Use SSH Dynamic Port Forwarding to Bypass Great Firewall Of China
Dynamic port forwarding can be used to bypass the great firewall of China or any other firewall or Internet Filtering system. In this tutorial, we are going to look at using two SSH clients, OpenSSH and PuTTY, to create a secure SSH tunnel with dynamic port forwarding function.
Requirements
An SSH tunnel will be established between your computer and a remote server. To follow this tutorial, you will need a VPS (Virtual Private Server) that can access blocked websites freely (Outside of your country or Internet filtering system). I recommend Kamatera VPS, which features:
- 30 days free trial.
- Starts at $4/month (1GB RAM)
- High-performance KVM-based VPS
- 9 data centers around the world, including United States, Canada, UK, Germany, The Netherlands, Hong Kong, and Isreal.
Follow the tutorial linked below to create your Linux VPS server at Kamatera.
Once you have a VPS with OpenSSH server up and running, follow the instructions below.
Dynamic Port Forwarding with the OpenSSH SSH Client
The OpenSSH SSH client is shipped with almost every Linux distribution, and it’s also been ported to Windows 10 and Windows 11. The following command will connect you to the remote SSH server and at the same time enable dynamic port forwarding.
ssh -D port-number user@ssh-server-ip
If you have a user john on the remote SSH server 12.34.56.78, then you can run:
ssh -D 1080 [email protected]
Enter the password for user john. -D option enables dynamic port forwarding. 1080 is a common port. You can also use other ports such as 8080.
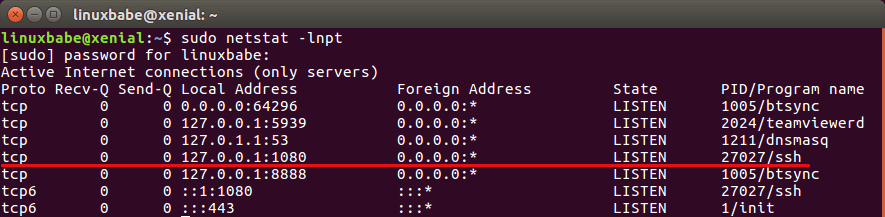
After you run this command, a secure SSH tunnel with dynamic port forwarding will be established between your Linux PC and your SSH server. The SSH client will be listening on 127.0.0.1:1080 acting as a local SOCKS proxy server. You can check this out with
sudo netstat -lnpt
Directing Browser Traffic Through the SSH Tunnel
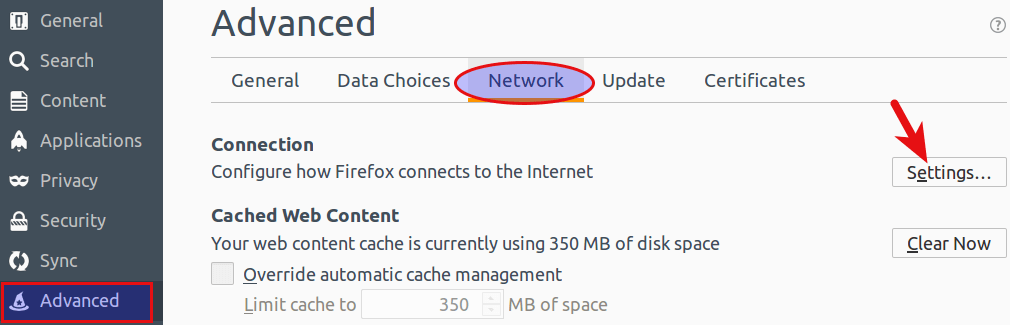
Now in your Firefox browser, go to Preferences > Advanced > Network > Settings.
Select Manual proxy configuration. Enter 127.0.0.1 in the SOCKS Host field, enter 1080 as the port number. Check SOCKS v5 and Remote DNS. Hit the OK button.
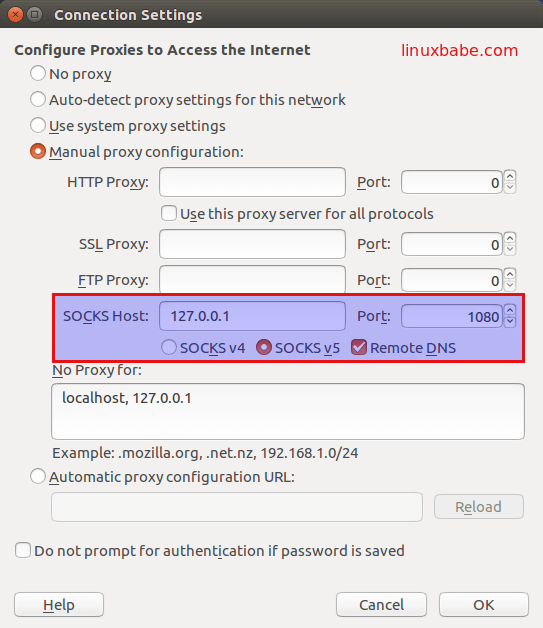
If you don’t check Remote DNS, your DNS traffic will not be tunneled.
