Set Up SSH Two-Factor Authentication (2FA) on Debian 11 Server
This tutorial will show you how to set up SSH two-factor authentication on Debian server using the well-known Google Authenticator. It will greatly improve the security of SSH service on your Debian server.
How Two-Factor Authentication Works
Normally, you only need to enter a password or use SSH key to log in to your Debian server remotely. Two-factor authentication (2FA) requires you to enter two pieces of information in order to login. So you will also need to enter a time-based one-time password to log in to your SSH server. This one-time password is computed using the TOTP algorithm, which is an IETF standard. These days many websites and services (Facebook, Google, Twitter, etc) offer 2FA for users to secure their accounts and it’s a good idea to also enable 2FA on your SSH server.
This tutorial will show you how to set up
- Password authentication with 2FA
- Public key authentication with 2FA
Note: The open-source server software we will use in this article is called libpam-google-authenticator, which is installed from the default Debian repository. Google the company does not involve in the authentication process in any shape or form. The server software and the mobile app don’t need network access.
Step 1: Install and Configure Google Authenticator on Debian Server
Log into your Debian server and run the following command to install Google Authenticator from the default Debian package repository.
sudo apt install -y libpam-google-authenticator
Then run the google-authenticator command to create a new secret key in your home directory.
google-authenticator
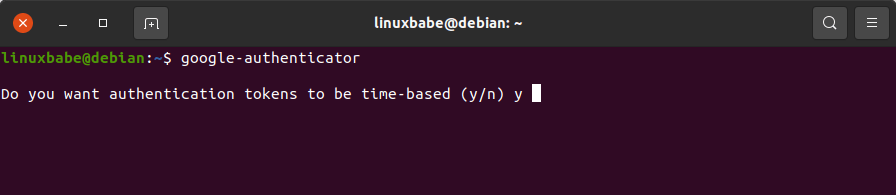
When asked “Do you want authentication tokens to be time-based?” Answer y.
Then you will see a QR code that you can scan using a TOTP app on your phone. There are two apps that I recommend:
