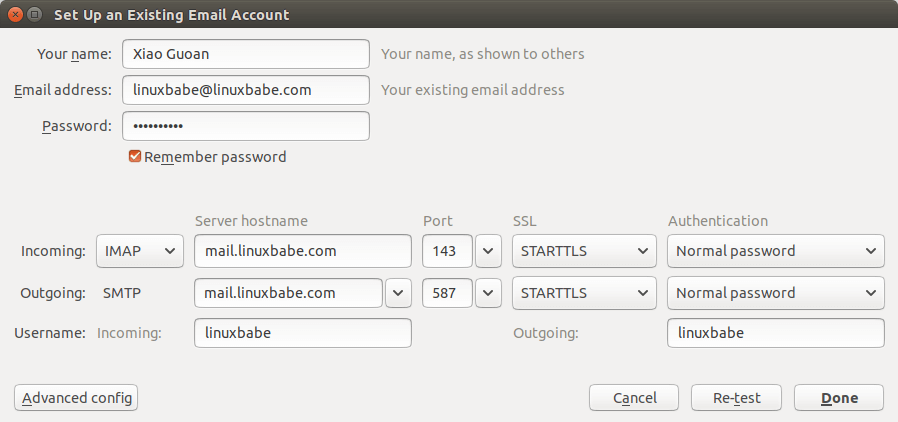
Hint 1: You can also use port 993 with SSL/TLS encryption for IMAP, and use port 465 with SSL/TLS encryption for SMTP. You should NOT use port 25 as the SMTP port in mail clients to submit outgoing emails.
Hint 2: If you use Microsoft 365 Outlook email client, then you shouldn’t enable Secure Password Authentication (SPA), which is a proprietary Microsoft protocol. Your password is already encrypted by TLS.
You should now be able to connect to your own email server and also send and receive emails with your desktop email client!
We use local Unix accounts as email addresses, as we did in part 1. For example, if you have a user called user1 on your Ubuntu server, then you have an email address: [email protected], and the password for the email address is the same password for the user1 user. To create a local Unix account, run
sudo adduser user1
Note: Dovecot doesn’t allow you to log in with the root account. You need to create separate user accounts.
You can list all available mailbox users with:
sudo doveadm user '*'
It’s recommended to restart Dovecot after adding users, so Dovecot can recognize new mailbox users.
sudo systemctl restart dovecot
Troubleshooting Tips
As a rule of thumb, you should always check the mail log (/var/log/mail.log) on your mail server when an error happens. The following is a list of specific errors and troubleshooting tips.
Can’t login from Mail Clients
If you can’t log into your mail server from a desktop mail client, scan your mail server to find if the ports (TCP 587, 465, 143, and 993) are open. Note that you should run the following command from another Linux computer or server. If you run it on your mail server, then the ports will always appear to be open.
sudo nmap mail.your-domain.com
And check if Dovecot is running.
systemctl status dovecot
You can also check the mail log (/var/log/mail.log), which may give you some clues. If Dovecot fails to start, the error might not be logged to the /var/log/mail.log file, you can run the following command to see what’s wrong.
sudo journalctl -eu dovecot
For example, some folks may have the following error in the journal.
doveconf: Fatal: Error in configuration file /etc/dovecot/conf.d/10-master.conf line 78: Unknown setting
Most of the time, it’s a simple syntax error, like a missing curly bracket. Open the configuration file, go to the specified line and fix the error.
If you find the following error message in the mail log
imap-login: Error: Failed to initialize SSL server context: Can't load DH parameters: error:1408518A:SSL routines:ssl3_ctx_ctrl:dh key too small
Then open the Dovecot TLS configuration file.
sudo nano /etc/dovecot/conf.d/10-ssl.conf
Add the following line in this file.
ssl_dh = </etc/dovecot/dh.pem
Save and close the file. Then generate the DH parameter file with:
sudo openssl dhparam -out /etc/dovecot/dh.pem 4096
Restart Dovecot for the changes to take effect.
Cloudflare DNS
As I said in part 1, if you use Cloudflare DNS service, you should not enable the CDN (proxy) feature when creating DNS A record and AAAA record for the hostname of your mail server. Cloudflare doesn’t support SMTP or IMAP proxy.
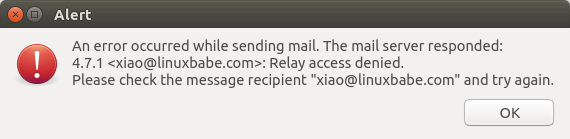
Relay Access Denied
If you see the “relay access denied” error when trying to send emails from a mail client, it’s most likely that you use port 25 as the SMTP port in your mail client. As I said a while ago, you should use port 587 or 465 as the SMTP port in mail clients (Mozilla Thunberbird, Microsoft Outlook, etc) to submit outgoing emails. Port 25 should be used for SMTP server to SMTP server communications.
If you see the following “relay access denied” error in the /var/log/mail.log file when trying to send emails from other mail services like Gmail to your own mail server, it’s likely that yourdomain.com is not in the list of $mydestination parameter.
NOQUEUE: reject: RCPT from mail-il1-f180.google.com[209.85.166.180]: 454 4.7.1 <[email protected]>: Relay access denied; from=<[email protected]> to=<[email protected]> proto=ESMTP helo=<mail-il1-f180.google.com>
You can display the current value of $mydestination with:
postconf mydestination
Some folks might not have the main domain name in the list like so:
mydestination = $myhostname, localhost.$mydomain, localhost
Then run the following command to add the main domain name to the list.
sudo postconf -e "mydestination = yourdomain.com, \$myhostname, localhost.\$mydomain, localhost"
Reload Postfix for the changes to take effect.
sudo systemctl reload postfix
User Doesn’t Exist
If you see the following error message in the mail log (/var/log/mail.log), it’s likely that you forgot to set auth_username_format = %n In /etc/dovecot/conf.d/10-auth.conf file.
mail postfix/lmtp[2256]: 68E00FC1A5: to=, relay=mail.example.com[private/dovecot-lmtp], delay=509, delays=509/0.03/0.03/0.02, dsn=5.1.1, status=bounced (host mail.example.com[private/dovecot-lmtp] said: 550 5.1.1 User doesn't exist: [email protected] (in reply to RCPT TO command))
iOS Mail App
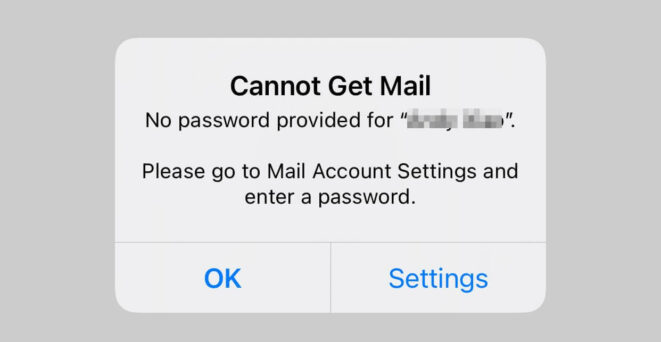
If you use the iOS Mail app to log into your mail server and encounter the following error.
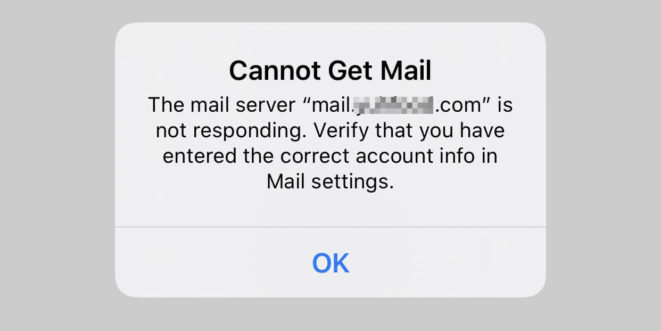
You can try to fix it by enforcing SSL encryption, for both SMTP and IMAP.
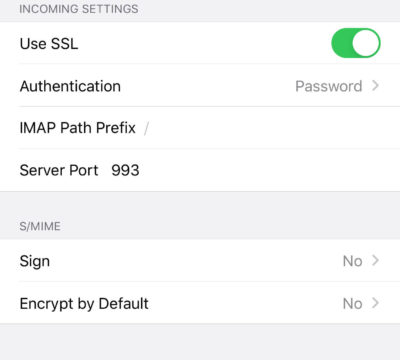
Fun fact: It seems the iOS Mail app has difficulty in supporting STARTTLS on IMAP port 143, but it supports STARTTLS on the submission port 587.
If you encounter the “No password provided” error in the iOS Mail app, it’s likely that you have a typo when entering the username in the Mail account settings, or you didn’t enable SSL in the Mail account settings.
Unable to Receive Email From Gmail, Hotmail, Yahoo Mail, etc
If you can’t receive emails from Gmail, Hotmail, Yahoo Mail, etc, here are the possible causes:
- Your MX record is wrong, or not propagated to the Internet yet.
- Your mail server hostname doesn’t have DNS A record, or is not propagated to the Internet yet.
- Your firewall doesn’t allow incoming connections to port 25. Maybe your mail server is behind a NAT?
- Postfix isn’t listening on the public IP address.
- Check the mail log (
/var/log/mail.log) to find out if there are other errors in your Postfix and Dovecot configuration.
You can use the Network Tools Email Checker to test if your SMTP server is reachable from the Internet. Just enter your domain email address and click the Go button. As you can see from the screenshot below, it successfully found my domain’s MX record and my SMTP server is reachable from the Internet.
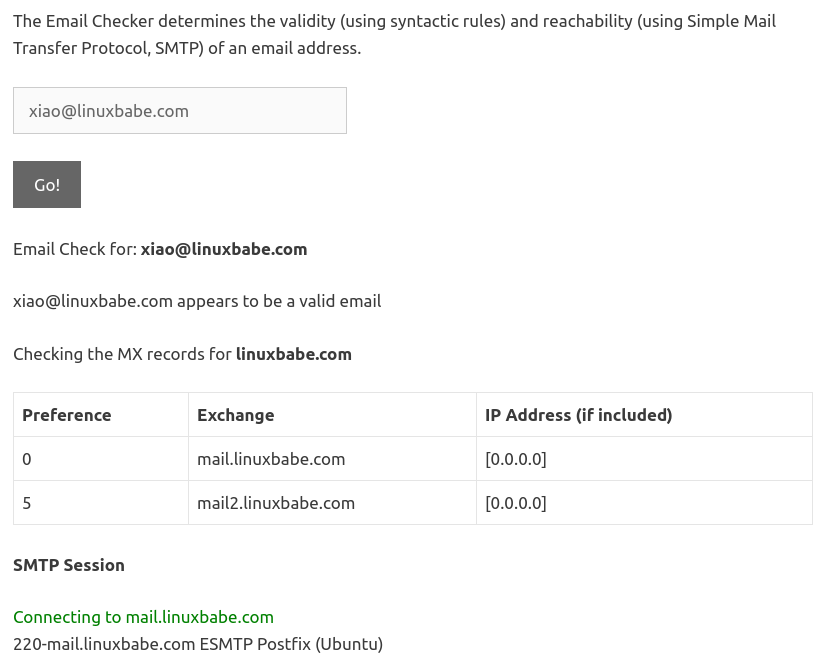
If your SMTP servers isn’t reachable from the Internet, then you have a problem in the first 4 items. If your SMTP server is reachable from the Internet, but you still can’t receive emails, check the mail log (/var/log/mail.log) to find out if there is any errors in your Postfix and Dovecot configuration.
Auto-Renew TLS Certificate
You can create Cron job to automatically renew TLS certificate. Simply open root user’s crontab file.
sudo crontab -e
If you use Apache web server, add the following line at the bottom of the file.
@daily certbot renew --quiet && systemctl reload postfix dovecot apache2
If you are using Nginx web server, then add the following line.
@daily certbot renew --quiet && systemctl reload postfix dovecot nginx
Reloading Postfix, Dovecot and the web server is necessary to make these programs pick up the new certificate and private key.
Dovecot Automatic Restart
If for any reason your Dovecot process is killed, you need to run the following command to restart it.
sudo systemctl restart dovecot
Instead of manually typing this command, we can make Dovecot automatically restart by editing the dovecot.service systemd service unit. To override the default systemd service configuration, we create a separate directory.
sudo mkdir -p /etc/systemd/system/dovecot.service.d/
Then create a file under this directory.
sudo nano /etc/systemd/system/dovecot.service.d/restart.conf
Add the following lines in the file, which will make Dovecot automatically restart 5 seconds after a failure is detected.
[Service] Restart=always RestartSec=5s
Save and close the file. Then reload systemd for the changes to take effect.
sudo systemctl daemon-reload
To check if this would work, kill Dovecot with:
sudo pkill dovecot
Then check Dovecot status. You will find Dovecot automatically restarted.
systemctl status dovecot
Next Step
I hope this article helped you set up Postfix and Dovecot on Ubuntu server. In part 3, I will show you how to create virtual mailboxes.
