How To Use SaferVPN on Linux – 81% Off
SaferVPN is a VPN service provider from Israel. In this article, I’m going to show you how to use SaferVPN on Linux, including Debian, Ubuntu, Linux Mint, Elementary OS, Fedora, CentOS, Arch Linux, OpenSUSE.
Why You Need to Use VPN on Your Computer and Mobile Devices
For those who don’t know, VPN stands for Virtual Private Network, which sets up a secure, encrypted “tunnel” between your device and the rest of the Internet. Common use cases of VPN includes:
- Encrypt your online traffic, protect your web browsing history from ISP and government.
- Unblock region-restricted content (Netflix, Hulu, etc), if your country isn’t supported by these streaming services, or you are traveling abroad.
- Bypass online censorship and access websites that are blocked in your country or area, such as Google, YouTube, Facebook.
- Prevent ISP from injecting ads in your Web browser.
- Encrypt your web traffic when using public Wi-Fi (in airport lounge, coffee shop or hotel Wi-Fi). Prevent hacker in the same Wi-Fi network from intercepting your Internet traffic and stealing your email address, passwords and credit card numbers.
- Hide your IP and identity when you are downloading files with BitTorrent client.
- Gamers can use VPN to find the best route to reduce gaming lag.
- Many online booking services like Kayak are known to offer different prices for different countries. When you are booking flights or hotel online, you can use VPN to switch your IP address in order to find the best deal.
What SaferVPN Has to Offer
SaferVPN features:
- Highspeed connection.
- Unlimited speed and data transfer.
- Supports PPTP, L2TP/IPSec, OpenVPN and IKEv2 protocol.
- Graphical VPN client available for Android, iOS, Mac OS X and Windows.
- Browser extension available for Firefox and Google Chrome.
- Multiple Logins. You can use SaferVPN to browse anonymously on multiple devices at the same time.
- Access to all servers. SaferVPN has over 14,000 IPs and 700 servers in 34 different countries, allowing you to switch servers at all times and as often as you like.
- No logging policy. SaferVPN doesn’t collect, log or store any browsing activity, data or IP addresses.
- Torrenting is supported.
- SaferVPN uses a strong AES-256 encryption when connecting to a VPN server.
- VPN kill switch. If the VPN connection drops, the computer defaults back to the original public IP. A VPN kill switch cuts your connection to the internet altogether when your VPN connection fails, so your web traffic are never exposed to hackers and snoopers.
- 24/7 Phone, email and live chat support
- 30-Day Money-Back Guarantee
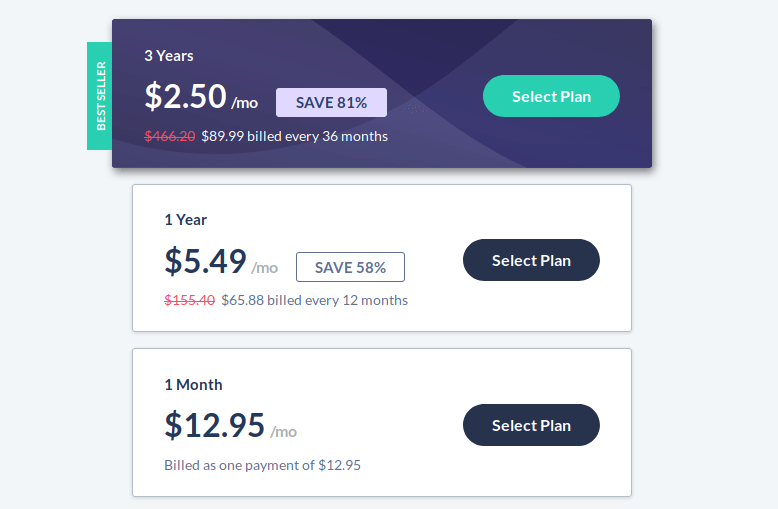
Pricing and Payment
See pricing here.
- Monthly plan starts at 12.95 USD per month.
- Yearly plan starts at 5.49 USD per month.
- If you buy the three-year plan, you monthly cost would be 2.5 USD.
SaferVPN supports the following payment methods:
- Credit card
- PayPal
- Bitcoin
How to Use SaferVPN on Linux
SaferVPN supports PPTP, L2TP, IKEv2 and OpenVPN protocols. We will use OpenVPN, since it’s very secure and easy to set up.
