Configure DNS over TLS on Linux Mint to Protect DNS Privacy
This tutorial will be showing you how to protect your DNS privacy on Linux Mint with DNS over TLS. We will use a tool called stubby, but first, let me tell you why DNS is not secure.
DNS Vulnerability
DNS is insecure because by default DNS queries are not encrypted. They are sent in plain text on the wire and can be exploited by middle entities. For example, the Great Firewall of China (GFW) uses a technique called DNS cache poison to censor Chinese Internet. (They also use other methods, which are beyond the scope of this article.)
GFW checks every DNS query that is sent to a DNS server outside of China. Since plain text DNS protocol is based on UDP, which is a connection-less protocol, GFW can spoof both the client IP and server IP. When GFW finds a domain name on its block list, it changes the DNS response.
For instance, if a Chinese Internet user wants to visit google.com, GFW returns an IP address located in China instead of Google’s real IP address, to the user’s DNS resolver. Then the DNS resolver returns the fake IP address to the user’s computer, so the user cannot visit google.com.
What is DNS over TLS? How It Protects Your DNS Privacy?
DNS over TLS means that DNS queries are sent over a secure connection encrypted with TLS (Transport Layer Security), which is the same technology that encrypts HTTP traffic, so no third parties can see your DNS queries. Combined with HTTPS sites and encrypted SNI (Server Name Indication), your web browsing history will be fully protected from ISP spying.
Stubby is an open-source DNS stub resolver. A stub resolver is a small DNS client on the end-user’s computer that receives DNS requests from applications such as Firefox and forwards requests to a recursive resolver like 1.1.1.1 or 8.8.8.8. Stubby is special in that it supports DNS over TLS. By default, it will only send encrypted DNS queries.
Note: This tutorial only works on Linux Mint 19, including 19.1 and 19.2. If you are using Linux Mint 18, please upgrade your system.
How to Use Stubby to Configure DNS over TLS on Linux Mint
Stubby is included in Linux Mint 19 software repository. Open up a terminal window and run the following command to install it.
sudo apt install stubby
Once installed, stubby automatically runs in the background. You you check its status with:
systemctl status stubby
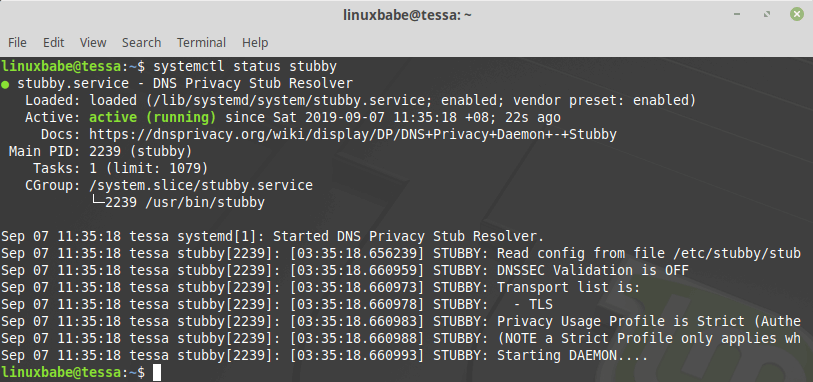
Hint: If the above command doesn’t quit immediately, you can press the Q key to quit the command and gain back control of the terminal.
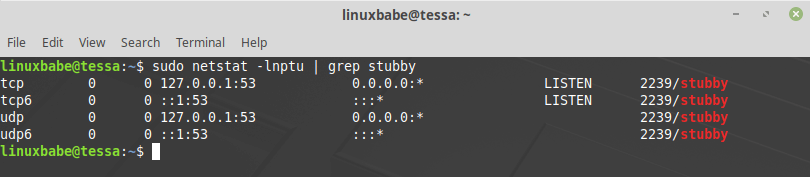
Stubby listens on TCP and UDP port 53 of localhost (127.0.0.1), as can be seen by running this command:
sudo netstat -lnptu | grep stubby
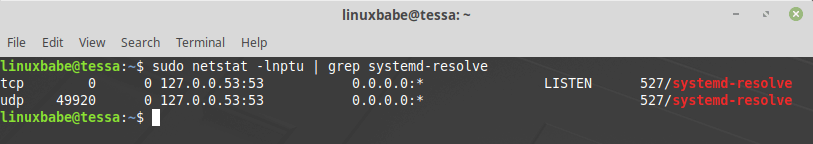
The default stub resolver provided by systemd-resolved listens on TCP and UDP port 53 of 127.0.0.53.