If you prefer to use MariaDB/MySQL database server, then follow this PostfixAdmin tutorial.
If you prefer to use PostgreSQL database server, then follow this PostfixAdmin tutorial.
As always, if you found this post useful, subscribe to our newsletter to get more tips and tricks. Take care 🙂



Finally, a tutorial that tells everything that’s needed, not only parts of it. And finally, after about 12 hours of trying, I have a working email-server. So THANKS a lot!
I m looking for a reliable source which helps me to setup mail server (Ubuntu 19.10)
This seems better I will try with this….
Looking for suggestions from all friends
Thanks
This is THE best postfix/dovecot tutorial on the web. Thank you very much for posting. You covered a lot of material in great detail, but there are still a few parts that I’m unclear on.
When adding your mail account to your mail client, how do you know what the password is? We didn’t set a password for SMTP authentication in the walkthrough. If my Ubuntu user account is ‘admin’, and my email is [email protected], do I just use my local ‘admin’ account password to connect my mail client to my new email account?
What if, in my specific case, my local Ubuntu login is ‘admin’, but I want the email address “[email protected]” to be the default for all incoming and outgoing mail? Do I need to create a “user1” local user account on Ubuntu? I’ve send some test emails from the “[email protected]” account and the SPF/DKIM checks are failing. DKIM only passes the check when I send mail from my “[email protected]” account.
Well, I continued working at it and I answered one of my questions. Yes, each email account has to have a local user account on the Ubuntu server in order to have email. I have successfully added my accounts on my Android email application. Still looking into the other issue about the “[email protected]” failing DKIM (and therefore getting detected as spam).
So after some research and trial/error since my last post, I’m still having problems with DKIM. When I email the port25.com test system from the user account that I followed this guide from, I get a pass on everything. When I email from another user on the system and get a report form port25.com, everything except DKIM passes.
If I send mail from my root account, DKIM passes. I just can’t figure out what it is about this specific user account that’s causing it to fail. And of course, it happens to be the account that I primarily want to use to send and receive mail. Without DKIM passing, I’ve noticed that Google sends my messages straight to the spam box.
Aha! I figured out why my single user account was failing DKIM, and I understand why:
DKIM takes the message content and hashes it with the private key, then puts this in the email header. I was using an additional postfix configuration option called smtp_generic_maps to “rewrite” how my sender address would appear in the recipients inbox. DKIM did not like this modification and that is what was causing the DKIM check to fail on messages from this specific user. Hopefully this helps somebody else!
Simply comment out the smtp_generic_maps parameter in your /etc/postfix/main.cf file if you’re having this problem.
Thanks again for the wonderful guide!
After doing this part, I can send email but cannot receive email. Can you help me? 🙁
SOLVED!! I made a little mistake, sorry
This is the best guide for mail servers (for me now), THANKS YOU
I’ve got same hiccup: using email client I can send but cannot receive any email. I have followed exactly the steps in this tutorial. Would you share how you solve the problem? Thanks.
Don’t bother. Everything is fine now. Gmail was slow. Thanks.
Great tutorial, worked perfectly, thanks!
Hello,
In the command:
sudo certbot –nginx –agree-tos –redirect –hsts –email your-email-address -d mail.your-domain.com
What is the “your-email-address” I should provide ?
Kind regards,
Daniel
Your email address 🙂 ([email protected]). It’s used to receive important notifications about your certificate.
Hello,
My domain is not a .com one, it is a .co.uk (let’s say test.co.uk)
How should I replace “your-domain” in:
“sudo nano /etc/nginx/conf.d/mail.your-domain.com.conf” ?
Kind regards,
Daniel
You can run this command.
Hello Xiao,
Thank you very much for the guide, all works for me.
Also, thank you for the support !!!
Kind regards,
Daniel Orkan
Once again. Well done. Got everything working perfectly. I couldn’t find the “buy me a beer” link, but thanks for a very thorough job. Have you done an article on virtual mailboxes yet?
Yes, you can create virtual mailbox with Postfixadmin.
You can support this site on this page 🙂
I cannot thank you enough.
Beautifully written article.
Glad to know it’s working for you 🙂
Biiiiig thank you, Xiao!!!
before “sudo certbot –apache –agree-tos –redirect –hsts –email your-email-address -d mail.your-domain.com”
need to do “sudo apt-get update && sudo apt-get dist-upgrade”, cause some certbot python packages need to be upgraded. You got the error, while otbain certificates, if you dont upgrade some packages. Sorry for bad english.
You absolute boss.
I’ve rarely found a tutorial which just works.. for something so complicated and head spinning as well.
Kudos mate, really.
I can’t seem to receive any external mail (ie: from gmail) – but everything else seems to be working well. Any thoughts?
found the solution – just needed to run this:
WRONG PORT LISTED ABOVE:
still 5 star rating! very precise and plain in language and logic writing!! Thank you very much!!!
Question – When opening the ports, why not just do ufw allow dovecot?
First, there’s no “dovecot” UFW profile.
The profiles installed by the
dovecotpackage are “Dovecot IMAP” and “Dovecot Secure IMAP”, which correspond to port 143 and port 993 respectively. They allow mail clients to fetch emails from the mail server.But you also need to open port 587 and 465 for mail clients to submit emails. And if you use webmail, open port 80 and 443.
You can run the following command to display available UFW profiles.
Then you can use the command below to check which port a profile allows, like
Output
Hi,
This tutorial is really good but I have a little problem with SMTP. I have configured the server in Thunderbird and the IMAP works perfect, but when I’m going to send emails, it says me something like this “Your connection has expired with the SMTP server”.
I can send messages with the
command perfectly, so I don’t know where is the problem. If you know any solutions, please let me know it.
Thank you in advance!
Is now working, thanks for the tutorial!
Hi,
My mail server works fine, as far as I know, after following your first three tutorials. Thank again! However, I don’t know how to make use of the letsencrypt setup. Can you provide some hint, or will you consider (maybe you already have?) writing a tutorial about this?
To learn how to use Let’s Encrypt (Certbot) on Ubuntu, visit the following links.
Apache version: Properly Enable HTTPS on Apache with Let’s Encrypt on Ubuntu
Nginx version: Properly Enable HTTPS on Nginx with Let’s Encrypt on Ubuntu
It´s works when I try whith a gmail account, but when I try send a email to a icloud account, that´s not receiving… can you help me please?
Hi, it´s me again,
firstly thanks for your super complete tutorial, that´s help me a lot 😀
the problem:
I ´m in black list of icloud…..
in mail.log i see this:
… refused to talk to me: 550 5.7.0 Blocked…
How can I solve this? help me :/
Read the Postmaster information for icloud mail. Basically you need to send an email to the icloud postmaster team to ask for removal of your IP address from the blacklist.
Thanks for your support 😀 I´m gonna try that.
Superb tutorial and perfect in all aspects!
I think I made a mistake when installing postfix and for system mail name I entered: mail.mydomain.com rather than mydomain.com and now the emails are @mail.mydomain.com rather @mydomain.com.
Anything that can fix the issue?
Thanks a lot
Edit /etc/mailname file and change mail.yourdomain.com to yourdomain.com. Then restart Postfix.
Thanks for the guide!
Trying to run the clean junk folders gives me an error. Any idea?
ubuntu@mail:/home$ sudo doveadm expunge -A mailbox Trash all
doveadm(nobody): Error: User initialization failed: Namespace ”: mkdir(/nonexistent/mail) failed: Permission denied (euid=65534(nobody) egid=65534(nogroup))
doveadm(nobody): Error: User init failed
ubuntu@mail:/home$ sudo doveadm user ‘*’
nobody
ubuntu
According to
man doveadm-expunge, if the -A option is present, the command will be performed for all users, including thenobodyuser. Since the nobody user’s home directory is /nonexistent/, an error would occur because the nobody user can’t create the /nonexistent/ directory.You can ignore this error by redirecting the error to /dev/null. A better approach would be getting the user list from a file. You can list users with:
Then you can use
sedto delete the line containing the word “nobody” and save the result into a text file.Now we can use doveadm-expunge.
Note that if you use virtual mailbox domain as described in part 3, there would be no such error, because the user list is obtained from MySQL/MariaDB database.
Thank you so much for helping me understand!
First of all thank you for your documentation(s), it was really helpful for us!
After all we have a little problem. We created a same virtual user like the unix user eg: [email protected], and unix user is user1. It feels like its mixing the SMTP auth or something.
We can get the incoming emails, but we cannot send, because it’s asking SMTP pass, which perfectly fine. (We can login into roundcube.) Other virtual users works perfectly fine, but not the matching users.
Setup was built on your flow, so we using lemp, postfix, dovecot, postfixadmin and roundcube.
Could you give us tip where to start debugging our problem?
Thank you in advance!
I don’t think you can have a domain on Postfix that’s both a canonical domain (with Unix system account) and a virtual domain (with virtual users stored in MySQL/MariaDB database) at the same time.
Domains listed in
mydestinationparameter are canonical domains. If a domain is listed in thevirtual_mailbox_domainsparameter, then you can not list the domain inmydestinationparameter, as is described in Postfix documentation: NEVER list a virtual MAILBOX domain name as a mydestination domain!A virtual domain can’t have email addresses for Unix system accounts.
Thank you for your fast response.
Now i understand much clearly. If mydestination is mail.mydomain.com and virtual_mailbox_domains is mydomain.com, then i can have [email protected] mailbox independently from my Unix system account which is user1.
Could not be a problem to use the same “user” name, because the Unix system account will use the mydestination domain, right?
Yes. That’s correct.
Your help lead me to find out the problem.
When we want to use indentical username eg: user1 for unix system account and for mailbox account, then we should define the full username ([email protected]) in the email client to incoming/outgoing username.
Other virtual users can use simple username like presented on tutorial picture in document.
Thanks for all✌😁
The username for Unix system account doesn’t have a domain name.
The username for virtual domain user includes the domain part, as you can see by logging into MySQL/MariaDB database server and displaying the mailbox table in the postfixadmin database.
I’m not sure if your finding is correct. I think the username field in Thunberbird is misleading.
Thanx for the guide!
I can receive but I cannot send? Any clue what may cause it?
From mail log:
As per this guide I have in my master.cf file:
So do not have idea why this fatal error is there … or maybe it is not that?
Any help would be apreciated …
There should be no space after the comma.
Works like a charm!
Thank you!
Hello there,
At this stage I can received but when try to send it always says: Timeout when setting up SSL/TLS.
The log file of the mail client shows:
11:24:28 C: STARTTLS
11:24:28 S: 454 4.7.0 TLS not available due to local problem
11:24:28 Error: Unexpected return code 454 (expected 220):
“4.7.0 TLS not available due to local problem”.
11:24:28 Error code: 2001
11:24:28 Failed action (0). Reset observed read/write timeouts: 8/8
Can someone help with?
It’s likely that you have made a typo or something in the Postfix configuration file.
Hello Xiao & Thank You so much,
– You was right, I just redone the typing and it is now working but did not found where; I am now on way to part 3.
– Also on getting the Letsencrypt certificates you must disable the default virtual host of apache2 – “sudo a2dissite *default” – before enable your own. Otherwise it will fail every time you try to get the certificates.
—
Kindest Regards.
Disabling the default virtual host is not a must, if you have correctly configured the mail.yourdomain.com virtual host. I have obtained numerous TLS certificates without disabling the default virtual host.
Hello there,
on “Obtaining TLS Certificate with Nginx Web Server” the syntax of
... location ~ /.well-known/acme-challenge { allow all; } ...the “~” is followed by a SPACE or by the SLASH ?
It’s a space. The
~in Nginx is a regular expression. It’s not the Linux~(home directory).In the file “/etc/nginx/conf.d/mail.your-domain.com.conf”,
the line “root /var/www/mail.your-domain.com/;” move the nginx server from “Welcome to nginx!” to “403 Forbidden”,
meaning when the line is comment with “#” the server answer with “Welcome to nginx!” and when the line is uncomment the server answer with “403 Forbidden”.
Any clue why?
This is not important in part 2. Follow my Roundcube tutorial to install a webmail client, then you will be able to login from webmail client at https://mail.your-domain.com.
Hello Xiao,
I follow this ‘IT Security Guidelines for Transport Layer Security
(TLS)’ from NCSC-NL, guideline B2-1 to B2-4 and table 2, 4, 6 and 7 (in
English) witch is considered here one of the best guides to cyber
security.
The website is :
[https://english.ncsc.nl/publications/publications/2019/juni/01/it-security-guidelines-for-transport-layer-security-tls]
The test tool is : “internet.nl”
About my installation they say on Ciphers (Algorithm selections) this:
Is there any way to unused phased out Ciphers?
—
Kindest Regards,
Alex
You can add the following lines in Postfix main configuration file to improve the security of TLS connection.