First, click here to go to SaferVPN official website and sign up for a plan. After signing up, Linux users have to manually set up VPN connection on their computer, because SaferVPN client isn’t available for Linux. Don’t worry, It’s pretty easy.
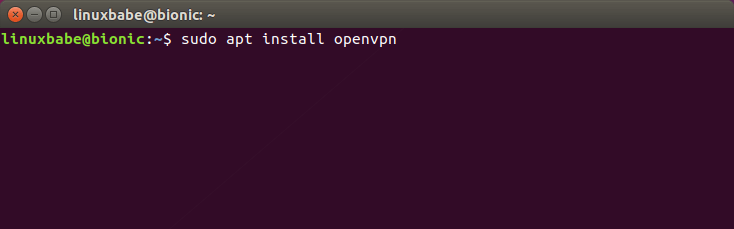
Open up a terminal window and use the package manager of your Linux distribution to install OpenVPN client.
Debian/Ubuntu/Linux Mint/Elementary OS/Linux Lite
sudo apt install openvpn
Fedora/CentOS/RHEL
sudo dnf install openvpn
or
sudo yum install openvpn
Arch Linux/Manjaro
sudo pacman -S openvpn
OpenSUSE
sudo zypper install openvpn
Then we need to create an OpenVPN configuration file with a text editor like gedit or nano. I will use the Nano command line text editor in this article. The following command will create an empty file named safervpn.confunder the /etc/openvpn/ directory.
sudo nano /etc/openvpn/safervpn.conf
Copy the following text and paste them into the safervpn.conf file.
client dev tun remote sg1.safervpn.com 1194 remote jp1.safervpn.com 1194 remote us1.safervpn.com 1194 remote us2.safervpn.com 1194 script-security 2 setenv PATH /usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin up /etc/openvpn/update-systemd-resolved up-restart down /etc/openvpn/update-systemd-resolved down-pre resolv-retry infinite nobind persist-key persist-tun persist-remote-ip tls-client remote-cert-tls server auth-user-pass /etc/openvpn/auth.txt comp-lzo verb 5 auth SHA256 cipher AES-256-CBC <ca> -----BEGIN CERTIFICATE----- MIIE1jCCA76gAwIBAgIJAOnRq4FWsZgYMA0GCSqGSIb3DQEBCwUAMIGiMQswCQYD VQQGEwJVUzELMAkGA1UECBMCQ0ExFTATBgNVBAcTDFNhbkZyYW5jaXNjbzERMA8G A1UEChMIU2FmZXJWUE4xETAPBgNVBAsTCFNhZmVyVlBOMREwDwYDVQQDEwhTYWZl clZQTjERMA8GA1UEKRMIU2FmZXJWUE4xIzAhBgkqhkiG9w0BCQEWFHN1cHBvcnRA c2FmZXJ2cG4uY29tMB4XDTE3MDgzMTA5NDEyM1oXDTI3MDgyOTA5NDEyM1owgaIx CzAJBgNVBAYTAlVTMQswCQYDVQQIEwJDQTEVMBMGA1UEBxMMU2FuRnJhbmNpc2Nv MREwDwYDVQQKEwhTYWZlclZQTjERMA8GA1UECxMIU2FmZXJWUE4xETAPBgNVBAMT