sudo netstat -lnptu | grep systemd-resolve
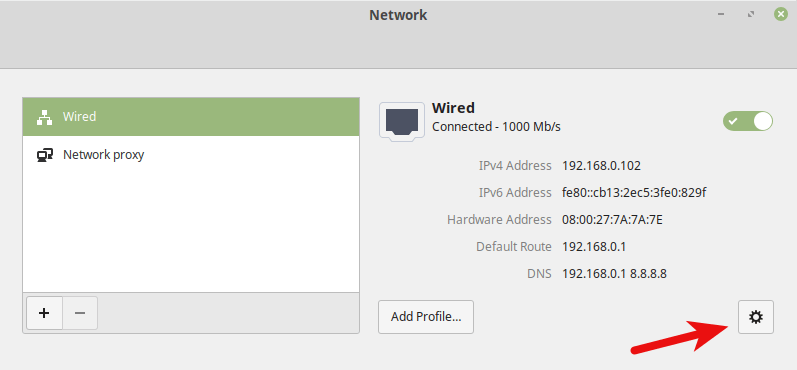
Now that stubby is installed and running, we need to tell our Linux Mint system to use it. Click the Network Manager icon on the bottom-right corner of your desktop, then select Network Settings.
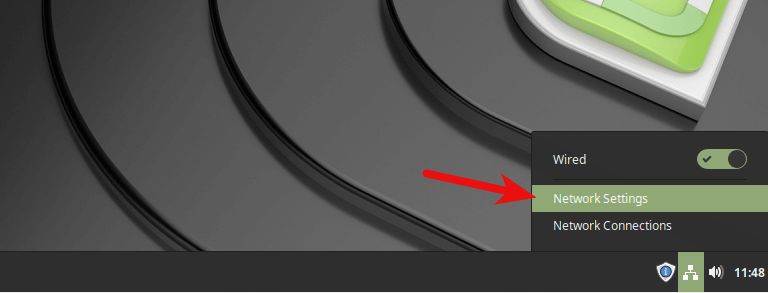
Click the gear icon to configure network.
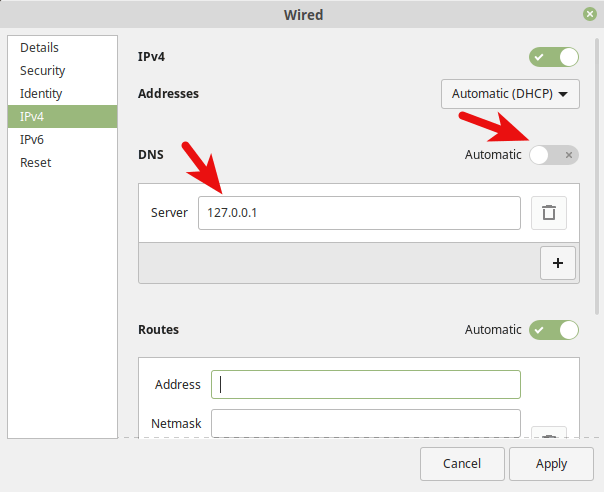
Select IPv4 tab and switch off Automatic in DNS. This will prevent your Linux Mint system from getting DNS server address from your router. Then specify the address of Stubby (127.0.0.1) in the Server text field. Click the Apply button and close the Network window.