However, don’t be obsessed with TLS for SMTP and IMAP servers. If you are too strict about TLS, then there will be SMTP clients that can’t establish TLS connection with your SMTP server.
Hi i am having currently problem with the setting up my account via Thunderbird for start. I went three times over all three tutorials but something is always not working, i think i am maybe wonky with my fingers or whatever. But here we go, third time is the charm. So, at the moment i am at this stage(2nd).
And when i am trying to connect via Thunderbird, what password should i use?
Because we never created that during first 2 tutorials.
Should i use password that i am using to connect via terminal?
The first two parts use local Unix accounts as email addresses. For example, if you have a user called
dejanon your Ubuntu server, then you have an email address: [email protected], and the password for the email address is the same password for thedejanuser.Thank you, i managed to login via THunderbird, but at the moment i am getting this error(in var/logs) dovecot: imap(contact): Error: Failed to autocreate mailbox Trash: Permission denied
Not sure what could be cause of this problem
please note that (at this date: 28/03/2020) in my machine: ubuntu 18.04.3 , the file: /etc/dovecot/conf.d/10-master.conf had the ports commented out, this resulted in the ports being “closed” when scanned from the outside
Other tan that, great job, I cant say wether all of this is needed to set it up in a “simple” way but anyway thanks 🙂
Hi Xiao,
I have another issues with the Thunderbird setup account:
I checked all the Q&A above in the thread and I understand that the [email protected] as the UNIX root and password. Do you have any solutions? How do I create a second: [email protected] to check it? Thanks so much.
To create another email address, simply create another Unix user account on your Ubuntu server.
Part 3 will show you how to create virtual users.
Hello,
Loving my setup… Thanks – I have followed all the way through (all 8ish parts).
I have run into one Challenge post setup, and this is confusing me.
Firstly… worth noting – Your setup is working!!!
It is working for all devices apart from an OLD Samsung Tab 2 failed the setup.
I have put this current challenge on this page as I think it could be the TLS SSL min protocols being part of the problem. But I don’t really want to tinker as I don’t know why you suggested these protocols. – Any suggestions as to what could be causing 1 old device to not work.
The device also doesn’t allow STARTTLS , so tried every option and none worked.
Also – feature request – PUSH messages, I would like to use this account for messages but the 15 mins or so i have to wait for IOS messages feels like an eternity . I have been searching and it appears you have to pay for Apple notification service? Feels bonkers!
Thank you!
I had to use this command to get past 404 errors with certbot
certbot certonly –agree-tos –expand –authenticator webroot –installer apache -d mail.domain.org –webroot-path /var/www/mail.domain.org/
Having a problem here. I’ve run the Postfix instructions in Part 2, but when I check systemctl status postfix it says postfix is “active (exited). Does this mean Postfix isn’t running? What have I done wrong?
This is normal, because the Postfix systemd service is a
oneshotservice. Postfix will run the master process after the main Postfix exits. If you run the following command, you can verify if Postfix master process if running.Output:
As you can see, the Postfix master process is listening on port 587, 465 and 25 on my mail server.
The dovecot systemd service is a
simpleservice, so you will see “active(running)” instead of “active(exited)”.That’s not what I get. I don’t see 587 or 465 listed when I run the above command. Any ideas?
Found the problem! I had missed an underline character in /etc/postfix/main.cf. Once I fixed that and reloaded Postfix, everything fell into place.
I have already postfix installed as a sendonly SMTP server using your other guide. I want to be able to also send from desktop client. Do I need to install dovecot to be able to communicate with Postfix? If so, are there other steps I can omit from this guide when I don’t need to receive email?
Why do you want to manually send emails from a desktop email client, but don’t want to receive reply email from the recipient?
The reply goes to another email server (Gmail). I can’t send mail from that server.
That’s not a good practice.
Hmm really? So my wordpress server is sending out emails. Sometimes I need to write a custom email.
Another server is taking care of incoming mail.
Do you mean that you send only postfix server guide shouldn’t be combined with an external mail server for incoming and other email?
I can also send mail from the other server, but not in this case (my colleague is in China, where gmail is blocked so can’t send out email).
Thanks.
I mean if you send an email from your own domain, but the reply email goes to a free third-party email service like gmail, that will trigger some spam filters. Why not receive reply emails on your own domain?
I do receive emails to my own domains. GSuite (gmail) is setup for incoming mail to mydomain.com. The wordpress server is not connected to Gsuite and sending with Postfix. I though from your-send only Postfix guide that this was a ok setup?
Ok. I understand now. Simply follow the instructions in this article and you will be able to use desktop email client. Note that
inet_interfacesshould be set toallin the/etc/postfix/main.cffile.Thanks, so you mean I do need dovecot even when I will not receive mail?
Mozilla Thunderbird, and also other mail clients I think, will not allow you to log into your mail server or send emails if there’s no IMAP/POP3 server running.
Ok, I see. I thought the separate settings in thunderbird etc for smtp server was connecting directly to postfix, but I guess that’s also dovecot than.
Hi Xiao, thank you for the awesome guide!
I keep to fail at the last step (configuring Thunderbird). It always shows error box that IMAP server doesn’t allow choosen authentication method.
I checked nmap for srv.kulibaba.site and it seems that all necessary ports are open.
Also dovecot is running fine:
● dovecot.service - Dovecot IMAP/POP3 email server Loaded: loaded (/lib/systemd/system/dovecot.service; enabled; vendor preset: enabled) Active: active (running) since Sun 2020-05-10 21:01:19 MSK; 1h 7min ago Docs: man:dovecot(1) http://wiki2.dovecot.org/ Process: 15947 ExecStop=/usr/bin/doveadm stop (code=exited, status=0/SUCCESS) Process: 16148 ExecReload=/usr/bin/doveadm reload (code=exited, status=0/SUCCESS) Process: 15986 ExecStart=/usr/sbin/dovecot (code=exited, status=0/SUCCESS) Main PID: 15990 (dovecot) CGroup: /system.slice/dovecot.service ├─15990 /usr/sbin/dovecot ├─15993 dovecot/anvil └─16151 dovecot/log May 10 21:41:47 srv.kulibaba.site dovecot[16151]: imap-login: Disconnected (no auth attempts in 0 s ecs): user=, rip=185.48.37.80, lip=194.58.119.56, TLS: SSL_read() failed: error:14094412:SSL rout ines:ssl3_read_bytes:sslv3 alert bad certificate: SSL alert number 42, session=In the log part you can see the error I get.
When I created let’s encrypt certificate for srv.kulibaba.site I also added –must-staple option, that’s probably the only thing I did “against” your guide…
I also tried to tweak Thunderbird changing general.useragent.compatMode.firefox to True, though it didn’t help. Neither choosing oAuth2 as auth method helped. My next concern is ssl = required in 10-ssl.conf, but at this point I decided to refer to the source, making this comment.
Btw, initially if my hostname and MX record is srv.kulibaba.site, was it right to create virtual nginx host and issue certificate using this name instead of “mail.kulibaba.site”?
Seems like I managed to resolve the issue by setting:
security.ssl.enable_ocsp_must_staple = false
in Thunderbird config editor
Postfix and Dovecot don’t support OCSP stapling. If you add
--must-stapleto your TLS certificate, then mail clients (Thunderbird) would refuse to connect. I didn’t test it, but other SMTP servers are probably not able to establish secure TLS connection with your Postfix SMTP server.So I recommend obtaining a new TLS certificate for your hostname (srv.kulibaba.site) without using
--must-staple.On ubuntu 20.04LTS “ssl_min_protocol = TLSv1.3” is not supported and we need to upgrade to at least dovecot 2.8
Can you help with ?
The latest stable version of Dovecot is 2.3.
Don’t be obsessed with using the latest cutting-edge TLS settings. That’s why you get TLS errors in your mail log. TLSv1.2 is secure enough.
Hi Xiao, at the beginning of the guide you wrote: “You need to have an Nginx virtual host for mail.your-domain.com before obtaining Let’s Encrypt TLS certificate”.
This is probably not true, I just need the certificate and see no reason in creating root folder and granting access to www-data. So I used certbot “certonly” option and configured nginx to make MX url forbidden (return 403). It seems to work fine. Do you see any problem with that?
Creating a virtual host is not a must if you have a default Nginx virtual host. There’s no problem with your method. However, you need to create a dedicated Nginx virtual host if you want to install Roundcube webmail later.
On Obtaining TLS Certificate with Nginx Web Server for ubuntu 20.04LTS I get the following error:
“AttributeError: module ‘acme.challenges’ has no attribute ‘TLSSNI01′”
Any clue on how to resolve this?
If you see the following error while trying to obtain TLS certificate on Ubuntu 20.04
You need to edit a config file.
Change
to:
Save and close the file. Then run the certbot command again to obtain TLS certificate.
Hello Xiao,
thank you for your very good tutorial. I successfully installed an email server using it. All good, but one point.
We have an ERP application which should send emails, but I cannot connect it to my email server. Not sure if I a missing some options of if I am inputing somethin wrong.
So I have:
outgoing mail server: mail.mydomain.com
port: 25
encryption: TLS
error: could not connect to SMTP host.
I tested with SMTP authentication (just took one created email address, not sure if I need another SMTP account..), I also tried without authentication.
Can you please give some insight?
Thank you!
You should use port 587.
Tahnk you.
Using port 587 I am a step closer. Same error if trying to connect to mail.domain.com but working if connecting to internal server IP.
Tested without SMTP auth (this is correct)?
New error on test email:
Mailer Error: Language string failed to load: tls The following From address failed: [email protected] Called Mail() without being connected
Can you please help with this error?
Thank you!
You should enable SMTP auth (enter an email address and password) on port 587.
really very nice and awesome tut! thanks for ur work
im trying to install mailserver for only local use, i have my own local dns server (bind9) and have mx record and stuff for my mail server, obv i cant use Let’s Encrypt, so im using openssl instead, followed to this part, i think everything’s fine
i can login using thunderbird in my laptop fine, it auto detect my settings, i try to send test email to myself (or another local account), i see the mail in sent folders but i receive nothing in inbox.
i see this in the /var/log/mail.log
i dont know where im going wrong, help is much appreciated!
thanks!
for some reasons i see the reply is posted “4 seconds ago” and it been days lol
anyway, solved my problem thanks!
Hi, thanks for the great tutorial!
What if Postfix and dovecot are running on separate servers like smtp.example.com and imap.example.com? How to configure LMTP?
Edit the Dovecot 10-master.conf file.
When Postfix and Dovecot are running on separte servers, you need to make LMTP service listen on TCP socket. Change the lmtp service definition to the following.
service lmtp { unix_listener /var/spool/postfix/private/dovecot-lmtp { mode = 0600 user = postfix group = postfix } inet_listener lmtp { address = 10.10.10.2 port = 2424 } }LMTP should be used in a local LAN and not be visible to the Internet, so you should use a private IP address for the
inet_listener. Replace 10.10.10.2 with your own private IP address. If your SMTP server and IMAP server are not in the same LAN, you can use wireguard to create a virtual private network.Save and close the file. Then restart Dovecot.
Next, edit the Postfix main configuration file on the other server.
Add the following lines at the end of the file. The first line tells Postfix to deliver emails to local message store via the dovecot LMTP server listening on 10.10.10.2:2424. The second line disables SMTPUTF8 in Postfix, because Dovecot-LMTP doesn’t support this email extension.
Save and close the file. restart Postfix.
outbox/drafts etc not creating automatically:
When i set the 15-mailboxes.conf to create boxes automatically, then create a user with “sudo adduser user1” and then add it to thunder bird thunderbird only contains the inbox and nothing else (which confuses it when it tries to save sent mails to outbox etc)
“`
mailbox Junk {
auto = create
special_use = \Junk
}
mailbox Trash {
auto = create
special_use = \Trash
}
# For \Sent mailboxes there are two widely used names. We’ll mark both of
# them as \Sent. User typically deletes one of them if duplicates are created.
mailbox Sent {
auto = create
special_use = \Sent
}
mailbox “Sent Messages” {
special_use = \Sent
}
“`
The “Sent” folder will be automatically created when you send the first email. The “Trash” folder will be automatically created when you delete an email, etc.
Huge thanks for creating and maintaining this guide!
Everything is working happily for me… except the Microsoft Mail App (on Windows 10) which, no mater what I’ve tried, proclaims “Untrusted certificate”.
The cert is configured in /etc/dovecot/conf.d/10-ssl.conf
Another client I’ve tried (GMail on Android) doesn’t complain about the cert.
I’ve configured the MS Mail App to use mail. names for the incoming and outgoing servers and used the suggested ports of 143 and 587 (which default to imap.:993 for incoming and smtpauths.:25 for outgoing)
I almost wonder if despite the settings it’s still expecting to see imap. and smtpauths. listed in the cert or some other stupidity… it really gives me no detailed error information to go on.