CFNhZmVyVlBOMREwDwYDVQQpEwhTYWZlclZQTjEjMCEGCSqGSIb3DQEJARYUc3Vw cG9ydEBzYWZlcnZwbi5jb20wggEiMA0GCSqGSIb3DQEBAQUAA4IBDwAwggEKAoIB AQCqNV7oJZrUqD/mBSWlKi/sGRE2y3Yphs5m/vmmS4GPrc8lyaI1idhv44MGZ0i1 XCkJFZmaVQk7NUz5npz9hcnxN3MiZd/5Kv8Vo4aQkL0xQ7euto71LIgTqbJvTJjW kowsVVgartGK2ewfCd+KV6k5oBImlDdSnLW1pq82Kg+YcnXxdaFc8RpNWdBbdxBe tb4k6JcoZHuk9Zq5gi5Nnhtjc6lheCRzTGZ2hslDfJ58yMpR0jTMC3Rd+G+sM0q3 /gEEEW34ckUgCb5j6Kq35LUlnuonnViBnEzFR/MTizMARFj7VYkzOpxSsxJ6Epan JP8Zgbz81z4A822hosakl7kTAgMBAAGjggELMIIBBzAdBgNVHQ4EFgQUKSnUrJLQ omrGvdncxKkKT7Rxrj8wgdcGA1UdIwSBzzCBzIAUKSnUrJLQomrGvdncxKkKT7Rx rj+hgaikgaUwgaIxCzAJBgNVBAYTAlVTMQswCQYDVQQIEwJDQTEVMBMGA1UEBxMM U2FuRnJhbmNpc2NvMREwDwYDVQQKEwhTYWZlclZQTjERMA8GA1UECxMIU2FmZXJW UE4xETAPBgNVBAMTCFNhZmVyVlBOMREwDwYDVQQpEwhTYWZlclZQTjEjMCEGCSqG SIb3DQEJARYUc3VwcG9ydEBzYWZlcnZwbi5jb22CCQDp0auBVrGYGDAMBgNVHRME BTADAQH/MA0GCSqGSIb3DQEBCwUAA4IBAQB704c0nixfDuJ7OiFBUmkhmDUFEIhl D35wxlthKYRs8tBzetZEipFGdyUOwuWiuwG/BuOwuP7fPS9uP4u4EPKjA5kL/Z/V E743q50PS4L/kT3ZFyUrcisUKajAr5Gu+o6rzA6F4+QYu26iBbKewNrrb+riF1wR GKthc6W++Awt+oVyKtVNyS2QokuBFcSu5IiVsfGqJ8TmffvFBqKUUjWopmP+qiYR 8+0qwHing/S/C9S72ZxhM9DF3et1dXFuHf/69YL8/u36tyKMqy/JVhByAlc87cRI tcRGaviUttBeSw4j1Y6XrycVkhn4LzizWrqrmfCikhx26MrIeWK5JxYL -----END CERTIFICATE----- </ca>
By default, this configuration file specifies 4 VPN servers located in Singapore, Japan and US (Because I live in China). 1194 is the port number.
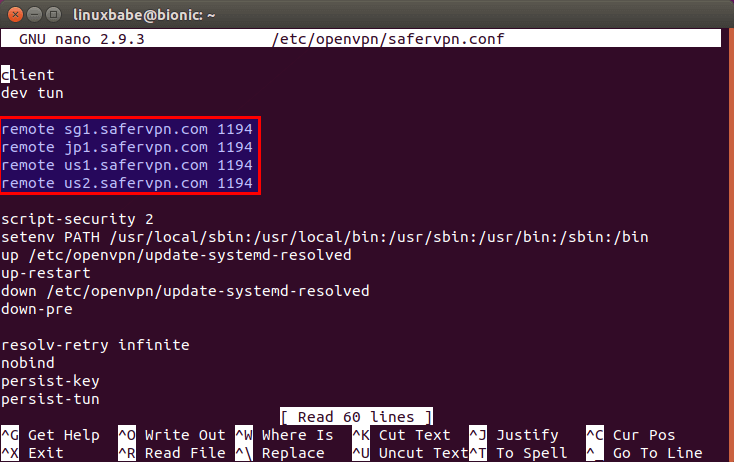
You can add as many VPN servers as you like in this file. Go to SaferVPN server list page to find additional VPN servers. For best performance, select a server close to your location. You computer will connect to the VPN server in the order you specified. Once a connection is successfully established, it will stop trying the next VPN server.
Now you can save and close this file. To save a file in Nano text editor, press Ctrl+O, then press Enter to confirm. To exit, press Ctrl+X.
