How to Install ntopng Traffic Analysis Tool on Ubuntu Server
ntopng (ntop next generation) is a high-speed web-based traffic analysis and flow collection tool. This tutorial is going to show you how to install and use ntopng on Ubuntu server.
I started using ntopng because I wanted to block BitTorrent traffic on my cloud VPN server. If someone downloads illegal materials with BitTorrent when the computer is connected to my VPN server, my hosting provider will suspend my account. I also like to know if the OpenConnect VPN protocol is resistant to deep packet inspection (DPI). That’s very important for people who need a solid solution to bypass the national firewall to unblock Google, Facebook, YouTube, and other websites.
ntopng Features
- Cross-platform: supports Linux, BSD, macOS, and Windows.
- Real-time network traffic analysis in an intuitive web user interface.
- Encrypted traffic analysis with nDPI (Deep Packet Inspection).
- Limit/block the bandwidth of specific protocols (e.g. BitTorrent).
- Prioritise specific traffic protocols
- Identity application protocols (Facebook, Youtube, BitTorrent, etc) in the network.
- TLS fingerprinting to detect and block malware traffic.
- Traffic recording and replay.
- and much more
ntopng Editions
ntopng comes in four editions:
- Free open-source community Edition
- Pro Edition
- Enterprise M Edition
- Enterprise L Edition
In this tutorial, we are going to install the community edition.
Requirement
ntopng can use lots of CPU resources. It’s recommended to run it on a server with at least 4 CPU cores.
How to Install ntopng on Ubuntu Server
ntopng is available in the default software repository, but it’s recommended to install the latest stable version from the upstream ntopng repository. Run the following command to install dependency packages.
sudo apt install software-properties-common wget
Ensure the universe repository is enabled.
sudo add-apt-repository universe
Download the latest stable version of ntopng on Ubuntu 20.04.
wget https://packages.ntop.org/apt-stable/20.04/all/apt-ntop-stable.deb
If you use Ubuntu 18.04, run the following command to download ntopng.
wget https://packages.ntop.org/apt-stable/18.04/all/apt-ntop-stable.deb
Note: ntopng repository doesn’t support Ubuntu 22.04 yet, but you can install it directly from the Ubuntu repository (sudo apt install ntopng).
Then install the package, which will automatically add the ntopng repository.
sudo apt install ./apt-ntop-stable.deb
Update package index.
sudo apt update
Install ntopng.
sudo apt install pfring-dkms ndpi nprobe ntopng n2disk cento
Check ntopng version.
ntopng --version
Output:
Version: 5.2.220520 [Enterprise/Professional build] GIT rev: 5.2-stable:df2ab44db34f31be4edaa8a6411e0a41f6555948:20220520 Pro rev: r4754 Built on: Ubuntu 20.04.4 LTS System Id: L982E9B157104A1D2--U982E9B1572D52B86--OL Platform: x86_64 Edition: Enterprise L (Bundle) License Type: Time-Limited [Empty license file] Validity: Until Fri May 27 09:51:47 2022
Check status:
sudo systemctl status nprobe cento ntopng pf_ring
If a service isn’t running, start it with systemctl. For example, the centos service is inactive (dead), I need to restart it with:
sudo systemctl restart cento
By default, ntopng listens on port 3000.
sudo ss -lnpt | grep 3000

The web user interface is available at the http://ubuntu-server-ip:3000.
Setting Up Reverse Proxy
To access the ntopng Web interface using a domain name rather than typing IP address and port number, we can set up a reverse proxy for ntopng with Nginx or Apache. This also allows you to enable HTTPS with certbot.
Nginx
Nginx is a very popular web server and reverse proxy. If you prefer to use Nginx, run the following command to install it.
sudo apt install nginx
Then create a server block file for ntopng.
sudo nano /etc/nginx/conf.d/ntopng.conf
Add the following content to this file. Replace ntopng.example.com with your domain name. You should also create DNS A record for this sub-domain. If you don’t have a real domain name, I recommend going to NameCheap to buy one. The price is low and they give whois privacy protection free for life.
server {
listen 80;
listen [::]:80;
server_name ntopng.example.com;
access_log /var/log/nginx/ntopng.access;
error_log /var/log/nginx/ntopng.error;
location / {
proxy_pass http://127.0.0.1:3000;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Forwarded-Protocol $scheme;
proxy_set_header X-Forwarded-Host $http_host;
}
}
Save and close this file. Then test Nginx configuration.
sudo nginx -t
If the test is successful, reload Nginx for the change to take effect.
sudo systemctl reload nginx
Now you can access ntopng web interface via ntopng.example.com.