I’ve sworn at it repeatedly and cursed windows 10 many times
I can ignore the “untrusted certificate” warning and everything appears happy – of course then once the cert gets renewed the windows mail app just silently stops syncing because the force-accepted cert no longer matches the retrieved cert and i have to remove the account(s), re-add them, and ignore the untrusted cert issue again because MS.
At this point I don’t think the problem is on the linux postfix/dovecot side, HOWEVER, I did experience my gmail client silently stop syncing too – until today when i was fiddling with my linux configs again when the gmail app suddenly started syncing my mail again.
If I can’t get this figured out I guess I’ll have to setup a daily cron to flick an email at me as a canary and go through the remove/re-add account process when the daily mails stop due to the cert being refreshed… I’d really like to solve this problem correctly though and have confidence that I’m not missing important mails.
Thanks again! Sorry for getting long winded here.
Thank you so very much!
This is by far the most helpful tutorial about anything that I have ever read, for so many reasons.
Cheers!
Hey! Great article. I have one doubt. I have a client send me a mail on port 25(which I cannot change). After following the first part, the client was able to send the mail on 25 and I was able to receive it.
After the 2nd part postfix was not listening to port 25.
I found out that `smtp inet n – y – 1 postscreen` line was commented in master.cf. I uncommented it and now I see it listening to port 25, but when the client tried to send a mail, he get’s no response and the request is just pending. Any idea what could be missing?
If you want to enable Postscreen, please read this article: Enable and Configure Postscreen in Postfix to Block Spambots
If you cat the /etc/postfix/master.cf file and paste it here, I might be able to troubleshoot your problem.
Also check your mail log file (/var/log/mail.log), it might give you some clues.
Where does postfix (or dovecot) even store these emails please?
If you are using virtual mailbox (PostfixAdmin), the emails are stored in
/var/vmail/yourdomain.com/username.If you are not using virtual mailbox, the emails are stored under
~/Maildir(The Maildir subdirectory under each user’s home directory.)Much appreciated
im not using virtual mailbox. Is it “/root/Maildir/new”? “/root/Maildir” has no other loose files and its other subdirectories ae empty. Anyway if it is “/root/Maildir/new” I see there are files in there but nothing after the 13 (this month) but i have sent many emails why is this? how is this even working?
oh i see its in
/home/plefort/Maildir
One more question. When i add my custom email account to gmail it doesnt save my sent emails to the sent folder. any thoughts?
is it because its using pop conventions, and so doesnt care about server storage, and so wont save anything to the server?
I’m not sure what you mean by “add my custom email account to gmail”.
Hello,
First, thank you for the detailed tutorial on setting up an email server with Ubuntu!
I’ve also followed the RoundCube tutorial (And the Postfix tutorial)from you and setup everything properly, but there seems to be an obstacle that prevents me from using Roundcube.
Logging in to Roundcube works perfectly fine, but sending and receiving emails cannot be done.
When using my email to test the server, I get a “Mail Undeliverable” message with the following error:
So the mail server cannot receive email.
Sending email using the Roundcube does nothing. After I compose a test email and click send, Roundcube would keep loading with no progress until I get an error that says “Request timed out”
What can I do to resolve this? Any leads would be appreciated, thank you!
Looks like some information was omitted for some reason, here is the actual error message I get from trying to send an email to my mail server:
Okay so now I can receive emails in the server. There is a minor change that I need to do in
I had to modify this line to include %Ln
This fixed the issue of not being able to receive emails in the mail server. But the problem of sending emails still persists. The Roundcube just loads indefinitely until the request timed out.
If you encounter errors with Roundcube, you can check the error logs at
/var/log/apache2/roundcube_error.log(if you are using Apache), or/var/log/nginx/roundcube.error(if you are using Nginx.)Thank you for this guide! It’s been very thorough and helpful
Nevermind, the issue has been resolved. I checked /var/log/mail.log and found out where the issue is. There was a typo (my bad lol) in master.cf file. After I fixed that one typo, and restarted the service, Roundcube can send and receive emails without problem.
Hi, Xiao. Thank you for helpful tutorials so much!! And I can’t send & recieve mail until this stage. mail.log says
mail postfix/lmtp[3305]:: to=, relay=mail.example.com[private/dovecot-lmtp], delay=0.14, delays=0.09/0.01/0.02/0.02, dsn=5.1.1, status=bounced (host mail.example.com[private/dovecot-lmtp] said: 550 5.1.1 User doesn’t exist: [email protected] (in reply to RCPT TO command))
Any ideas? thanks
Perhaps your email address is in lower case, but you used upper case when you send the email. You can edit the
/etc/dovecot/conf.d/10-auth.conffile and change the auth_username_format toSo dovecot would lowercase the username. Restart Dovecot.
Hello there,
After installing Dovecot on ubuntu 20.04LTS i found out that dovecot 2.3.7.2 does not work with SSL1.3. So I need to update Dovecot to at least the version 2.3.8 or to the stable version 2.4
Can you help with?
The latest stable version of Dovecot is 2.3.
Don’t be obsessed with using the latest cutting-edge TLS settings. That’s why you get TLS errors in your mail log. TLSv1.2 is secure enough.
I concur this is an AMAZING write-up, thank you. I have several gsuite accounts and am trying to migrate one over to my local MX. Like a few others, I’ve completed the setup, triple checked your instructions, confirmed that there are no postfix or dovecot errors, yet can only send messages, but not receive any. Now, if I send a message from the domain I migrated, [email protected] to [email protected] it appears in my inbox. If I send from [email protected] to [email protected] – it also WORKS, but if I send from [email protected] to [email protected] the message never arrives in my Inbox. (18.04, Dovecot v. 2.3.10.1)
Thank you.
If there are no errors in mail log (/var/log/mail.log) after sending emails from gmail to your domain address. It could be:
1.) Your MX record is wrong, or the MX hostname doesn’t have an IP address.
2.) Port 25 (inbound) is closed.
Awesome. Port 25 was the issue; I’m 100%. I appreciate the article and the prompt response.
Hello there,
my mail log have a lot of this
SSL_accept error from st43p00im-ztfb10063301.me.com[17.58.63.179]: -1
Jul 7 16:44:01 www postfix/smtpd[66273]: warning: TLS library problem: error:14209102:SSL routines:tls_early_post_process_client_hello:unsupported protocol:../ssl/statem/statem_srvr.c:1685
What can be this? On their side or on my side?
Thank You
Don’t be obsessed with using the latest cutting-edge TLS settings. That’s why you get TLS errors in your mail log.
One other thing, I saw this message in mail.log:
‘mail dovecot: config: Warning: please set ssl_dh= /etc/dovecot/dh.pem’
After executing the suggested command, I didn’t see that message again…
HTH and thanks for your work on this how-to 🙂
Last suggestion: I always found it complicated and error-prone to get a Letsencrypt certificate via the method you recommend (which is the method commonly adopted in how-to’s on the Web). Instead, I prefer to stop the Web server and use the following command, which works without hassle every time:
certbot certonly –standalone –preferred-challenges http -d example.com -d www.example.com
(obviously, you have to replace ‘example.com’ with your own domain.) Then I respond to the prompts for a mail address and permission to be contacted by EFF and restart the Web server. I prefer to do certificate renewals in the same way…
You have to stop your web server again when you renew TLS certificate. (every 90 days)
If it’s not working, you have done something wrong. If you paste the error message when obtaining TLS certificate, perhaps I can help.
I have my certificates, and they’re working fine… I think you missed the point of what I was saying… 😉
Personally, I find that ‘certbot certonly –standalone’ with the Web server temporarily shut down is a lot less hassle than being obliged to set up the vhosts first and satisfy all the constraints of using the nginx/apache2 plugins…
after running sudo netstat -lntp | dovecot I am getting the following error message:
doveconf: Fatal: Error in configuration file /etc/dovecot/conf.d/10-ssl.conf line 14: ssl_cert: Can’t open file /etc/letsencrypt/live/mail.lobap.ca/fullchain.pem: Permission denied
Any suggestion on how to fix it, please.
The correct command is
Hi, hope to save me. Everything is perfect until this command UbuntuServer 20.04.
“sudo add-apt-repository ppa:certbot/certbot”
E: The repository ‘http://ppa.launchpad.net/certbot/certbot/ubuntu focal Release’ does not have a Release file.
N: Updating from such a repository can’t be done securely, and is therefore disabled by default.
N: See apt-secure(8) manpage for repository creation and user configuration details.
I can´t install TLS Certificate. the port 443 does not open “attach picture”
I opened the ports by firewall UFW and I call my isp and all port are open. can you help me?
Certbot doesn’t have a PPA for Ubuntu 20.04. Remove it with:
Install certbot from the default software repository.
Hello Guo an,
When I send an email to my gmail account, there is a red lock on gmail which means that my email is not encrypted. However, my TLS letsencrypt connection is working so I don’t know what the problem is. How do I get rid of the red lock?
Maybe you forgot to add the following lines in /etc/postfix/main.cf file?
smtp_tls_security_level = may smtp_tls_loglevel = 1 smtp_tls_session_cache_database = btree:${data_directory}/smtp_scacheFound the problem!
It turns out that my postfix had enabled a PIX workaround “disable esmtp” which for some reason downgraded the connection to a HELO connection to Google.
I had the following line in my mail.log file:
This problem was fixed when I added the following line in my main.cf file:
Absolutely great guide. Life-saver!
When I try this step:
I got error message like attach file, can you help me Xiao?
Add DNS A record for email.vanhussen.net
I’m getting the same error, even though I have created an A record in my dns
Can’t find the A record of your hostname on dnsmap.io: https://dnsmap.io/#A/mail.nerdcomputers.net
Ask you domain registrar to find out why the A record doesn’t propagate to the Internet.
My Ubuntu 20.04 did not allow incoming traffic, while I explicitly have given ufw allow 25
In postfix main.cf file, I changed inet_interfaces from 127.0.0.1 to 0.0.0.0
If I understand well, the postfix installation that preexisted on my rented server was looking only at localserver for email. Probably kind of a countermeasure to prevent newly installed servers from accepting-relaying smap if postfix is not properly configured…
Robert
Edit /etc/postfix/main.cf file and change the value of
inet_interfacestoall.Then restart Postfix.
Thanks ! This is indeed what I tried and it cured the issue.
Robert
I keep getting the following error when trying to obtain a TLS certificate. I definitely have an A record on my godaddy domain page that leads to the server IP address. Is there anything else that could be causing this?
I can’t find the A record for mail.josephngechu.online. https://dnsmap.io/#A/mail.josephngechu.online
Hello,
Great guide. I’m getting this error when installing the certbot certificate:
It didn’t show up on dnsmap.io so i contacted namecheap and they told me (for the A and AAAA records) to get rid of the domain in the host field so to only have it as “mail”. It showed up on dnsmap.io but then i got this error:
Your help fixing this would be much appreciated.
Can’t find your A or AAAA record on dnsmap.io.
Sorry i left it with the broken records to see the error message. It now gives me this error message when i run the certbot certificate. I checked the IPv4 and v6 I entered and they’re correct.
Domain: mail.lunitacrafts.com
Type: unauthorized
Detail: Invalid response from
http://mail.lunitacrafts.com/.well-known/acme-challenge/MNUHdMy9MMeKL8fe5KOEecoCDaLkUFDJMV_lESlhckc
[2607:5501:3000:1141::2]: “\n\n
Not Found
\n<p"
To fix these errors, please make sure that your domain name was
entered correctly and the DNS A/AAAA record(s) for that domain
contain(s) the right IP address.
It seems a firewall is blocking http/https requests to your mail server.
You need to open the following TCP ports on your mail server.
Hello. I am having issues with getting incoming mail working. I keep getting the error below when a mail server tries to connect to me:
The file definitely exists with what look like the correct permissions:
And here is my config excerpt from dovecot’s 10-master.conf:
service auth { # Postfix smtp-auth unix_listener /var/spool/postfix/private/auth { mode = 0660 user = postfix group = postfix } }I am at a loss to what the problem could be. I am using Ubuntu 20.04 LTS.
It looks like you changed the
submissionservice in the/etc/postfix/master.cffile.Also, you can check if Dovecot is running.
If it’s not running, check the journal to find out why it’s not running.
The /var/log/mail.log file might also tell you why Dovecot failed.
Besides configuring dovecot’s mailbox, postfix also needs to be configured; which is missing in this tutorial:
sudo postconf -e “home_mailbox = Maildir/”
Unless you didn’t configure LMTP as told in this article.
The
home_mailboxparameter is used by Postifx’slocaldelivery agent. After configuring LMTP, Postfix will not use its ownlocaldelivery agent, but pass incoming emails to Dovecot via LMTP protocol, which is effected by the following setting. Postfix doesn’t care which mailbox format you are going to use.Yes, thanks for the hint. I did miss the service lmtp configuration part. Thus, I ultimately ran into another issue, I just was able to solve. (dovecot-lmtp: No such file or directory) Thanks for the lesson! Your tutorial is great and our Email-SRV is up and running flawlessly. (A bit slow, but at least it works for now)
Hi Xiao,
I attempted to redo the setup from the start and I’m now stuck – after configuring thunderbird and trying to send an email – I’m getting the following error :
I’m assuming it is listening on port 587:
Your submission service on port 587 advertises STARTTLS. Always check the mail log (/var/log/mail.log) when something went wrong.