To prevent DNS leak, we added the following lines to the safervpn.conf file.
script-security 2 setenv PATH /usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin up /etc/openvpn/update-systemd-resolved up-restart down /etc/openvpn/update-systemd-resolved down-pre
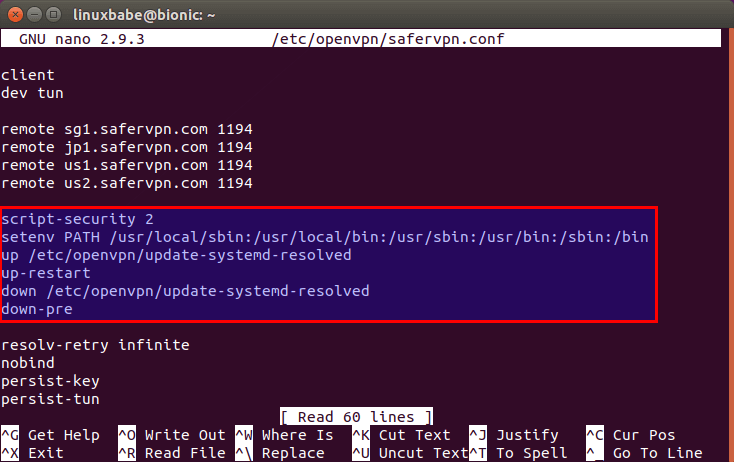
/etc/openvpn/update-systemd-resolved is a script that will parse DHCP options (including DNS servers) when connecting to OpenVPN server. This script isn’t installed on your system. To install it on Debian-based Linux distros (Debian/Ubuntu/Linux Mint/Elementary OS), run the following command.
sudo apt install openvpn-systemd-resolved
To install it on other Linux distros, simply download the script from Github to the /etc/openvpn/ directory with the following command.
sudo wget https://raw.githubusercontent.com/jonathanio/update-systemd-resolved/master/update-systemd-resolved -P /etc/openvpn/
Then make it executable with:
sudo chmod +x /etc/openvpn/update-systemd-resolved
We also need to make sure the systemd-resolved service is enabled and running.
sudo systemctl enable systemd-resolved sudo systemctl start systemd-resolved
Next, we need to specify our OpenVPN username and password in the /etc/openvpn/auth.txt file.
sudo nano /etc/openvpn/auth.txt
In this file, we enter the username and password created on SaferVPN website on two lines like below.
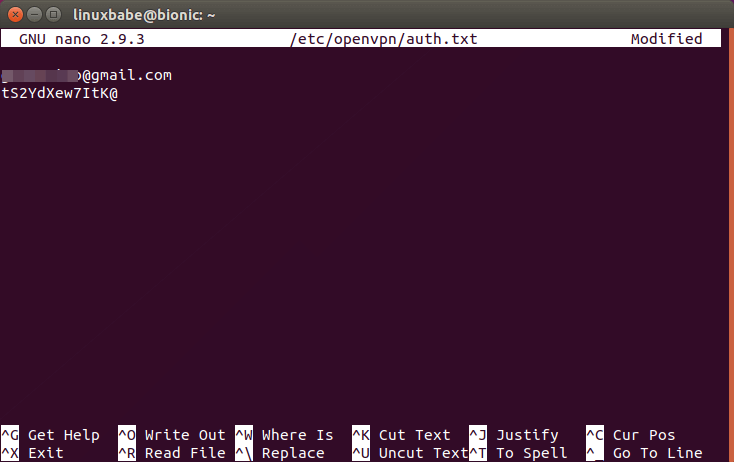
Save and close the file. Now we can run the OpenVPN client with safervpn.conf configuration file on Linux like below.
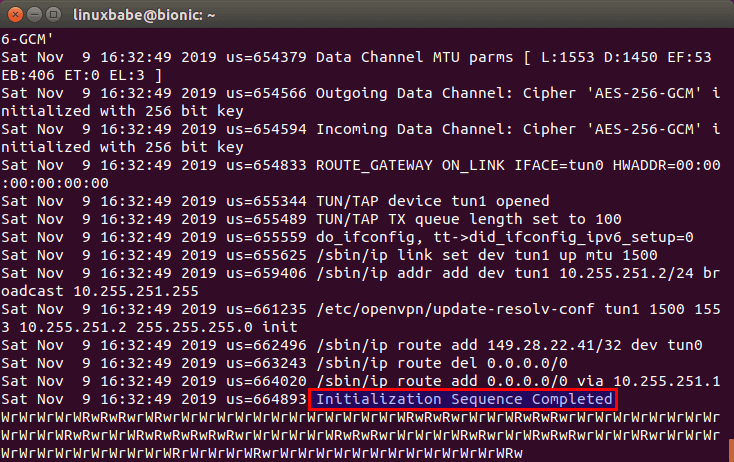
sudo openvpn /etc/openvpn/safervpn.conf
When you see the Initialization Sequence Completed message, your OpenVPN connection has been successfully established. Don’t close your current terminal window just yet, because OpenVPN is running in the foreground.