Then run the following command in terminal to restart NetworkManager, in order for the above changes to take effect.
sudo systemctl restart NetworkManager
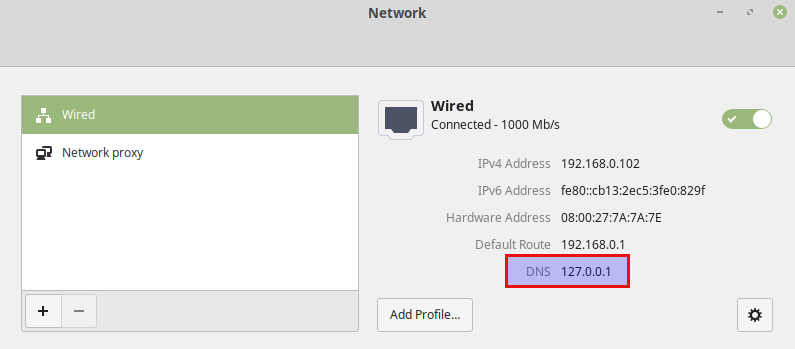
Once you are reconnected to your router, click the Network Manager icon again and select Network Settings. You can see that your Linux Mint system is now using 127.0.0.1 (stubby) as the DNS server.
How to Switch to Stubby From the Command Line
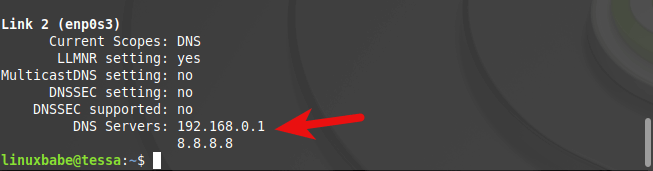
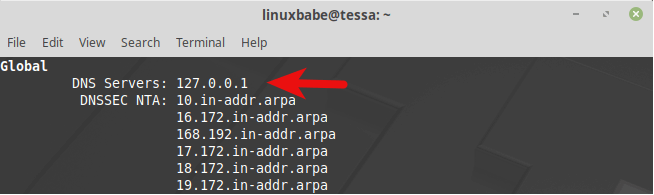
You can also make your Linux Mint system use stubby by configuring systemd-resolved from the command line. The default DNS server can be seen with this command.
systemd-resolve --status
To set Stubby as the default server, open the systemd-resolved configuration file with a command line text editor, such as Nano.
sudo nano /etc/systemd/resolved.conf
Use the arrow keys to move up and down. In the [Resolve] section, add the following line to make your system use Stubby.
DNS=127.0.0.1

Save and close the file. (To save a file in Nano text editor, press Ctrl+O, then press Enter to confirm. To exit, press Ctrl+X.)
Then restart systemd-resolved service.
sudo systemctl restart systemd-resolved
Now run the following command to check the default DNS server.
systemd-resolve --status
You will see 127.0.0.1 is set as the DNS server in the Global section.
How to Check if Your DNS Traffic is Encrypted
We can use WireShark to monitor DNS traffic. Run the following command in terminal to install WireShark from Linux Mint repository.
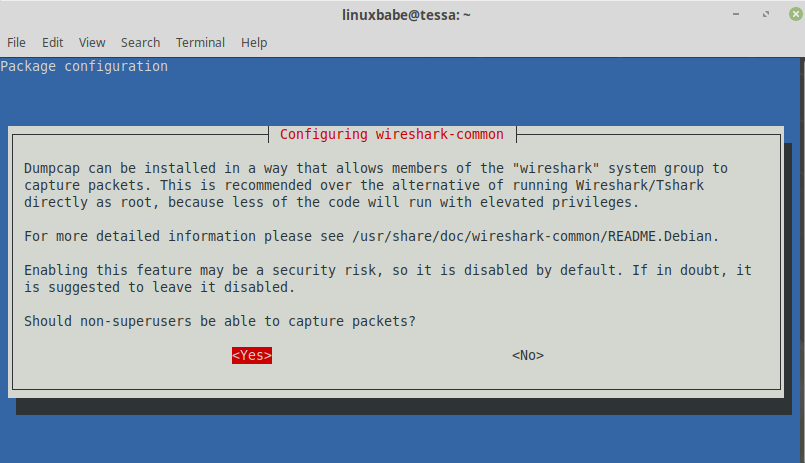
sudo apt install wireshark
If you are asked “Should non-superusers be able to capture packets?”, use the arrow key to select Yes and press Enter.