I’m getting some errors on the RSA keys, from the priv.key – i’ve checked that the file exists. I’m not sure how to interpret this –
It seems you didn’t correctly enter the path for your TLS private key in
/etc/postfix/main.cffile. The path is not complete.yes, you’re correct there was an error with the path. I had a typo on privkey.pem
Thanks you for the excellent guide!
I’ve been successful with creating the relay according to your relevant guide (sent confirmed it using the “mail [email protected]”). I’ve also been successful in connecting via IMAP from a mail client (Mac Mail client).
However, when trying to use the SMTP via Mac Mail client, I’m unsuccessful. Why could this be?
Thank you so much, and please accept my small donation 🙂
Here are a failed log (from Mail client) and a success log (from mail “[email protected]” command):
It seems your Mac mail client is trying to connect to port 25 of the mail server when sending emails. You should configure the mail client to connect to port 587 or 465.
Thanks for the reply! Why shouldn’t the mail client connect with my server on port 25 (incoming)? If I understood you correctly, the client can connect with my server on 25, and my server will communicate with the world via relay (which it seems like it does successfully from the fact that “mail …” worked.
Port 25 is usually used for MTA to MTA communication. MTA stands for Mail Transfer Agent, aka SMTP server.
Your mail client is MUA (Mail User Agent). Port 587 and 465 are used for MUA to MTA communication.
Most residential ISPs block port 25. It doesn’t make sense for mail clients to use port 25 to submit outgoing emails.
Thanks. Understood. Interesting then that that was the default for the Mail client.
Switched to 587, and it worked!
Thanks 🙂
Hi Xiao,
First of all,thank you for sharing the experience in seting up a mail server.
I have through the Part 2 and followed every step to setup a mail server,while I test the server,the test account ([email protected],ubuntu is my Linux user)can not receive any email from any server,but can send a mail.The error messages are bellow(as the attachment):
"The mail system : host mail.xxx.com[private/dovecot-lmtp] said: 550 5.1.1 User doesn't exist: [email protected] (in reply to RCPT TO command)"And the mail.log snippet:
The status of Dovecot:
" dovecot.service - Dovecot IMAP/POP3 email server Loaded: loaded (/lib/systemd/system/dovecot.service; enabled; vendor preset: enabled) Active: active (running) since Tue 2020-09-29 08:46:18 CST; 20min ago Docs: man:dovecot(1) http://wiki2.dovecot.org/ Main PID: 1193 (dovecot) Tasks: 7 (limit: 4915) CGroup: /system.slice/dovecot.service ├─1193 /usr/sbin/dovecot -F ├─1329 dovecot/anvil ├─1331 dovecot/log ├─1335 dovecot/config ├─3177 dovecot/imap-login ├─3179 dovecot/ssl-params └─3184 dovecot/imap Sep 29 08:46:18 VM-0-5-ubuntu systemd[1]: Started Dovecot IMAP/POP3 email server. Sep 29 08:46:18 VM-0-5-ubuntu dovecot[1193]: master: Dovecot v2.2.33.2 (d6601f4ec) starting up for imap, pop3, lmtp, imap, lmtp, pop3 (core dumps disabled) Sep 29 08:47:06 VM-0-5-ubuntu dovecot[1331]: imap-login: Disconnected (no auth attempts in 13 secs): user=, rip=83.97.20.25, lip=172.17.0.5, session= Sep 29 08:48:51 VM-0-5-ubuntu dovecot[1331]: lmtp(2305): Connect from local Sep 29 08:48:51 VM-0-5-ubuntu dovecot[1331]: lmtp(2305): Disconnect from local: Successful quit Sep 29 08:51:05 VM-0-5-ubuntu dovecot[1331]: pop3-login: Disconnected (no auth attempts in 11 secs): user=, rip=83.97.20.25, lip=172.17.0.5, TLS: Disconnected, session= Sep 29 08:54:13 VM-0-5-ubuntu dovecot[1331]: imap-login: Login: user=, method=PLAIN, rip=113.87.92.134, lip=172.17.0.5, mpid=3184, TLS, session= Sep 29 08:54:22 VM-0-5-ubuntu dovecot[1331]: imap-login: Disconnected (no auth attempts in 11 secs): user=, rip=83.97.20.25, lip=172.17.0.5, TLS: Disconnected, session= "I have try to set the /etc/dovecot/conf.d/10-auth.conf file and change the auth_username_format to
auth_username_format = %Ln
but it’s still not work !
Could you help me to fix the issues?
Thanks a lot!
Run the following command to list all available mailboxes on your server.
I already set up Apache server using cloudflare origin certificate. do I still need another certificate for email? or Can I point to the same SSL cert i am using in Apache2 conf?
If your mail server hostname is
mail.example.comand your current certificate coversmail.example.com, then you can use the current certificate.Hello. Thank you for the tutorials, I am learning a lot and its nice to have solid independant resources to learn from.
I have ran into a problem that I can not find a solution for. I will try to get help at #dovecot, but perhaps it’s something to bring up here as well. I successfully installed postfix and dovecot, and got connected through thunderbid and again on spark through my iphone. I successfuly add postfixadmin and did not retest the email. I moved on to trying to install roundcube and got to the config test and failed. Upon trying to relog into thunderbird and spark I was unable to login. Then I noticed I was unable to send email from the command line using postfix. I worked for awhile trying to find a solution and decided to start over.
Eventually I decided to purge everything and try again, once I did postfix worked again in the command line, so I tried to jump ahead and test roundcube. Postfix went down again. I am back to a point where I can send from the terminal in postfix, and it appears dovecot is running correctly, but I am unable to login in from thunderbird and spark still. I ran journalctl -eu dovecot and the only oddity that I found is this…
dovecot[10422]: auth: passwd-file(*user*,*clientip*,): unknown user
*user* being my user name without the domain and *clientip* being my home ip address, as I am logged in through ssh.
Any thoughts would be greatly appreciated, thanks.
Run the following command to list all mailbox users on your server.
It seems you changed the
userdbsettings in the/etc/dovecot/conf.d/auth-system.conf.extfile.This displayed my account in the vmail system, which is correctly configued. I had made no changes to the userdb setting in /etc/dovecot/conf.d/auth-system.conf.ext., the only variable uncommented is driver = passwd. I realize now that this issue belongs in a thread on part 3, so I will move it over there.
Something much larger is going on here and I have spent many hours pouring over this to understand it and express it just in case anyone else comes across my issues so they don’t have to waste their time. The problem has too many oddities for it to be a simple error in syntax, or missed variable… etc. I have poured over the first 3 tutorials top to bottom and front to back, I am pretty certain I have everything correctly.
When I configure the SMTP server on thunderbird I can use the server properly (port 587 with standard TLS OR 465 SSL) but in both cases when I send an e-mail to my gmail account, the e-mail is not encrypted (red lock icon). I believe it is because of the following:
Can you help me?
I should maybe have mentioned: 1. Thank you so much for the tutorial!!! 2. both SPF and DKIM pass when I send e-mails (from part 4 of the tutorial)
AND, as from the other comments, the following params are set:
My bad, I was missing the following in my /etc/postfix/main.cf:
I’m sorry for cluttering the comment section and again, grateful for the tutorial!!
Just try this command to copy /etc/securetty
sudo cp /usr/share/doc/util-linux/examples/securetty /etc/securetty
How to migrate from mbox to maildir
If you previously use mbox mail format, now you want to migrate to maildir format, here’s how.
Edit
/etc/dovecot/conf.d/10-mail.conffile.Go to the
namespace inbox {}section, find the following line.Uncomment this line and specify separator for the inbox namespace.
Then set
Save and close the file. Restart Dovecot for the changes to take effect.
Stop Postfix so there won’t be any new emails coming in.
Then run the following command to convert mbox to maildir for a user. (Sometimes I found I need to manually type the command. If I copy and paste it in the terminal, sometimes it won’t won’t. I don’t know why.)
If you have created folder in your mailbox, they will be converted as well and stored as hidden files under
~/Maildir.If you have followed part 3 to set up virtual mailbox, then you need to sync the Maildir for the virtual users. For example,
Then change the ownership to vmail user.
Now reload the webmail. If some folders don’t show anymore, don’t worry, they are still there. You just need to re-enable them in Roundcube webmail settings.
if you see this error this error
● dovecot.service – Dovecot IMAP/POP3 email server
Loaded: loaded (/lib/systemd/system/dovecot.service; enabled; vendor preset: enabled)
Active: failed (Result: exit-code) since Wed 2020-11-11 14:33:44 UTC; 6s ago
Docs: man:dovecot(1)
http://wiki2.dovecot.org/
Process: 13110 ExecStop=/usr/bin/doveadm stop (code=exited, status=0/SUCCESS)
Process: 22093 ExecStart=/usr/sbin/dovecot -F (code=exited, status=89)
Main PID: 22093 (code=exited, status=89)
Nov 11 14:33:44 mail.deeglowempire.com systemd[1]: Started Dovecot IMAP/POP3 email server.
Nov 11 14:33:44 mail.deeglowempire.com dovecot[22093]: doveconf: Fatal: Error in configuration file /etc/dovecot/conf.d/10-ssl.conf line 54: Unknown setting: ssl_min_protocol = TLSv1.2
Nov 11 14:33:44 mail.deeglowempire.com systemd[1]: dovecot.service: Main process exited, code=exited, status=89/n/a
Nov 11 14:33:44 mail.deeglowempire.com systemd[1]: dovecot.service: Failed with result ‘exit-code’.
OPEN /etc/dovecot/conf.d/10-ssl.conf
PLEASE COMMENT OUT THIS LINE
#ssl_min_protocol = TLSv1.2
Hi, I noticed that to connect my email account to Thunderbird I have to disable Cloudflare option for my domain. Do you know what can cause such a problem ? When trying to set up an email account in Thunderbird with Cloudflare enabled, the program does not detect the server settings…
You should not enable the CDN (proxy) feature when creating DNS A record and AAAA record for the hostname of your mail server. Cloudflare doesn’t support SMTP or IMAP proxy 🙂
Hi Xiao,
Thank you for the tutorials. I fallowed everything and the server is running but when I try to send mail it is not delivered, on the log is written:
Port 25 (outbound) is blocked.
https://www.linuxbabe.com/mail-server/setup-basic-postfix-mail-sever-ubuntu#port-25-outbound
Thank you very match Xiao. I spoke with my ISP and port 25 was open, but they were put connection restrictions on it. After they remove it, everything works. Thank you very match again!
Hi Xiao,
thank you very much for the comprehensive tutorial! Basically everything works and I can send and receive mails. However postfix keeps randomly shutting down. Sometimes when I try to send an email and sometimes just by itself. Do you have any clue why such a thing occurrs?
You can open the
/var/log/syslogfile to see if you can find any clue. Search for the word “kill” in this file.For example,
This indicates the server ran out of memory, so it killed the
mysqldprocess.Thanks for the response. Actually it was the monit process that was killing it. I don’t know how it was configured but disabling fixed the problem
Hello Xiao, Love your tutorials. I’ve followed parts 1 and 2 for setting up postfix and dovecote on ubuntu 20.04 and able to connect and log into imaps, but cannot get ports 465 and 587 to listen. The result from netstat is:
and submission and smtps as in your instructions are followed in postfix master.cf
and dovecot.conf unix listener
service lmtp { unix_listener /var/spool/postfix/private/dovecot-lmtp { mode = 0600 user = postfix group = postfix } }Been over this for the past 2 weeks looking for errors in the logs and not information reported in mail.log and dovecote.log. You help will be very much a time saver.
Stop Postfix.
Do a health check.
Run it in the foreground.
The output might give you some clues.