DNS Leak Test
Now go to dnsleaktest.com. You will see that your computer has got a new IP address. Click Standard test to see which DNS server you are using now.
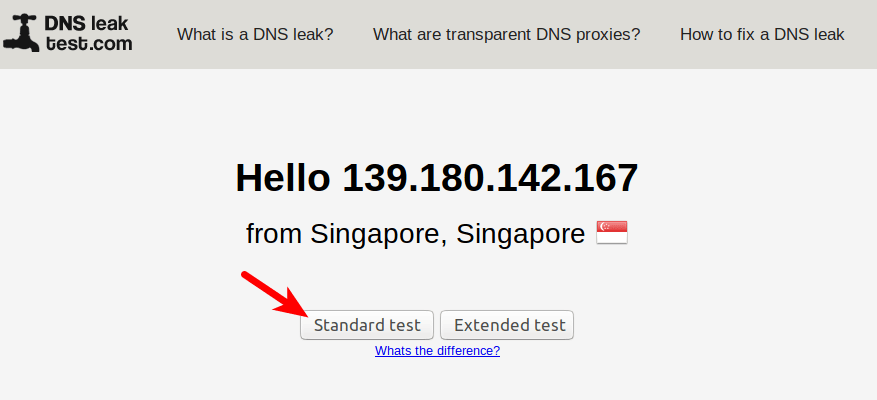
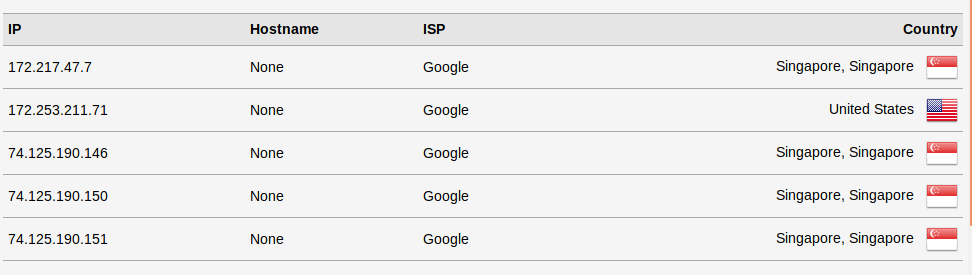
If your ISP’s DNS server shows up on the test results, then you have a DNS leak, which means you ISP’s DNS server is translating domain names to IP addresses for you. Although your connection is encrypted by VPN, your ISP knows which websites you are visiting.
Because we use the update-systemd-resolved script in the OpenVPN configuration file to prevent DNS leak, you will see you are not using your ISP’s DNS server, which means your ISP doesn’t know which websites you are visiting and can’t see what you are browsing online. Please note that SaferVPN by default uses Google DNS server, but Google doesn’t know it’s you who is sending DNS requests. Google only know that SaferVPN’s server is sending DNS requests.
If you still see your ISP in the test result, it’s probably because the /etc/resolv.conf file isn’t managed by systemd-resolved service on your Linux distro. You can solve this problem by creating a symbolic link with the following command.
sudo ln -sf /run/systemd/resolve/stub-resolv.conf /etc/resolv.conf
Then restart systemd-resolved service.
