A Practical Guide to GPG Part 5: Digital Signature
In previous GPG tutorials, I explained using GPG for encryption. In this part, you will learn how to use GPG to add digital signatures on documents. GPG provides two modes of signing:
- Signing without encryption
- Signing with encryption
Signing without Encryption
GPG can sign a document without encrypting it. Sometimes you may want to send someone a document and you don’t care whether the content is confidential or not but you want to make sure that the person who receives it knows the document comes from you and also hasn’t been tampered with.
We can do so by signing a document with our private key in the following syntax.
gpg --clearsign /path/to/file
Let’s create a test txt file.
echo "This is a test text file" > test.txt
Then add a digital signature on this file.
gpg --clearsign test.txt
- The
--clearsignoption means to make a clear text signature. The content will still be readable without using any special software. OpenPGP software is only needed to verify the signature. - GPG uses your private key to create the digital signature so you will be prompted to enter your passphrase to unlock the private key. When the command is completed, a new file with
.ascextension is created. - If you have multiple GPG key pair, then you can select a speficif private key with:
gpg --local-user user-id --clearsign test.txt.
There’re some interesting tidbits you can get from this .asc file, so open it with your text editor such as Nano.
nano test.txt.asc
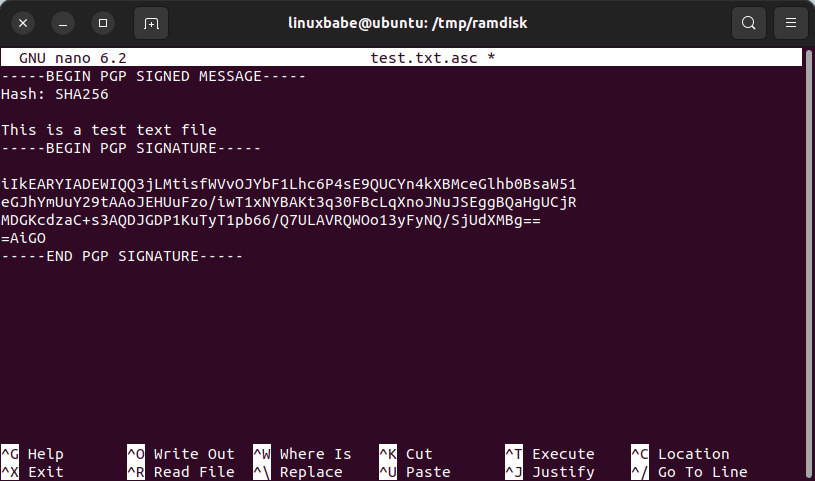
You will find the hash algorithm used. In my case GPG used SHA256 as the hash algorithm which is strong enough. Note that SHA1 is obsolete. The PGP signature is placed right after the original content. The plaintext file is first hashed, then your private key is used to sign the hash.
Exit the Nano text editor by pressing Ctrl+X.
Verify the Signature
In part 3, we created a test user account, and imported the public key, so let’s move the signature file to the test user’s home directory.
sudo mv test.txt.asc /home/test/
Then switch to the test user account.
su - test
Verify the signature with the following command:
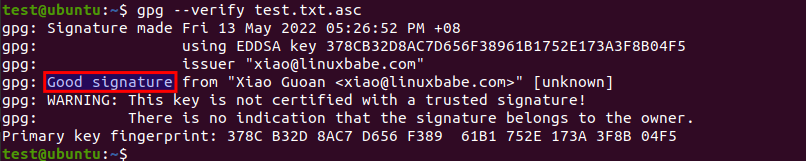
gpg --verify test.txt.asc
The verification does two things.
- It makes sure that the file has not been changed somehow in transit. There’s a hash calculated and then the hash is signed with the private key. By signing with the private key, it allows the recipient to determine the authenticity of the sender.
- During the verification process, GPG determines what key (key ID) is used to sign the document and then use the corresponding public key from public keyring to verify the signature.
If it say “Good signature”, then the verification is successful, so you know this file hasn’t been tampered with and is really come from the sender.
Signing with Encryption
If we want to make sure that the authenticity of the sender is checked as well as the integrity of the encrypted message and we want to provide confidentiality, use the below command:
gpg --armor --recipient user-id -e --sign /path/to/file
Where
--armor: Create ASCII armored output. The default is to create the binary OpenPGP format.user-idis the recipient’s email address.-e: Encrypt the file.
You need to enter your passphrase to unlock the private key. It combines the commands to sign and encrypt in one step. It first signs the document with your private key, then encrypts it with the recipient’s public key.
Decrypt and Verify
The decrypt process will automatically verify the signature.
gpg --decrypt filename.asc
Next Step
In the next part, we will learn how to verify software downloads on Linux.