Xiao,
from sudo postfix check
checked the makedefs.out
# Do not edit -- this file documents how Postfix was built for your machine. #---------------------------------------------------------------- # Start of summary of user-configurable 'make makefiles' options. # CCARGS=-g -O2 -fdebug-prefix-map=/build/postfix-q6EyY5/postfix-3.4.13=. -fstack-protector-strong -Wformat -Werror=format-security -DDEBIAN -DHAS_PCRE -DHAS_LDAP -DUSE_LDAP_SASL -DHAS_SQLITE -DMYORIGIN_FROM_FILE -DHAS_CDB -DHAS_LMDB -DHAS_MYSQL -I/usr/include/mysql -DHAS_PGSQL -I/usr/include/postgresql -DHAS_SQLITE -I/usr/include -DHAS_SSL -I/usr/include/openssl -DUSE_SASL_AUTH -I/usr/include/sasl -DUSE_CYRUS_SASL -DUSE_TLS # AUXLIBS=-lssl -lcrypto -lsasl2 -lpthread -Wl,-Bsymbolic-functions -Wl,-z,relro -Wl,-z,now -L/build/postfix-q6EyY5/postfix-3.4.13/debian # AUXLIBS_CDB=-lcdb -L../../lib -L. -lpostfix-util # AUXLIBS_LMDB=-llmdb -L../../lib -L. -lpostfix-util # AUXLIBS_MYSQL=-lmysqlclient -L../../lib -L. -lpostfix-util -lpostfix-global # AUXLIBS_LDAP=-lldap -llber -L../../lib -L. -lpostfix-util -lpostfix-global # AUXLIBS_PCRE=-lpcre -L../../lib -L. -lpostfix-util # AUXLIBS_SQLITE=-lsqlite3 -L../../lib -L. -lpostfix-util -lpostfix-global -lpthread # AUXLIBS_PGSQL=-lpq -L../../lib -L. -lpostfix-util -lpostfix-global # shared=yes # dynamicmaps=yes # pie=yes # daemon_directory=/usr/lib/postfix/sbin # html_directory=/usr/share/doc/postfix/html # manpage_directory=/usr/share/man # readme_directory=/usr/share/doc/postfix # End of summary of user-configurable 'make makefiles' options. #-------------------------------------------------------------- # System-dependent settings and compiler/linker overrides. SYSTYPE = LINUX4 _AR = ar ARFL = rv _RANLIB = ranlib SYSLIBS = -pie -z relro -z now -lssl -lcrypto -lsasl2 -lpthread -Wl,-Bsymbolic-functions -Wl,-z,relro -Wl,-z,now -L/build/postfix-q6EyY5/postfix-3.4.13/debian -ldb -lnsl -lresolv -ldl -licui18n -licuuc -licudata AUXLIBS_CDB = -lcdb -L../../lib -L. -lpostfix-util AUXLIBS_LDAP = -lldap -llber -L../../lib -L. -lpostfix-util -lpostfix-global AUXLIBS_LMDB = -llmdb -L../../lib -L. -lpostfix-util AUXLIBS_MYSQL = -lmysqlclient -L../../lib -L. -lpostfix-util -lpostfix-global AUXLIBS_PCRE = -lpcre -L../../lib -L. -lpostfix-util AUXLIBS_PGSQL = -lpq -L../../lib -L. -lpostfix-util -lpostfix-global AUXLIBS_SQLITE = -lsqlite3 -L../../lib -L. -lpostfix-util -lpostfix-global -lpthread CC = gcc -fPIC -I. -I../../include -g -O2 -fdebug-prefix-map=/build/postfix-q6EyY5/postfix-3.4.13=. -fstack-protector-strong -Wformat -Werror=format-security -DDEBIAN -DHAS_PCRE -DHAS_LDAP -DUSE_LDAP_SASL -DHAS_SQLITE -DMYORIGIN_FROM_FILE -DHAS_CDB -DHAS_LMDB -DHAS_MYSQL -I/usr/include/mysql -DHAS_PGSQL -I/usr/include/postgresql -DHAS_SQLITE -I/usr/include -DHAS_SSL -I/usr/include/openssl -DUSE_SASL_AUTH -I/usr/include/sasl -DUSE_CYRUS_SASL -DUSE_TLS -DHAS_DEV_URANDOM -DDEF_DAEMON_DIR=\"/usr/lib/postfix/sbin\" -DDEF_HTML_DIR=\"/usr/share/doc/postfix/html\" -DDEF_MANPAGE_DIR=\"/usr/share/man\" -DDEF_README_DIR=\"/usr/share/doc/postfix\" -DUSE_DYNAMIC_LIBS -DUSE_DYNAMIC_MAPS $(WARN) OPT = -O2 DEBUG = -g AWK = awk STRCASE = EXPORT = CCARGS='-I. -I../../include -g -O2 -fdebug-prefix-map=/build/postfix-q6EyY5/postfix-3.4.13=. -fstack-protector-strong -Wformat -Werror=format-security -DDEBIAN -DHAS_PCRE -DHAS_LDAP -DUSE_LDAP_SASL -DHAS_SQLITE -DMYORIGIN_FROM_FILE -DHAS_CDB -DHAS_LMDB -DHAS_MYSQL -I/usr/include/mysql -DHAS_PGSQL -I/usr/include/postgresql -DHAS_SQLITE -I/usr/include -DHAS_SSL -I/usr/include/openssl -DUSE_SASL_AUTH -I/usr/include/sasl -DUSE_CYRUS_SASL -DUSE_TLS -DHAS_DEV_URANDOM -DDEF_DAEMON_DIR=\"/usr/lib/postfix/sbin\" -DDEF_HTML_DIR=\"/usr/share/doc/postfix/html\" -DDEF_MANPAGE_DIR=\"/usr/share/man\" -DDEF_README_DIR=\"/usr/share/doc/postfix\" -DUSE_DYNAMIC_LIBS -DUSE_DYNAMIC_MAPS' OPT='-O2' DEBUG='-g' WARN = -Wall -Wno-comment -Wformat -Wimplicit -Wmissing-prototypes \ -Wparentheses -Wstrict-prototypes -Wswitch -Wuninitialized \ -Wunused -Wno-missing-braces -fcommon DEFINED_MAP_TYPES = pcre ldap sqlite cdb lmdb mysql pgsql ssl dev_urandom MAKE_FIX = # Switch between Postfix static and dynamically-linked libraries. AR = : RANLIB = : LIB_PREFIX = postfix- LIB_SUFFIX = .so SHLIB_CFLAGS = -fPIC SHLIB_DIR = /usr/lib/postfix SHLIB_ENV = LD_LIBRARY_PATH=/build/postfix-q6EyY5/postfix-3.4.13/lib SHLIB_LD = gcc -shared -Wl,-soname,${LIB} SHLIB_SYSLIBS = -lssl -lcrypto -lsasl2 -lpthread -Wl,-Bsymbolic-functions -Wl,-z,relro -Wl,-z,now -L/build/postfix-q6EyY5/postfix-3.4.13/debian -ldb -lnsl -lresolv -ldl -licui18n -licuuc -licudata SHLIB_RPATH = -Wl,--enable-new-dtags -Wl,-rpath,${SHLIB_DIR} # Switch between dynamicmaps.cf plugins and hard-linked databases. NON_PLUGIN_MAP_OBJ = PLUGIN_MAP_OBJ = $(MAP_OBJ) PLUGIN_MAP_OBJ_UPDATE = plugin_map_obj_update PLUGIN_MAP_SO_MAKE = plugin_map_so_make PLUGIN_MAP_SO_UPDATE = plugin_map_so_update PLUGIN_LD = gcc -shared POSTFIX_INSTALL_OPTS = # Application-specific rules.Could it be a permissions issue?
Xiao,
Problem solved. The file /etc/postfix/postfix-files was not created on the install (there was a directory instead named postfix-files.d). Created file by touch postfix-files and presto magic, ports 465 and 587 appeared. Thanks for your time.
Hi Xiao, always got the error when I try to send mail:
But when I restart my postfix:
I can send my email.
But after that, I get the error again “Unable to send email to [email protected]!”
This is my mail.log:
Can you help me? THANK YOU!
I don’t know why, but some folks have problems after installing Monit. Try disabling Monit.
I have try this sir:
But stil got the error, but when I try remove monit.
Now I can send message anytime.
Here is what monit log kept sending after restarting postfix:
perhaps this is of any help Xiao?
Hello, I get an error when I’m trying to run the following command:
sudo doveadm user ‘*’
RESULT:
Error: auth-master: userdb list: User listing returned failure
Fatal: user listing failed
Any idea of what can I do to fix it?
Regards,
Can you check the /var/log/mail.log file to see if there are any errors in the log?
Hello
as I tried to log in in thunderbird, I had dovecot log like user=
I created a unix user and dovecot doesn’t sees it,
thunderbird says cant login wrong pass or username
Maybe you should reboot your server?
hello Xiao, thanks for quick answer
I restarted dovecot many times, dovecot lists mailusers only [email protected]
I created unix user info, it doesn’t list it
thunderbird says cant login to smtp server wrong user or pass
If you followed part 3, then you can no longer use Unix accounts as email addresses. You must create virtual users in PostfixAdmin.
I didn’t follow part 3 since I’m afraid it removes mysql db
I just wish one single mail user, it’s enough with single unix user
but can’t login, and mail.log doesn’t write anything about dovecot attempts, or last one was like user=<>
Then you probably have followed tutorials on other websites. Don’t mix up mail server tutorials from different websites.
If you don’t know where’s wrong, you can add the following line in the /etc/dovecot/dovecot.conf file,
then restart dovecot, so dovecot will produce debugging message in the /var/log/mail.log file.
ok, I can now login as I rebuilt it all
now gmail says as I try to send to gmail address
Make sure you have set PTR record for the IP address of your mail server. And follow part 4 to set up SFP and DKIM.
Hello,
why incoming mails from google for example are removed automatically?
log writes message delivered, but then log writes “removed”
It’s removed from the Postfix mail queue, not removed from the message store (Inbox).
Hello Xiao,
Thank you for the guide 🙂
I am stuck with Roundcube setup.
Can’t login:
Remote login error:
IMAP connect: NOT OK(Login failed for [email protected] against mail.dkboyz.dk from 192.168.1.1. Could not connect to ssl://mail.dkboyz.dk:993: Unknown reason)
Local error (from the ubuntu 20.4 server):
roundcube connection to storage server failed
I think that it’s a problem with Dovecot, because i get this when i run systemctl status dovecot:
I can’t seem to fix the problem.
Maybe you could lead me in the right direction?
Regards
Thomas
Dovecot can’t find your SSL certificate. Open the
/etc/dovecot/conf.d/10-ssl.conffile, make sure you specify the correct location of your SSL certificate and private key.Is this wrong???
It’s from the /etc/dovecot/conf.d/10-ssl.conf file.
‘# SSL/TLS support: yes, no, required.
ssl = required
ssl_cert = </etc/letsencrypt/live/dkboyz.dk-0001/fullchain.pem
ssl_key = </etc/letsencrypt/live/dkboyz.dk-0001/privkey.pem
It seems your certificate files are corrupted. Renew your certificate.
Then restart Postfix and Dovecot.
Dovecot should use the certificate for
mail.dkboyz.dk. The configuration should be:The certificate for
dkboyz.dkis irrelevant.I am also getting this error. I have removed certbot and purged it. Deleted the letsencrypt directory and sub directories. Re-installed certbot and regenerate the certs. These are the paths in my file
ssl_cert = </etc/letsencrypt/live/mail.aheart4god.us/fullchain.pem
ssl_key = </etc/letsencrypt/live/mail.aheart4god.us/privkey.pem
I am able to cd into that directory copying the path from the line above.
I did a force renew and restarted the postfix and dovecot. Still getting the error No Valid PEM.
any ideas?
Could this be causing a problem?
LISTEN 0 0 *:587 *:* users:((“smtpd”,pid=2823,fd=6),(“master”,pid=2606,fd=16))
Hey Xiao,
Thanks for the guide, good job. I just wanted to let you know that if you have more host names, it is actually easier just to use the temporary server when doing the challenge. I needed it for 4 host names and did the following.
Made my life a little easier 😉
/Christian
when i try to install certificate
sudo certbot certonly -a nginx –agree-tos –no-eff-email –staple-ocsp –email [email protected] -d mail.your-domain.com i got output
Saving debug log to /var/log/letsencrypt/letsencrypt.log
Plugins selected: Authenticator nginx, Installer None
Obtaining a new certificate
Performing the following challenges:
http-01 challenge for mail.mydomain.com
Waiting for verification…
Challenge failed for domain mail.mydomain.com
http-01 challenge for mail.mydomain.com
Cleaning up challenges
Some challenges have failed.
IMPORTANT NOTES:
– The following errors were reported by the server:
Domain: mail.mydomain.com
Type: unauthorized
Detail: Invalid response from
http://mail.mydomain.com/.well-known/acme-challenge/xT1TZ3cDXxx-9pk_XAplZcoPf6uprT0mUsSHNMkU2eI
[119.15.81.237]: “\r\n
404 Not
Found
\r\n
nginx/1.18.0 (Ub”
To fix these errors, please make sure that your domain name was
entered correctly and the DNS A/AAAA record(s) for that domain
contain(s) the right IP address.
If there’s a problem when trying to obtain the TLS certificate, please read the following article to learn how to troubleshoot.