sudo systemctl restart systemd-resolved.service
Speed Test
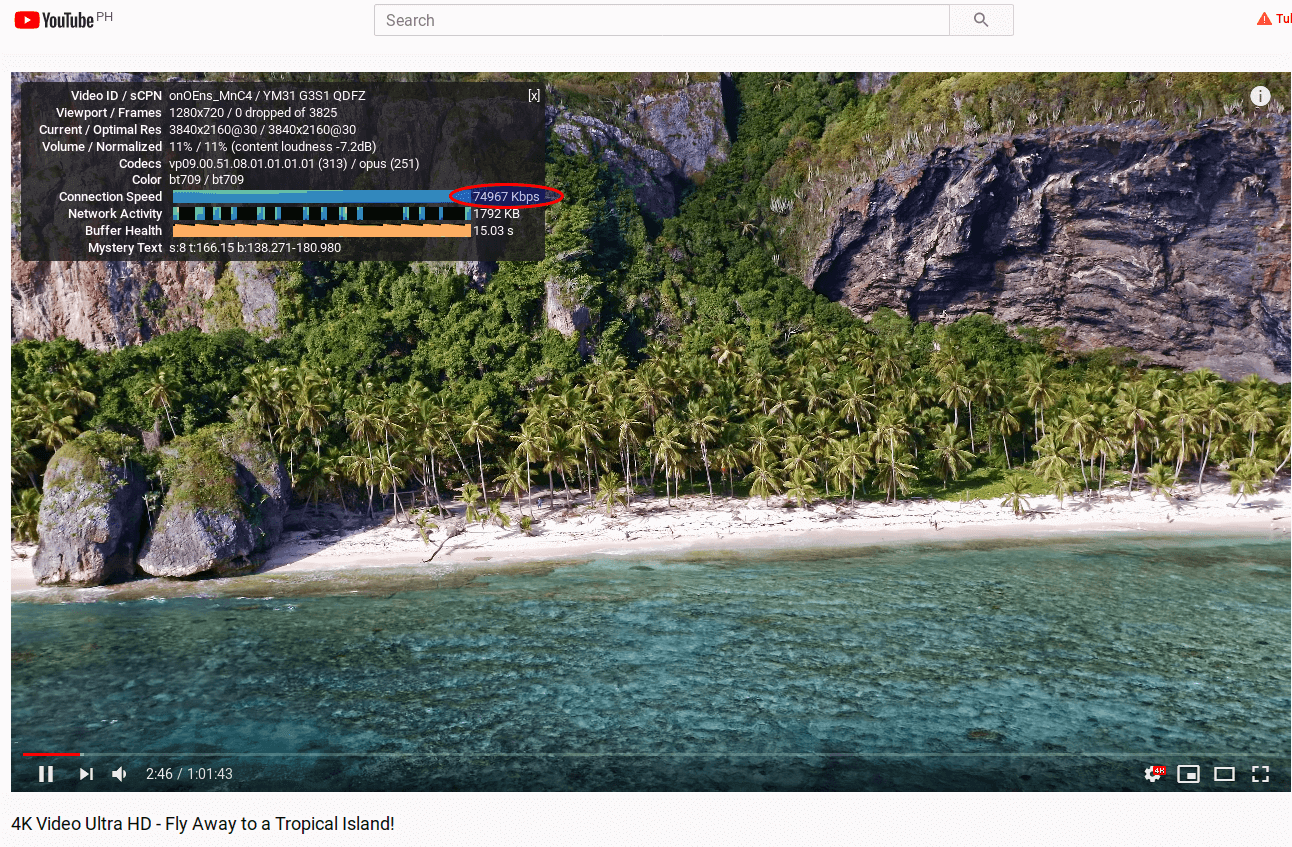
SaferVPN is pretty fast. I can watch a 4K video on YouTube at 74967 Kbps, which translates to 73.2 Mbps. This maxes out my full Internet speed. (The maximum speed of my crappy router is 75 Mbps.) You can see the YouTube connection speed by right clicking the video and select Stats for nerds.
Connect to SaferVPN OpenVPN Server At Startup
Kill the current OpenVPN connection by pressing CTRL+C in the terminal window. Then we can run the OpenVPN service in the background with the following command.
sudo systemctl start [email protected]
To connect to SaferVPN OpenVPN Server at boot time, we just need to enable this service.
sudo systemctl enable [email protected]
You need to disable the main OpenVPN service to prevent being asked about username and password at boot time.
sudo systemctl disable openvpn
If you don’t want to connect to SaferVPN at boot time, run
sudo systemctl disable [email protected]
To stop the current OpenVPN connection, use the following command.
sudo systemctl stop [email protected]
Conclusion
I hope this post helped you use SaferVPN on Linux. If you have problems when using SaferVPN, please don’t hesitate to put your question in the comments section below. As always, if you found this post useful, then subscribe to our free newsletter.



This Post is look like ADS , However you are my master and Thanks Shifu.