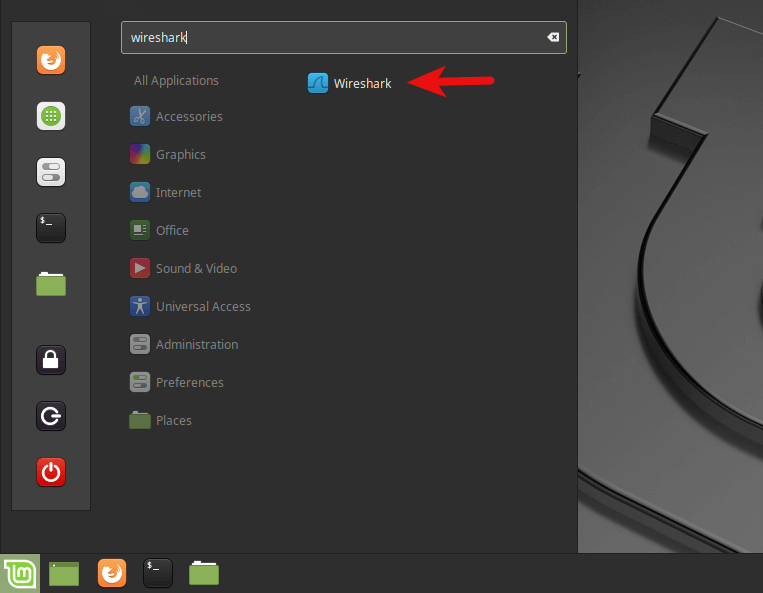
Once it’s installed, run the following command to add your user account to the wireshark group so that you can capture packets. Replace your-username with your real username.
sudo adduser your-username wireshark
Log out and log back in for the changes to take effect. Then open WireShark from your application menu.
Select your network interface in WireShark. For example, my Ethernet interface name is enp0s3. If you are using Wi-Fi, then your network interface name will be something like wlp0s3. Then enter port 853 as the capture filter. This will make WireShark only capture traffic on port 853, which is the port used by DNS over TLS.
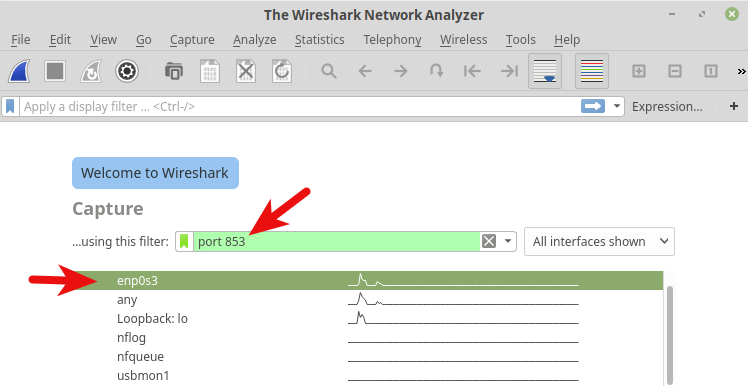
Press Enter to start capturing traffic. After that, in terminal window, run the following command to query a domain name by using the dig utility. For instance, I can query the A record of my domain name.
dig A linuxbabe.com
Now you can see the captured DNS traffic in WireShark. As you can see, my DNS query was sent to 185.49.141.37, 145.100.185.15 or 145.100.185.16, which are the 3 default DNS resolvers defined in stubby configuration file. Connections were made over TCP and encrypted with TLS, which is what I want. Click the red button on the upper-left corner to stop capturing traffic.