How to Fix Common Let’s Encrypt/Certbot Errors
After upgrading to “20.10”, I can’t receive any mails with “Thunderbird”. I can only send out but with an error message that the message couldn’t be copied to the “sent”-folder. “Thunderbird” keeps telling me “[email protected]: Checking mail server capabilities…” in the status bar. “mail.err” has repeatedly this error message:
“Jan 21 00:43:58 test dovecot: imap-login: Error: Failed to initialize SSL server context: Can’t load DH parameters (ssl_dh setting): error:1408518A:SSL routines:ssl3_ctx_ctrl:dh key too small: user=, rip=192.168.1.1, lip=192.168.1.173, session=”
What does it mean and how can I repair my mail server?
i have a similar error, i’ve managed to send out emails, but Thunderbird told me “There was an error saving the message to Sent Messages. Retry?”. i could find incoming emails saved under /Maildir/cur, but no copy saved under /Maildir/.Sent for outgoing emails
Maybe you need to generate the Diffie-Hellman parameter with:
Then set
in
/etc/dovecot/conf.d/10-ssl.conffile.Thank you for this, all working perfectly, I am a linux newbie, always used windows in the past, you have made me want to learn a lot more about linux : )
Hi Guoan,
somehow i can’t get my android (outlook client) to send email to my ubuntu configured with dovecot and postfix with smtp auth.
I assume dovecot is the one for performing smtp-auth(?)
can you post some example, such as doveconf -Pn for references?
i can send out fine (to gmail), I can send from gmail to the vps fine too.
thanks
want to supplement more information.
– i want to compose an email from android outlook and relay to my ubuntu (20.04) vps, setup with dovecot, postfix and postfixadmin vmail.
– i can actually send successful, when using gmail android client setup
– i cannot send successful when using the outlook android client setup.
could be something with microsoft …again.
do let me know anything can be shared to look into it.
thanks
As a rule of thumb, you should always check the mail log (/var/log/mail.log) on your mail server when an error happens.
Thank you for this;
i can send emails from my email client but i don’t receive emails sent to me. My log is attached below
If you can’t receive emails from Gmail, Hotmail, Yahoo Mail, etc, here are the possible causes:
/var/log/mail.log) to find out if there are other errors in your Postfix and Dovecot configuration.You can use the Network Tools Email Checker to test if your SMTP server is reachable from the Internet. Just enter your domain email address and click the
Gobutton. As you can see from the screenshot below, it successfully found my domain’s MX record and my SMTP server is reachable from the Internet.If your SMTP servers isn’t reachable from the Internet, then you have a problem in the first 4 items. If your SMTP server is reachable from the Internet, but you still can’t receive emails, check the mail log (
/var/log/mail.log) to find out if there is any errors in your Postfix and Dovecot configuration.Your posted mail log is too short and I can’t work out a conclusion.
This is indeed one of the best, if not the only, step-by-step tutorial on making real-life email system. I having been trying to make this happen for 3 days with no fruitful results, until I read this series and followed it step by step.
Thank you a lot!
sudo doveadm user ‘*’
returns:
nobody
systemd-coredump
lxd
Danran
Error: auth-master: userdb list: User listing returned failure
Fatal: user listing failed
How do I start debugging this?
As a rule of thumb, you should always check the mail log (/var/log/mail.log) on your mail server when an error happens
Thank you. So i figured out that I missed a step just before running the sudo doveadm user’*’ command. I forgot to add a user. After running sudo adduser user1, My user list now looks correct! Thank you so much!
Wait, Im realizing, that this worked by adding a user, But my mistake was that I already was using a home user, not root. Do i need two seperate user account for this to work? Because that is the condition for me that makes this work. If i stick to one home user account, then i get the same error again.
I dont’ know exactly what I did, but now, I’m back to square one, but worse, because I’m getting absolutely zero errors in my logs now. The logs look clean, showing dovecot and postfix both running smoothly. Emails are seemingly working. But now,
sudo doveadm user ‘*’
returns:
Error: auth-master: userdb list: User listing returned failure
Fatal: user listing failed
and thats it. I’ve gone up and down my config files and logs. I did a clean install and tried from scratch again with the same problem surfacing. As of now, I’m at a total loss as to how I can fix this. I wish there was the equivilent of nginx -t for dovecot, so I could somehow know which line in which file has the broken syntax. I’m relatively close to going out of my mind after a good 6 hour staring contest with my computer! lol. Any more ideas here?
My mailbox is having issues saving sent mail to the sent folder when trying to send an email from thunderbird.
Below is the issue the message thunderbird gives me when “Un?Successfully” sending mail:
Your message was sent but a copy was not placed in your sent folder (Sent) due to network or file access errors.
You can retry or save the message locally to Local Folders/[email protected]
Any advice as how to debug this problem would be greatly appreciated! Thanks for a great tutorial!
As a rule of thumb, you should always check the mail log (/var/log/mail.log) on your mail server when an error happens
I think your problem is the same as Luis Pereira. It’s likely that you forgot to set
auth_username_format = %nIn/etc/dovecot/conf.d/10-auth.conffile.Thanks for the reply! I did check the auth_username_format = %n in 10-auth.conf file, and it was actually setup correctly. When I have some time to get back into this I will post some the logs that I am finding. Maybe you can help!
I’m still having the same issue after doing a clean install and following the guide again. What could be the issue? Please help?
tail -f /var/log/mail.log
sudo service dovecot status
● dovecot.service - Dovecot IMAP/POP3 email server Loaded: loaded (/lib/systemd/system/dovecot.service; enabled; vendor preset: enabled) Active: active (running) since Sat 2021-04-10 07:26:16 CDT; 7h ago Docs: man:dovecot(1) http://wiki2.dovecot.org/ Process: 3107 ExecReload=/usr/bin/doveadm reload (code=exited, status=0/SUCCESS) Main PID: 1804 (dovecot) Tasks: 7 (limit: 9256) CGroup: /system.slice/dovecot.service ├─1804 /usr/sbin/dovecot -F ├─1884 dovecot/anvil ├─3108 dovecot/log ├─3119 dovecot/imap-login ├─3120 dovecot/config ├─3121 dovecot/stats └─3125 dovecot/imap Apr 10 14:13:49 mail.facl.xyz dovecot[1885]: auth-worker(2733): Error: getpwent() failed: Invalid argument Apr 10 14:18:18 mail.facl.xyz systemd[1]: Reloading Dovecot IMAP/POP3 email server. Apr 10 14:18:18 mail.facl.xyz dovecot[1804]: master: Warning: SIGHUP received - reloading configuration Apr 10 14:18:18 mail.facl.xyz systemd[1]: Reloaded Dovecot IMAP/POP3 email server. Apr 10 14:18:18 mail.facl.xyz dovecot[1885]: imap(danran): Server shutting down. in=13075 out=54029 deleted=0 expunged=0 trashed=0 hdr_count=0 hdr_bytes=0 body_count=0 body_bytes=0 Apr 10 14:20:51 mail.facl.xyz auth[3124]: pam_unix(dovecot:auth): Couldn't open /etc/securetty: No such file or directory Apr 10 14:20:51 mail.facl.xyz auth[3124]: pam_unix(dovecot:auth): Couldn't open /etc/securetty: No such file or directory Apr 10 14:20:51 mail.facl.xyz dovecot[3108]: imap-login: Login: user=, method=PLAIN, rip=192.168.1.254, lip=192.168.2.2, mpid=3125, TLS, session= Apr 10 14:21:13 mail.facl.xyz auth[3124]: pam_unix(dovecot:auth): Couldn't open /etc/securetty: No such file or directory Apr 10 14:21:13 mail.facl.xyz auth[3124]: pam_unix(dovecot:auth): Couldn't open /etc/securetty: No such file or directorysudo service postfix status
● postfix.service - Postfix Mail Transport Agent Loaded: loaded (/lib/systemd/system/postfix.service; enabled; vendor preset: enabled) Active: active (exited) since Sat 2021-04-10 14:17:59 CDT; 10min ago Process: 3086 ExecStart=/bin/true (code=exited, status=0/SUCCESS) Main PID: 3086 (code=exited, status=0/SUCCESS) Apr 10 14:17:59 mail.facl.xyz systemd[1]: Starting Postfix Mail Transport Agent... Apr 10 14:17:59 mail.facl.xyz systemd[1]: Finished Postfix Mail Transport Agent.This indicates there is an error in your Dovecot configuration file. Probably a syntax error.
Thank you so much. I’ve gone over and over and over my config files time and time again, and am not seeing anything suspocious. Is there any way to figure out which line in what file is causing this? Any command like the equivilant of “sudo nginx -t”? You help and your guide are much appreciated!
Probably the error is in the
/etc/dovecot/conf.d/10-master.conffile. This tutorial shows you how to edit theservice authsection. You don’t need to edit theservice auth-wokersection.Okay excellent! I will work on this and get back to you! Thank you so much!
PROBLEM SOLVED! The /etc/dovecot/conf.d/10-master.conf file still had the following uncommented:
unix_listener auth-userdb {
#mode = 0600
#user =
#group =
}
After commenting out the unix_listener Auth-userdb {
and the
}
this issue seems to now be a non-issue and its working! Thanks a ton!
Thank you for all of your help! Do you think you might be able to give me a second pair of eyes on my 10-master.conf file? I have posted it on pastebin permanently (and publicly) and will keep it there forever, to help others if they encounter a similar problem. Pastbin seems to be important for proper formatting of the file so thats why I pasted it there. Please let me know if you see anything wrong with this file! I just cannot figure out whats wront and why my thunderbird won’t move its messages to the sent folder, even though sent emails go out and work. Thanks a ton Xiao! You are a master of tutorials!
Well, forget about my previous solution. I sweaer I didnt touch anything, but when I came back to test my emails on my server again, the exact problem came back. Either I’m not seeing something or i’m going crazy at this point, becausie I’ve gone over my 10-master.conf file for more than 4 hours. Back and forth back and forth up and down, and I just cannot figure out whats wrong with my file. Could I post my file here or email it to you possibly, and maybe have you take a look at it? Maybe you will see something I’m not seeing. It would be so much appreciated Xiao!
Ahh, forgot to mention, I am no longer seeing any errors with “`sudo service dovecot status“`. The only odd lin that comes up is “pam_unix(dovecot:auth): Couldn’t open /etc/securetty: No such file or directory”. My /var/log/mail.log is showing no errors either. I just cant figure out where the problem lies.
My thunderbird still gives me “Your message was sent but a copy was not placed in your sent folder (Sent) due to network or file access errors.
You can retry or save the message locally to Local Folders/[email protected].”
https://pastebin.com/gKZxq4J0
Found nothing wrong in your file. May you can check the Dovecot logs with
sudo journalctl -eu dovecot. It might also be a thunderbird problem. See here: https://support.mozilla.org/en-US/questions/1299140.I had this same issue. In the /etc/dovecot/conf.d/15-mailboxes.conf I had added the “auto = create” line under both
mailbox Sent {
and
mailbox “Sent Messages” {
After I removed “auto = create” under mailbox “Sent Messages” { . The Sent folder was created and the error went away in Thunderbird. I think you have to choose one or the other. If you choose both it doesn’t create either.
The comments above them say:
———
# For \Sent mailboxes there are two widely used names. We’ll mark both of
# them as \Sent. User typically deletes one of them if duplicates are created.”
——–
So I guess you can delete one of them also. I just left the “Sent Messages” there but didn’t add “auto = create” under it. Since it says something about marking them both as Sent. Not sure if it is necessary. Only have the one “Sent” folder created on my server though, so it’s working as it is supposed to.
Hey, thanks for the tip Jim W. I Finally got around to making this edit, and unfortunately I am still having the same problem. Any other ideas?
No sorry Danran. All I know is that is what fixed the error for me. Did you remember to restart the server after you made the change?
Hello Xiao.
I discovered your guide which is a great guide and very detailed. It allows to learn a lot about the process and the terms involved.
I reached this point (part 2), and I can send and receive emails, however, Dovecot does not seem to pick the received emails, and for that I cannot view them on Thunderbird, only with the “mail” command. The only error I get on the log files is this one:
Currently I’m not with lmtp enabled, because I tried with it and I did not receive any email at all, returning user not found by the email server.
Do you know what can I be missing? I rechecked my config twice.
Thank you very much
So I managed to make the connection from thunderbird. I set the “home_mailbox” on the postfix config to the Maildir folder, as was set on Dovecot.
But was this the right way? Or I’m I missing something that should be the Dovecot service moving the email?
And now, the mail command only shows old messanges in “/var/mail”, is that also supposed to be the behaviour?
What’s the value of
auth_username_formatin/etc/dovecot/conf.d/10-auth.conf?I didn’t set one, as I would like to login only with username.
By default, when Dovecot tries to find or deliver emails for a user, it uses the full email address. Since in this part, we only set up canonical mail users (using OS users as the mailbox user), Dovecot can’t find the user in full domain format ([email protected]), so we need to set
auth_username_format = %nto drop the domain part, then Dovecot should be able to find the mailbox user and you will be able to use Dovecot LMTP to deliver emails. Thehome_mailboxis not needed now.LMTP is required if you want to follow part 3 to set up virtual domain mailbox.
Thank you so much for this info Jim W. This is most likely my mistake as well! When I get back at my server, I will make the changes you suggested, and report back to confirm! Thanks so much for chiming in here!