- Google Authenticator is the most well-known TOTP mobile app. You can install it via Google Play or Apple app store on your mobile phone.
- The Google Authenticator mobile app isn’t open-source. If you don’t trust Google, you can use FreeOTP, an open-source TOTP mobile app developed by Red Hat.
Scan the QR code with Google Authenticator or FreeOTP on your mobile phone. Note that you need to enlarge the terminal window to scan the full QR code.
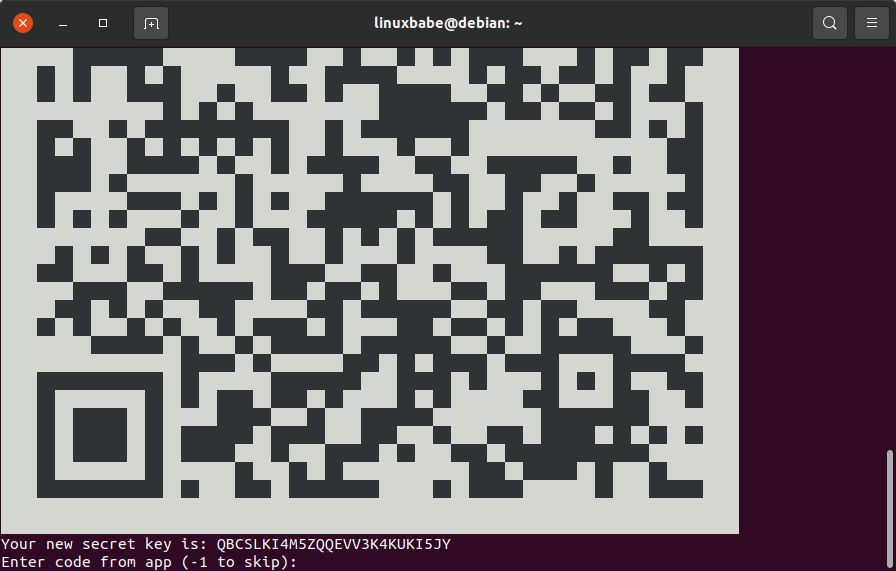
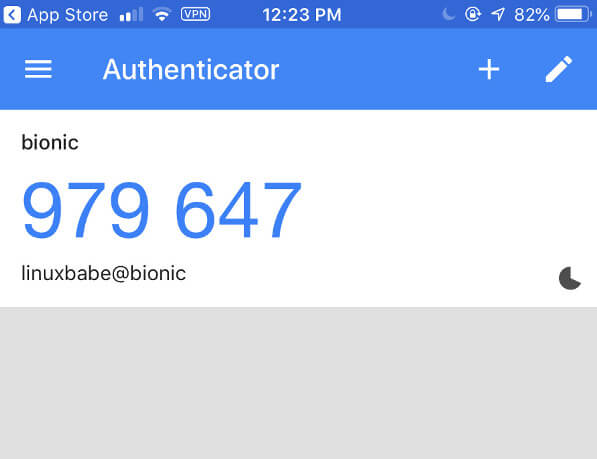
The QR code represents the secret key, which is only known by your SSH server and your TOTP mobile app. Once the QR code is scanned, you can see a six-digit one-time password on your phone. By default, it changes every 30 seconds. Enter this one-time password in the terminal window to confirm it’s correct.
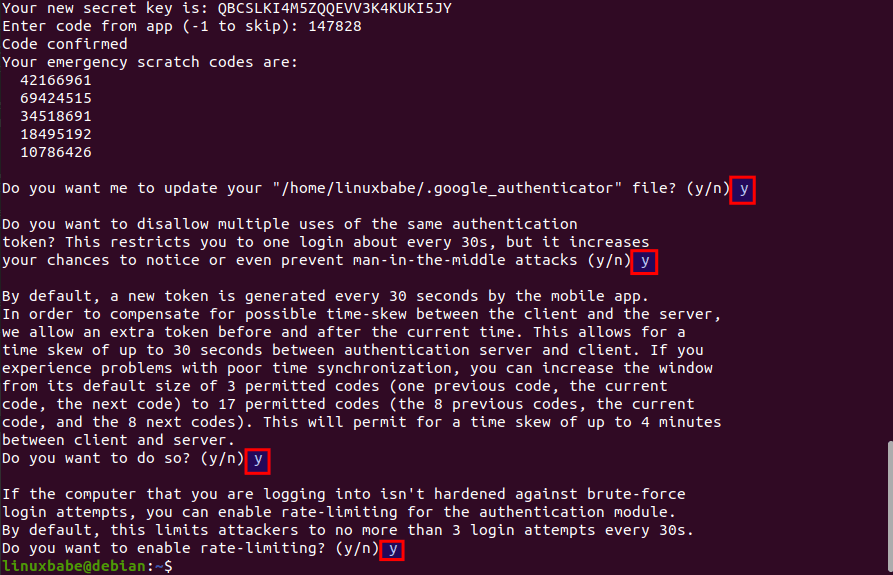
Now in the terminal window, you can see the secret key, verification code, and emergency scratch code. It’s recommended that you save this information to a safe place for later use.
Then you can enter y to answer all of the remaining questions. This will update your Google Authenticator configuration file, disable multiple uses of the same authentication token, increase the time window and enable rate-limiting to protect against brute-force login attempts.
Step 2: Configure SSH Daemon to Use Google Authenticator
- Password authentication with 2FA
- Public key authentication with 2FA
Password Authentication with 2FA
If you don’t use SSH key, then follow the instructions below.
Open SSH server configuration file.
sudo nano /etc/ssh/sshd_config
Find the following two parameters in the file and make sure both of them are set to yes.
UsePAM yes ChallengeResponseAuthentication yes
PAM stands for pluggable authentication module. It provides an easy way to plug different authentication method into your Linux system. To enable Google Authenticator with SSH, PAM and Challenge-Response authentication must be enabled.