Apache
If you prefer Apache over Nginx, then install Apache web server by using the following command.
sudo apt install apache2
To use Apache as a reverse proxy, we need to enable the proxy modules and the header module.
sudo a2enmod proxy proxy_http headers proxy_wstunnel
Then create a virtual host file for ntopng.
sudo nano /etc/apache2/sites-available/ntopng.conf
Put the following configurations into the file. Replace ntopng.example.com with your actual domain name. Don’t forget to create DNS A record for this sub-domain. If you don’t have a real domain name, I recommend going to NameCheap to buy one. The price is low and they give whois privacy protection free for life.
<VirtualHost *:80>
ServerName ntopng.example.com
ErrorDocument 404 /404.html
#HTTP proxy
ProxyPass / http://localhost:3000/
ProxyPassReverse / http://localhost:3000/
#Websocket proxy
SSLProxyEngine on
<Location /:/websockets/notifications>
ProxyPass wss://localhost:3000/:/websockets/notifications
ProxyPassReverse wss://localhost:3000/:/websockets/notifications
</Location>
Header always unset X-Frame-Options
</VirtualHost>
Save and close the file. Then enable this virtual host.
sudo a2ensite ntopng.conf
Restart Apache
sudo systemctl restart apache2
Now you can access ntopng web interface using the domain name ntopng.example.com.
Enable HTTPS
To encrypt the HTTP traffic, we can enable HTTPS by installing a free TLS certificate issued from Let’s Encrypt. Run the following command to install Let’s Encrypt client (certbot) on Ubuntu 20.04.
sudo apt install certbot
If you use Nginx, then you also need to install the Certbot Nginx plugin.
sudo apt install python3-certbot-nginx
Next, run the following command to obtain and install TLS certificate.
sudo certbot --nginx --agree-tos --redirect --hsts --staple-ocsp --email [email protected] -d ntopng.example.com
If you use Apache, then you need to install the Certbot Apache plugin.
sudo apt install python3-certbot-apache
Next, run the following command to obtain and install TLS certificate.
sudo certbot --apache --agree-tos --redirect --hsts --staple-ocsp --email [email protected] -d ntopng.example.com
Where:
--nginx: Use the nginx plugin.--apache: Use the Apache plugin.--agree-tos: Agree to terms of service.--redirect: Force HTTPS by 301 redirect.--hsts: Add the Strict-Transport-Security header to every HTTP response. Forcing browser to always use TLS for the domain. Defends against SSL/TLS Stripping.--staple-ocsp: Enables OCSP Stapling. A valid OCSP response is stapled to the certificate that the server offers during TLS.
The certificate should now be obtained and automatically installed.

And you can access ntopng web interface via HTTPS: https://ntopng.example.com.
Traffic Flow Analysis
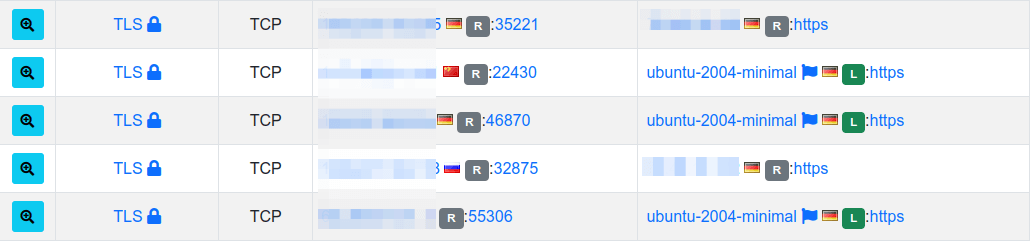
Go to the Flow tab in the ntopng dashboard, then select the main network interface. For example, my main network interface is eth0. You can view the active traffic flows. As you can see, ntopng identified Azure, MQTT, WireGuard VPN, CiscoVPN, MsSQL-TDS, and SSH traffic. If there’s no traffic in the ntopng web-based dashboard, it might be that cento.service and ntopng.service are not running.