Oh, alright, I didn’t understood that. That solved the problem. Thank you very much.
Yes I’ll follow all parts. I recently helped create a mail server with virtualmin, and I want to understand all the raw steps thats necessary to create a mail server (and if everything works, I’ll use it as my own).
Againt, thank you for this great guide!
Great series of tutorials! Thanks to you now I have a properly working mail server (and a web server with PHP as a bonus) on a US$ 5.00 Lightsail instance with 1 CPU and 1 GB of RAM, that was already an OpenVPN server: that wouldn’t be possible if your setup wasn’t so light weighted.
I have just one suggestion to make: if we set the mailbox location to “mail_location = maildir:~/Maildir/” (with a trailing slash at the end) instead of the suggested “mail_location = maildir:~/Maildir”, it will be possible to create folders in the mailbox for IMAP use. I believe that without the trailing slash the MBOX format would still be used, is that right?
And to create the folders I still have to use a shell terminal so I can see them in Outlook, Outlook still doesn’t let me add them using its interface. Is there any way to change this?
Thank you!
If you don’t configure LMTP, then email is delivered via Postfix’s built-in delivery agent, which uses
mboxformat by default.If you configure LMTP, then email is delivered by Dovecot. Since we set
mail_location = maildir:~/Maildir, the email will be stored in Maildir format.You can install the Roundcube webmail, which allows you to create additional folders. Roundcube is an open-source, feature-rich webmail client.
Install Roundcube Webmail on Ubuntu 20.04 with Apache/Nginx
Install Roundcube Webmail on Ubuntu 18.04 with Apache/Nginx
OK, I will save a snapshot of the instance and try Roundcube, to see how it will impact the performance.
Thank you very much!
Just by curiosity, I just checked where I got the tutorials to create a LAMP/LEMP stack, to install Mautic and to install iRedMail years ago, and who was the author: it was Linuxbabe, and you!
https://www.linuxbabe.com/linux-server/install-apache-mariadb-and-php7-lamp-stack-on-ubuntu-16-04-lts
https://www.linuxbabe.com/ubuntu/install-mautic-onubuntu-16-04-marketing-automation-software
https://www.linuxbabe.com/mail-server/ubuntu-20-04-iredmail-server-installation
Thanks for coming back. 🙂
Thank you very much a very informative all in one guide. I followed it to the dot and my email server has been running without any issue for the past 3 months. Now comes Letsencrypt renewal time and i’m struggling to get it to work. The server is an Ubuntu 20.04 Server, Apache 2.4.41 on the latest patch . Running this command:
i keep getting this error:
Have tried some suggestions on the internet one said i should create a 1234 file under /.well-known/acme-challenge/ and browse to it. That failing with the following error:
Also tried adding a Directory alias in the virtual host file like:
Alias /.well-known/ /var/www/mail.georgia.com/.well-known/ Options -Indexes +FollowSymLinks +MultiViews AllowOverride None Order allow,deny allow from allBut i still get the same error. Kindly assist with how i can solve this issue. Thank you.
If there’s a problem when trying to obtain the TLS certificate, please read the following article to learn how to troubleshoot.
How to Fix Common Let’s Encrypt/Certbot Errors
Just to point out to other users (Please correct me if I am wrong here Xiao) who modified the “Auto-create Sent and Trash Folder” section to include “SPECIAL USE”. If your version of dovecot is greater than v2.2.30, according to doc.dovecot.org/configuration_manual/namespace/#mailbox-settings
the following bug exists in dovecot:
“Note:
Due to a bug in Dovecot v2.2.30+ if special-use flags are used, SPECIAL-USE needs to be added to post-login CAPABILITY response as RFC 6154 mandates. You can do this with imap_capability = +SPECIAL-USE”
(I believe) To remedy this, you must edit your 20-imap.conf file with “sudo nano /etc/dovecot/conf.d/20-imap.conf”, and then change line 38 from “imap_capability = ” to “imap_capability = +SPECIAL-USE”, and then be sure it is uncommented.
bahh. I noticed this before I read the entire page 3 instructions. Sorry.
root@Postfix:/etc/nginx/conf.d# sudo certbot certonly -a nginx –agree-tos –no-eff-email –staple-ocsp –email [email protected] -d mail.ferniproyect.es
Saving debug log to /var/log/letsencrypt/letsencrypt.log
Plugins selected: Authenticator nginx, Installer None
Obtaining a new certificate
Performing the following challenges:
http-01 challenge for mail.ferniproyect.es
Waiting for verification…
Cleaning up challenges
Failed authorization procedure. mail.ferniproyect.es (http-01): urn:ietf:params:acme:error:dns :: DNS problem: NXDOMAIN looking up A for mail.ferniproyect.es – check that a DNS record exists for this domain
IMPORTANT NOTES:
– The following errors were reported by the server:
Domain: mail.ferniproyect.es
Type: None
Detail: DNS problem: NXDOMAIN looking up A for mail.ferniproyect.es
– check that a DNS record exists for this domain
root@Postfix:/etc/nginx/conf.d#
You need to wait for DNS propagation. Check your DNS propagation status at https://dnsmap.io
Thanks for your quick response, I still get the error, I have my DNS server with bind9 from another machine and I have added to the file db.ferniproyect.es the record A mail.ferniproyect.es, even so I still get the same error as before ….
What can I do?
Your DNS record contains a private IP address 192.168.14.2. Delete this IP address from your A record.
Thanks, this is great. Now, maybe you could write an awesome guide on how to create a reverse proxy to access the webmail feature for those of us that have an Apache webserver already running on a different server, but still want to access our webmail. I assume it is a reverse proxy, that is the only thing hurting me.
You can install webmail on the Apache web server, so you don’t need a reverse proxy. Webmail and Postfix/Dovecot can run on different hosts.
If you would like to use a reverse proxy, you can try HAProxy. It can redirect traffic to multiple hosts in the same network.
Hi Guoan:
I have spent days trying to figure out my problem and finally stumbled on your posts. First of all, thanks for your efforts!
Here is my problem: I recently set up an Ubuntu 20.04 mail server using postfix and dovecot. Everything works fine except that my users can not configure their gmail web interface to “send mail as”. During the smtp configuration on web, it complains “Server returned error: “TLS Negotiation failed, the certificate doesn’t match the host., code: 0”. One can configure the smtp with no problem on: Outlook, Thunderbird and gamil app etc. This problem only occurs on gmail web interface.
So, I checked that syslog and mail log but could not find anything wrong. The only problem I see is when I issue: journalctl -eu dovecot, it spits out:
pam_unix(dovecot:auth): Couldn’t open /etc/securetty: No such file or directory
For this error, I could not find a solution. I know in your above A & Q, two people mentioned this error, but the solutions do not apply to my case.
Could you help me on this? It is appreciated.
Hugh
Just try this
sudo cp /usr/share/doc/util-linux/examples/securetty /etc/securetty
Wonderful tutorial! I have a working email server on my VPS.
Xiao, is the portion on configuring sieve missing? I would like to redirect spam to the Junk folder, but as configured above spam is rejected by the server. Is this just a matter of installing the dovecot-sieve package and enabling sieve under “plugins” in /etc/dovecot/conf.d/20-lmtp.conf ?
Thank you!
If you need to move spam to junk folder, you can read the full guide in part 9: SpamAssassin.
Great tutorial! Really helping me learn how to set all this up! It’s almost perfect, however I found one thing you missed. You have to disable the 000-default host setup file that also points to the /var/www/html folder. I got an error when I tried generate the TLS cert. But fixed it by disabling the 000-default host file with “a2dissite 000-default” and reloaded apache with “systemctl reload apache2”. I was able to generate the TLS certificate. Might want to add that to the tutorial. I have Webmin installed so not sure if it was put there by Webmin. Or if it just comes with Ubuntu 20.04. But you might want to give it a mention.
Thanks for the tip 🙂
I can send and receive email, but Thunderbird requires me to make a security exception, saying my certificate is self-signed (but it’s not!). I followed all the steps, and re-checked my configs several times. In dovecot/conf.d/10-ssl.conf I’m pointed at my letsencrypt cert, but it seems like there’s some other (dovecot?) config, somewhere, overriding my letsencrypt cert. But I searched the dovecot docs and found nothing obvious.
The only other thing I can think of, I did set up slightly different than your example. My hostname is `myhost.com`. I create `mail.myhost.com`, A and MX records for it, created nginx server block (per your tutorial), restarted all services, rebooted… I’ve even tried several variations, but keep getting the same message saying my mail server is using self-signed cert.
Any help is appreciated. Thank you so much for all the great tutorials that you curate!!
You also need to use Let’s Encrypt certificate in your Postfix configuration (/etc/postfix/main.conf).
a silly question:
what does [email protected] parameters stand for?
thank you
Your own email address. Gmail, outlook, yahoo mail, etc. You can also use your domain email address.
Hello, thank you again for your great tutorials. I’ve noticed a couple of oddities in my build. When sending email from my server, if I use the echo command, email comes in from [email protected], but if I use the mail command, it arrives from [email protected]. Further, when trying to check mail I always get “Cannot open mailbox /var/mail/user: Permission Denied” but permissions appear to be correct. Any suggestions?
To specify the FROM address, use the following syntax.
The
mailcommand is used only in part 1 to show you Postfix works. The remaining parts of this tutorial series assumes you want to use a graphical email client. If you want to continue to use themailcommand, you will need to create a configuration file formailand adapt the configuration to the remaining parts of this tutorial series.For example,
mailby default uses the /var/mail/ directory to read emails. However, we configured Dovecot to store emails in~/Maildirin this article. And they are stored in Maildir format.For more info, read the manual
Personally I don’t use
mailcommand anymore. You might think it’s cool to send and read emails from command line, but it doesn’t play well with the remaining parts of this tutorial series.Also, it seems that external mail coming into the server is never received.
The
mailcommand by default uses the/var/mail/directory to read emails. However, we configured Dovecot to store emails in~/Maildirin this article. That’s why it can’t read incoming emails.If you use a graphical mail client like Thunderbird and can’t receive email, please read the troubleshooting tips in this article.
Sadly I did everything as this article, but I can not receive emails from external sources, sending emails locally actually does work 🙁
All ports are open, MX records set and correct
What’s your domain name? I can send an email from my mail server to you and see what’s wrong in your configuration.
futdeal.com
[email protected]
Thanks!
Your port 25 is open, but the connection timed out while receiving the initial server greeting, i.e. Your SMTP server doesn’t greet the SMTP client with HELO/EHLO.
Possible reasons:
1. You have syntax error in the
/etc/postfix/master.cffile and Postfix fails to run properly. In this situation, you can probabaly find the following error in the/var/log/mail.logfile.You should fix the syntax error in the
/etc/postfix/master.cffile.2. If you are using SMTP proxy software (such as HAProxy) in front of Postfix SMTP server, it could be that the connection between SMTP Proxy and SMTP server is broken.
3. There might be another firewall in your network that is interfering with SMTP connection. Check this page: https://success.trendmicro.com/solution/1055808-users-encounter-issues-when-sending-mails-to-some-domains
Thanks for the answer, I’m looking into it
Hello I have done everything and it seems to be receiving and able to send emails but I can’t connect it to an email client.
When I do try to connect it to an email client it looks like the traffic comes through to my server but nothing happens. Is there a log I can look into for any help?
Follow the instructions in the Troubleshooting Tips section.
I figured it out after weeks of trying. Thank you for an amazing guide.
My problem was that I didn’t add the email server to my dns resolver in pfSense.
When reloading dovecot, I consistently encounter the following error:
The solution is obvious, but could you explain to my why this keeps happening?
The answer is obvious. Because you changed the dovecot.service configuration file, so you need to reload systemd.
That’s not an error. It’s telling you what you should do.
Every time you change a systemd service unit file, you need to reload systemd (
sudo systemctl daemon-reload) for the changes to take effect.Just like you need to reload Nginx (
sudo systemctl reload nginx) after making changes to Nginx configuration files.I made a post about this on another of your tutorial pages. The thing is, this error kept appearing regardless of the fact that I made no changes. This message appears on every reboot. After much scouring the internet, I have concluded that the restart.conf file is causing this message to appear even after making no changes. Some user on github seem to think this is related to lack of a real time clock, which might make sense. After removing the restart.conf file, the error no longer appears after every reboot. Putting the file back, creates the error once again.
Did you run the
sudo systemctl daemon-reloadcommand after adding the restart.conf file?You can create a systemd service to automatically reload systemd after startup.
Add the following lines to this file.
Save and close the file. Then enable this service.
Also, you can set up NTP time sync.
I followed all of your tutorial and added a relay host. But it always land on promotion tab and this is my email test result https://www.mail-tester.com/test-fnaxr8q1g
Please help.
My advice for avoiding the promotion tab is when your emails are not promotional.
The Gmail promotion tab is for promotional emails. If you send promotional emails, they will land on the promotion tab.