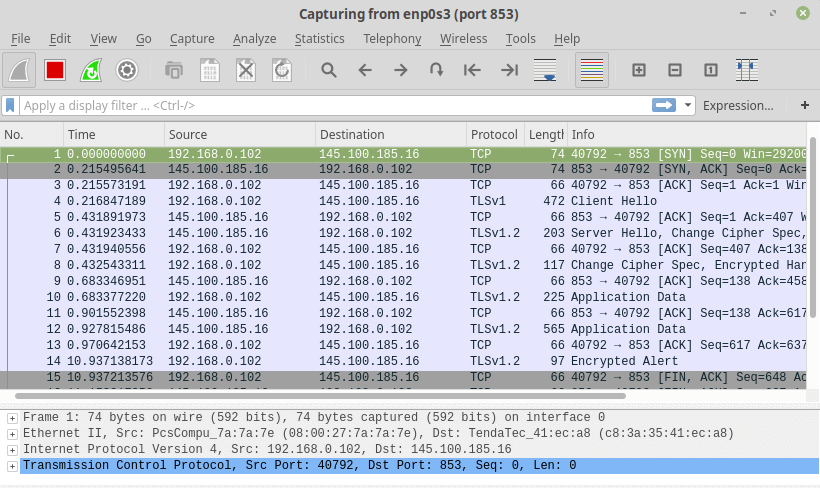
If DNS queries are sent without encryption, then the computer would contact DNS server on port 53. You can capture packets again with port 53 as the capture filter, but you won’t see any packets in WireShark, which means stubby is encrypting your DNS queries.
Wrapping Up
I hope this tutorial helped you protect your DNS privacy on Linux Mint with DNS over TLS. As always, if you found this post useful, then subscribe to our free newsletter to get more tips and tricks. Take care.



Great !
Is that for one time installing n setup process? Next time if we want to use DoT (DNS over TLS) all we have to do is turn on the stubby?
If you followed this tutorial exactly, then stubby would automatically start at boot time. All your DNS requests are encrypted. It is a one time setup process.
Thanks! 👍
how to undo this? After installing Stubby, I cannot run steam
All this is wonderful – but there’s a logical loop. If DNS is not enabled we can’t download the package (or any other update)
/etc$ sudo apt install stubby
Reading package lists… Done
Building dependency tree
Reading state information… Done
The following packages were automatically installed and are no longer required:
linux-headers-5.4.0-65 linux-headers-5.4.0-65-generic linux-image-5.4.0-65-generic linux-modules-5.4.0-65-generic linux-modules-extra-5.4.0-65-generic
Use ‘sudo apt autoremove’ to remove them.
The following additional packages will be installed:
libev4 libgetdns10 libunbound8
The following NEW packages will be installed:
libev4 libgetdns10 libunbound8 stubby
0 upgraded, 4 newly installed, 0 to remove and 0 not upgraded.
Need to get 601 kB of archives.
After this operation, 1,801 kB of additional disk space will be used.
Do you want to continue? [Y/n] y
Err:1 http://archive.ubuntu.com/ubuntu focal/universe amd64 libev4 amd64 1:4.31-1
Could not resolve ‘archive.ubuntu.com’
Ign:2 http://archive.ubuntu.com/ubuntu focal-updates/main amd64 libunbound8 amd64 1.9.4-2ubuntu1.2
You can use any other DNS resolver like 8.8.8.8 before installing stubby. After that, configure the stubby to use a DNS over TLS resolver.
If your system can’t resolve DNS, I’m wondering why can you browse this web page?
Can no longer ping after setup. Any reason?
can ping ips but not fqdn
How should I do it for Mint Linux 22? Somehow it will set a secundary or tetriary DNS server from my router. and what is the diferrence between /etc/resolv.conf (points to 127.0.0.53) and /etc/systemd/resolved.conf (has only DNS=127.0.0.1)?