Now go to https://www.whatismyip.com. You will find your IP is the SSH server’s IP. You have successfully bypassed the firewall and can freely browse the Internet.
In fact, all programs with SOCKS proxy support can use this SSH tunnel to hide the real IP address.
If you are on a slow network, compression can be enabled with -C option to speed up connection like below:
ssh -C -D 1080 [email protected]
If you don’t want to enter your SSH password every time, you can set up passwordless SSH login.
Dynamic Port Forwarding with PuTTY SSH Client
The PuTTY SSH client also supports dynamic port forwarding. On Debian/Ubuntu, PuTTY can be installed with:
sudo apt-get install putty
Open PuTTY SSH client, select SSH > Tunnels on the left pane. Then on the right pane, enter the source port such as 1080. Select Dynamic as the type of port forwarding and Click Add button.
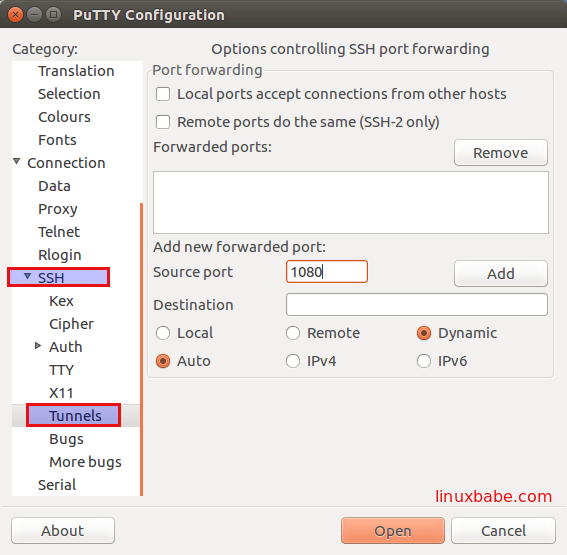
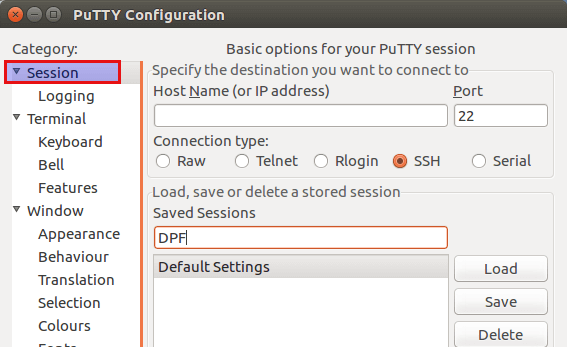
Then click Session on the left pane, enter your server’s IP in the Host name field. In the Save Sessions field, enter a name for this session like DPF (dynamic port forwarding) and click Save button.
Then enter your username and password to connect to the SSH server. An SSH tunnel with dynamic port forwarding will be created and PuTTY will be listening on 127.0.0.1:1080 acting as a local SOCKS proxy server. Check out listening ports on your computer with netstat command:
sudo netstat -lnpt
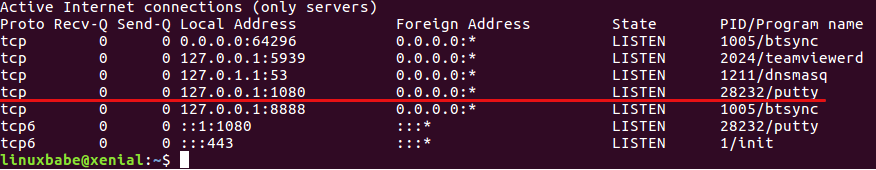
Now all you need to do is direct your browser’s traffic through this SSH tunnel.
All traffic in the SSH tunnel is encrypted. If you are using insecure public Wi-fi, you may consider using SSH dynamic port forwarding to encrypt all your traffic.
Note that the SOCKS proxy will stop working when the SSH session ends.
Comments, questions, or suggestions are always welcome. If you think this post is useful, share it with your friends on social media! Stay tuned for more Linux tutorials.



IS this article valid in 2019??
No. SSH port forwarding doesn’t work in China anymore. I’m now using OpenConnect VPN to bypass the great firewall, which works very well.
This method still works in China. However, if you are using chrome as browser, by default, chrome will use your local name server to resolve domains like google.com etc. and that fails. I haven’t found how to configure DNS in chrome under windows.
Having changed to firefox which can force DNS over Socks or over HTTPS. And that works.
I am balling, I am faded, I am drowning, help me to breeeeeeaaaaaaaaatttttthhhhhhhhh
hey guys make sure to check out Willis College for all your networking education needs!