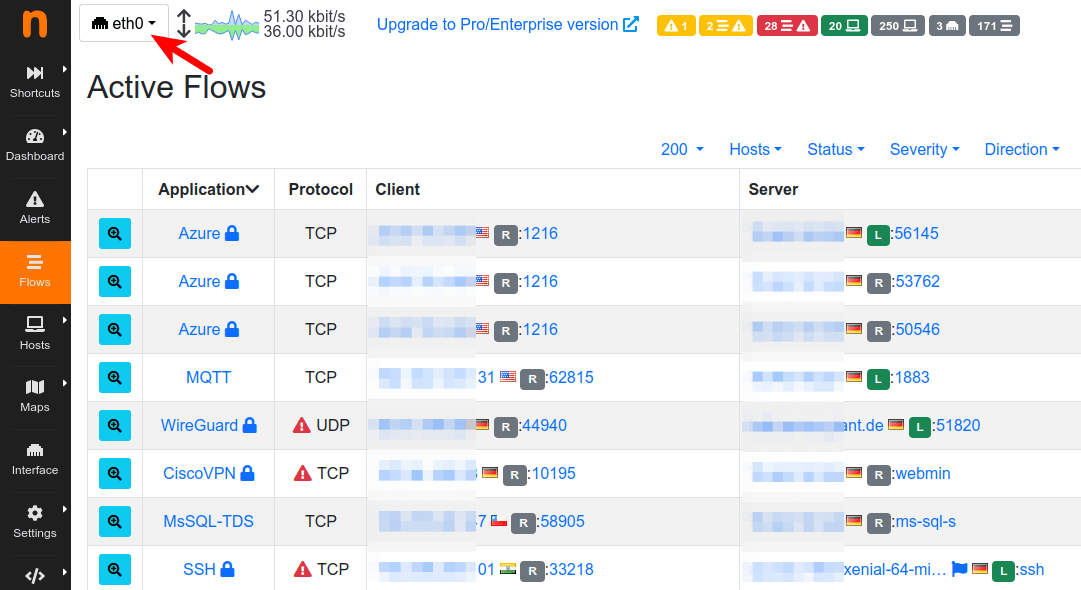
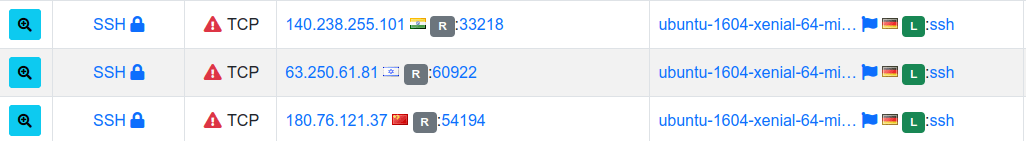
If you see some unknown IP addresses in the SSH section, don’t panic. It’s very likely to be SSH brute-force attacks, which can be shown with command sudo journalctl -eu ssh. Read the following article to learn how to harden your SSH service.
Deep Packet Inspection
Deep Package Inspection (DPI) is a technique that inspects the packet payload. It’s computationally intensive compared to simple packet header analysis. nDPI is an open-source DPI toolkit developed by the ntop team. It’s based on the unmaintained OpenDPI project. nDPI can inspect more than 240 protocols including:
- P2P (Skype, BitTorrent)
- Messaging (Viber, WhatsApp, Telegram, Facebook)
- Multimedia (YouTube, Last.gm, iTunes)
- Conferencing (WebEX, CitrixOnLine)
- Streaming (Netflix, Icecast, Shoutcast)
- Business (VNC, RDP, Citrix, WebEX)
- and more.
You can find a complete list of supported protocols here.
nDPI Traffic Classification
nDPI can use the TLS SNI (server name indication) header to differentiate YouTube traffic and Facebook traffic.