If you want to allow the root user to use 2FA, then find the PermitRootLogin parameter and set its value to yes. It can not be PermitRootLogin no or PermitRootLogin prohibit-password.
PermitRootLogin yes
Save and close the file. Next, edit the PAM rule file for SSH daemon.
sudo nano /etc/pam.d/sshd
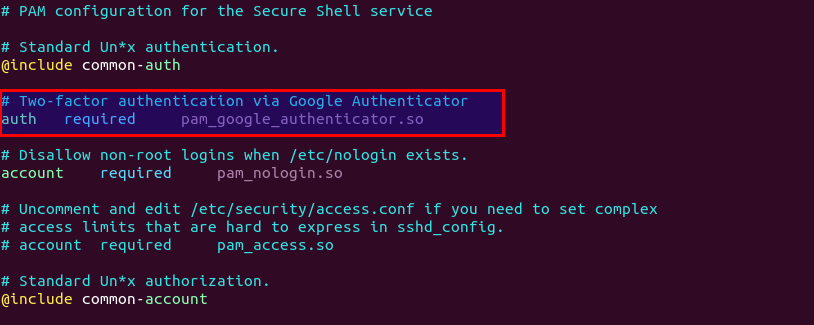
At the beginning of this file, you can see the following line, which enables password authentication when ChallengeResponseAuthentication is set to yes.
@include common-auth
To enable 2FA in SSH, add the following two lines.
# two-factor authentication via Google Authenticator auth required pam_google_authenticator.so
Save and close the file. Then restart SSH daemon for the change to take effect.
sudo systemctl restart ssh
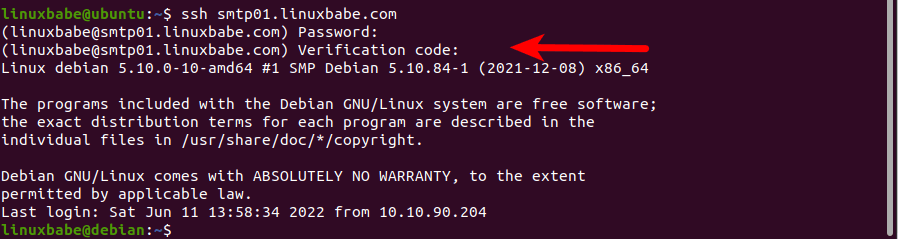
From now on SSH daemon will require you to enter user password and a verification code (the one-time password generated by Google Authenticator). Please don’t end the current SSH session. You should open another terminal window to test two-factor authentication. In case something goes wrong, you can use the first SSH session to fix errors.
The following screenshot shows an SSH login session from a Ubuntu desktop computer to a Debian server.
Public Key Authentication with 2FA
If you use SSH key to log into SSH server, then follow the instructions below.
Open SSH server configuration file.
sudo nano /etc/ssh/sshd_config
Find the following two parameters in the file and make sure both of them are set to yes.
UsePAM yes ChallengeResponseAuthentication yes
PAM stands for pluggable authentication module. It provides an easy way to plug different authentication method into your Linux system. To enable Google Authenticator with SSH, PAM and Challenge-Response authentication must be enabled.
If you want to allow the root user to use 2FA, then find the PermitRootLogin parameter and set its value to yes. It can not be PermitRootLogin no or PermitRootLogin prohibit-password.
PermitRootLogin yes
Next, add the following line at the end of this file. This tells SSH daemon that the user must pass both public key authentication and challenge-response authentication.