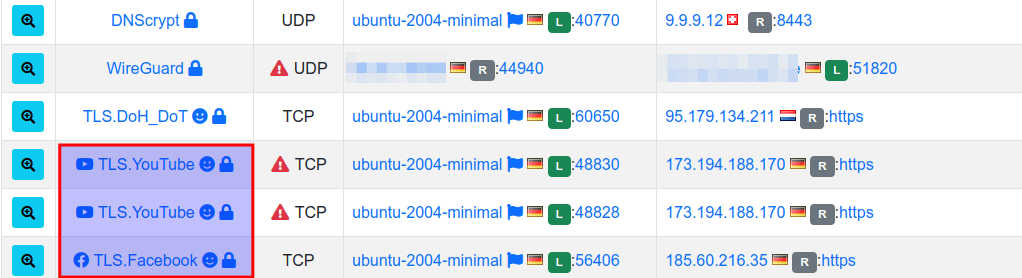
VPN Protocol Identification
Which VPN Protocol is resistant to Deep Packet Inspection (DPI)? ntopng can identify WireGuard VPN, OpenVPN, IPSec VPN, and Cisco VPN traffic. Is it able to differentiate normal HTTPS traffic and OpenConnect VPN traffic? (OpenConnect VPN is an HTTPS-based VPN protocol.)
nDPI isn’t able to identify OpenConnect VPN traffic. Like other HTTPS traffic, it’s shown as TLS traffic in the ntopng dashboard. So if you live in a country like China that utilizes DPI to block OpenVPN or WireGuard traffic, you should run an OpenConnect VPN server to stay under the radar.
Blocking BitTorrent Traffic with ntopng-edge
Hint: ntopng-edge requires a paid license. The Ubuntu repository doesn’t ship this package. It should be installed from the ntopng package repository.
Warning !!!: ntopng-edge can modify your server’s network settings. Please don’t install it on a cloud server if you don’t know how to deal with cloud server network configurations.
To block BitTorrent traffic, you need ntopng-edge (nedge) which is a Web-based edge traffic policer developed by the ntop team. It can throttle and block any network protocols that nDPI supports.
Remove ntopng and install nedge. They cannot be installed on the same server.
sudo apt remove ntopng sudo apt install nedge
- ntopng is a traffic analysis tool.
- ntopng-edge is a traffic policy enforcement tool.
ntopng-edge also listens on port 3000, so you can visit the web-based admin console at http://ubuntu-server-ip:3000. Once you are logged in, go to Protocol Policies tab and create your policies.
If you don’t need ntopng-edge anymore, you can stop with:
sudo systemctl stop nedge
Mask this service, so it can’t be started.
sudo systemctl mask nedge
Remove it with:
sudo apt purge nedge
Block BitTorrent Traffic in UFW
If you don’t want to pay for ntopng-edge, you can use UFW firewall to block BitTorrent traffic, though it’s not a perfect solution.
Wrapping Up
I hope this tutorial helped you install and use ntopng on Ubuntu. As always, if you found this post useful, then subscribe to our free newsletter to get more tips and tricks. Take care 🙂



When I try to perform the installation step I get the following message:
————>sudo apt install pfring-dkms ndpi nprobe ntopng n2disk cento
Reading package lists… Done
Building dependency tree
Reading state information… Done
E: Unable to locate package ndpi
E: Unable to locate package nprobe
E: Unable to locate package n2disk
E: Unable to locate package cento
—————————
Info ubuntu –>>> Ubuntu 20.04.4 LTS (GNU/Linux 5.13.0-1028-oracle aarch64)
It seems the upstream ntopng repository doesn’t support aarch64 architecture.
Hello Xiao,
Great article thanks.
I did the following test. With my Mac connected to Wireguard I’m downloading Ubuntu.iso with BitTorrent. My iPhone is also connected to the same Wireguard server, but it’s idle.
So I would like to see if I can find out that my Mac is downloading via torrent.
I can see on the eth0 that my Mac and my iPhone are both connected to the Wireguard. Then when I switch the interface from eth0 to Wg0, I can see the BitTorrent downloads shown on screen. However there is no mapping between the two interfaces. I can only see that somebody on my server is using Bittorrent, but I don’t know who. If there was a way to do a mapping between the two interfaces, I could get the user’s IP address and warn them to stop torrenting on my VPN server.
Do you know a way to achieve that, please?
Thanks,
Houman
Hello, can you write article about ntopng and mikrotik? I mean how analise traffic from mikrotik. ThankYou)