AuthenticationMethods publickey,keyboard-interactive
Save and close the file. Next, edit the PAM rule file for SSH daemon.
sudo nano /etc/pam.d/sshd
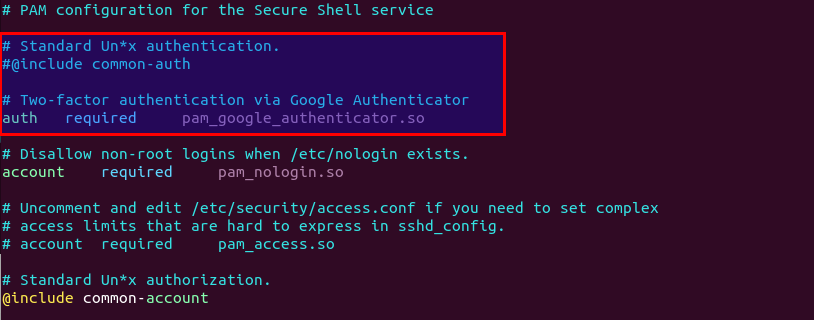
At the beginning of this file, you can see the following line, which enables password authentication when ChallengeResponseAuthentication is set to yes. We need to comment this line out, because we will use SSH key instead of password.
@include common-auth
To enable 2FA in SSH, add the following two lines.
# two-factor authentication via Google Authenticator auth required pam_google_authenticator.so
Save and close the file. Then restart SSH daemon for the change to take effect.
sudo systemctl restart ssh
From now on you need to use SSH key and Google Authenticator verification code to log in. Please don’t end the current SSH session. You should open another terminal window to test two-factor authentication. In case something goes wrong, you can use the first SSH session to fix errors.
Notes
- Each user on your Debian server needs to run
google-authenticatorcommand and scan QR code in order to use two-factor authentication. If the user didn’t set up and tries to login, the error message “Permission denied (keyboard-interactive)” will be displayed. - Emergency Scratch Code is your backup code. If you lose your phone, you can enter one of five emergency scratch code instead of a one-time password to complete the two-step verification. These codes are for one-time use only.
- If you want to change the secret key, simply log into your server and run
google-authenticatorcommand again to update the~/.google_authenticatorfile. - Since the one time password is computed using the shared secret key and the current time, so it’s a good idea to enable NTP time synchronization on your Debian server to keep accurate time, although previously we have allowed a time skew of 4 minutes between the Debian server and the mobile app. Your Debian server and the TOTP mobile app can use different time zones.
How to Disable SSH Two Factor Authentication
Edit the PAM rule file for SSH daemon.
sudo nano /etc/pam.d/sshd
Comment out the following line.
auth required pam_google_authenticator.so
Save and close the file. If you added the following line in /etc/ssh/sshd_config file,
AuthenticationMethods publickey,keyboard-interactive
Remove the keyboard-interactive authentication method.
AuthenticationMethods publickey
Save and close the file. Then restart SSH daemon.
sudo systemctl restart ssh
Wrapping Up
I hope this tutorial helped you set up SSH two-factor authentication on Debian server 22.04 and 20.04. As always, if you found this post useful, then subscribe to our free newsletter. You can also follow us on Twitter or like our Facebook page.



Yay! 2FA for SSH.
Great security and easy to setup.
Thank you for the great instructions.
A++
New readers: Make sure to check out all the other great instructions and tutorials on Linuxbabe.com
Please make a donation to help keep LinuxBabe motivated to write more great instructions and tutorials!
LinuxBabe.com is the best place on the internet for noobs to learn Linux!
Nice guide, easy to set up, thanks for making this.
thanks for the instructions. I found them because the initial discover of 2FA for SSH was incomplete and old. I did the setup successful on Debian 12. I just would like to turn off the step entering a password before the TOTP.
My initial setup was using private/public key with the following settings in the sshd_config
Section of the sshd_config
————————————-
PasswordAuthentication no
PermitEmptyPasswords no
PermitRootLogin no
————————————
I added the two line above the PasswordAuthentication no
ChallengeResponseAuthentication yes
AuthenticationMethods publickey,keyboard-interactive
and restarted the ssh daemon, but still have to enter the password.
… and I found the solution.
in the /etc/pam.d/sshd I had to commented the line at the far top aka beginning
#@include common-auth
apuaaaaaa
Works fine! TKS…..
To enable passwords with 2FA, I had to set KbdInteractiveAuthentication yes in /etc/ssh/sshd_config, on a VPS with Debian 12 minimal
But I didn’t see that setting in this or other tutorials and don’t know why